Protect Your Business With This Seamless Firewall — Now $150 Off
Tech Republic Security
MARCH 27, 2024
DNS FireWall is an intuitive security app built to protect you and your business from malware, phishing, botnets and more security threats.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

eSecurity Planet
NOVEMBER 10, 2023
DNS security protects the domain name system (DNS) from attackers seeking to reroute traffic to malicious sites. Since a majority of business IT traffic now accesses or passes through the internet, DNS plays an increasingly important — and vulnerable — role. in the DNS cache for more efficient delivery of information to users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JANUARY 5, 2024
A firewall policy is a set of rules and standards designed to control network traffic between an organization’s internal network and the internet. Featured Partners: Next-Gen Firewall (NGFW) Software Learn more Table of Contents Toggle Free Firewall Policy Template What Are the Components of Firewall Policies?
Security Affairs
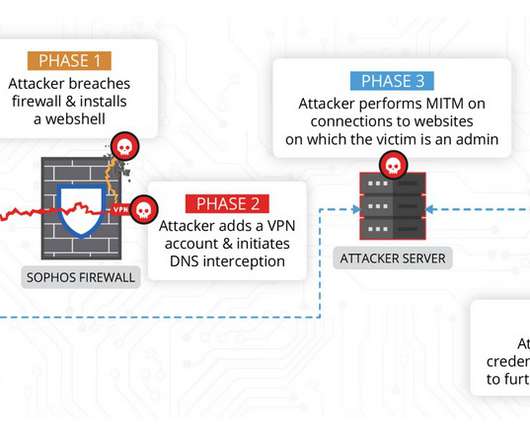
JUNE 17, 2022
China-linked threat actors exploited the zero-day flaw CVE-2022-1040 in Sophos Firewall weeks before it was fixed by the security vendor. On March 25, Sophos announced to have fixed the authentication bypass vulnerability, tracked as CVE-2022-1040, that resides in the User Portal and Webadmin areas of Sophos Firewall. MR3 (18.5.3)

The Last Watchdog
DECEMBER 6, 2019
In 2019, we’ve seen a surge in domain name service (DNS) hijacking attempts and have relayed warnings from the U.S. Cybersecurity and Infrastructure Agency, U.K.’s s Cybersecurity Centre, ICANN, and other notable security experts. Security goes beyond the firewall, not just behind it.

SC Magazine
MARCH 4, 2021
The National Security Agency (NSA) and Cybersecurity and Infrastructure Agency (CISA) released a joint information sheet Thursday that offers guidance on the benefits of using a Protective Domain Name System (PDNS). A PDNS service uses existing DNS protocols and architecture to analyze DNS queries and mitigate threats.

eSecurity Planet
FEBRUARY 14, 2024
Stateful inspection is a firewall feature that filters data packets based on the context of previous data packets. For example, a firewall performing stateful inspection may be tracking an active FTP transfer with the FTP server and show a network laptop in a Listen or Closed status. Stateless protocols (UDP, HTTP, etc.)

CyberSecurity Insiders
MAY 18, 2022
A foundational approach to cybersecurity empowers CISOs to see abnormalities and block threats before they do damage. Constantly playing catch-up seems to have become the unfortunate norm in the cybersecurity industry. So why aren’t more organizations taking advantage of protective DNS? So where do we go from here?

Security Boulevard
MAY 17, 2024
HYAS Protect protective DNS includes a user-friendly interface and four core deployment methods. Organizations of any size can monitor traffic with HYAS Protect’s cloud-based DNS resolver. DNS data from HYAS Protect allows organizations to identify their riskiest users and prioritize proactive security measures.

eSecurity Planet
APRIL 30, 2024
It’s important to prepare the network and firewalls in advance, then follow seven major steps to configure your DMZ’s protocols and rules. We recommend determining in advance every service you want to host, how many firewalls you plan to implement, and which traffic you want to allow and block.
CSO Magazine
JANUARY 19, 2021
Security researchers have found several serious vulnerabilities in dnsmasq, a utility used in many Linux-based systems, especially routers and other IoT devices, to provide DNS services. Learn 12 tips for effectively presenting cybersecurity to the board and 6 steps for building a robust incident response plan.

Webroot
APRIL 13, 2021
All of this malicious activity points to the need for a layered approach to cybersecurity. This includes essential security measures like firewalls, endpoint protection and DNS protection. This is why security awareness training with phishing simulations are increasingly important.

Cisco Security
AUGUST 12, 2021
What an experience to be attending the first major cybersecurity conference since the lockdowns of the COVID-19 pandemic. Threat hunting is a core mission of the Cisco Secure team, while monitoring the DNS activity for potentially malicious activity. The PAN firewall team observed Russian IP 45[.]146[.]164[.]110. urlscan.io.

eSecurity Planet
JUNE 21, 2022
” Also read: Cybersecurity Employment in 2022: Solving the Skills Gap. Also read: How to Get Started in a Cybersecurity Career. The Top Cybersecurity Certifications. With that advice in mind, here are 15 cybersecurity certifications particularly worth considering. IBM Cybersecurity Analyst Professional Certificate.
Webroot
MARCH 29, 2021
A firewall with the right threat intelligence embedded could have blocked communications with the command-and-control server thus preventing a Trojanized Orion install from connecting back to the attackers and stopping them from furthering the attack. Outside of the corporate firewall, it is the Wild West.

Webroot
MARCH 9, 2021
DNS (Domain Name System) is especially vulnerable. One of the most common methods of infiltration includes internet-based attacks, such as Denial of Service (DoS), Distributed Denial of Service (DDoS) and DNS poisoning. However, cybercriminals can also use legal DNS traffic surveillance to their advantage.

eSecurity Planet
DECEMBER 8, 2023
Domain name service (DNS) attacks threaten every internet connection because they can deny, intercept, and hijack connections. With the internet playing an increasing role in business, securing DNS plays a critical role in both operations and security. Everything You Need to Know.

Security Affairs
DECEMBER 22, 2021
The Cybersecurity and Infrastructure Security Agency (CISA) has announced the release of an open-source scanner for identifying web services impacted by Apache Log4j remote code execution vulnerabilities, tracked as CVE-2021-44228 and CVE-2021-45046. Supports DNS callback for vulnerability discovery and validation.

eSecurity Planet
JULY 25, 2022
The domain name system (DNS) is basically a directory of addresses for the internet. Your browser uses DNS to find the IP for a specific service. For example, when you enter esecurityplanet.com, the browser queries a DNS service to reach the matching servers, but it’s also used when you send an email. DNS spoofing or poisoning.

Security Affairs
APRIL 21, 2022
Umbrella integrates secure web gateway, firewall, DNS-layer security, and cloud access security broker (CASB) functionality to protect systems against threats. Umbrella is Cisco’s cloud-based Secure Internet Gateway (SIG) platform that provides users with multiple levels of defense against internet-based threats.

Security Affairs
MAY 16, 2023
A joint analysis conducted by industrial cybersecurity firms Claroty and O torio discovered multiple flaws in Teltonika Networks’ IIoT products that can expose OT networks to remote attacks. Experts found multiple vulnerabilities in Teltonika industrial cellular routers that could expose OT networks to cyber attacks. through 00.07.03.4

eSecurity Planet
AUGUST 22, 2023
Cybersecurity can be difficult to implement, and to make matters worse, the security professionals needed to do it right are in short supply. Organizations typically decide to outsource cybersecurity for a number of reasons: IT talent shortages make it difficult to hire and retain experienced cybersecurity professionals.

SC Magazine
MARCH 31, 2021
A company is suing Palo Alto Networks patent infringement, alleging that their proprietary technologies were used in a number of major security products and systems sold by the cybersecurity giant. Last October a judge ordered Cisco Systems to pay $1.9 The court denied Cisco a new trial earlier this week.

Security Affairs
AUGUST 1, 2019
In addition, we’re shooting for 7x24x365 uptime as we continue to scale with improved Web App Firewalls, Content Deliver Networks (CDNs) around the Globe, Faster and More Secure DNS and CyberDefenseMagazineBackup.com up and running as an array of live mirror sites. It’s mobile and tablet friendly and superfast.

Security Affairs
SEPTEMBER 4, 2019
In addition, we’re shooting for 7x24x365 uptime as we continue to scale with improved Web App Firewalls, Content Deliver Networks (CDNs) around the Globe, Faster and More Secure DNS and CyberDefenseMagazineBackup.com up and running as an array of live mirror sites. It’s mobile and tablet friendly and superfast.

eSecurity Planet
FEBRUARY 23, 2022
Invisibility sounds like something out of a fantasy novel, but if done properly, we can use it to hide computers, gateways, or individual PCs by implementing specific firewall techniques like port knocking or single-packet authorization (SPA). If we obscure an IP address, the attacker may overlook the hidden device.

CyberSecurity Insiders
MARCH 21, 2021
Therefore, make sure to set up the latest network routers and firewall protocols across all IT equipment to strengthen your security and create a defense against hackers and security breaches. Firewalls . Install hardware firewalls for the maximum level of network security. . appeared first on Cybersecurity Insiders.

Security Affairs
JULY 1, 2019
Tips, tricks, ideas, secrets and insider information on the best practices in cybersecurity. Tips, tricks, ideas, secrets and insider information on the best practices in cybersecurity. Please read it and share it with your friends. With much appreciation to our sponsors. 168 pages packed with excellent content. We hope you like it.

eSecurity Planet
JULY 7, 2023
Popular DDoS Web Analytics Tools Some popular DDoS web analytics tools include: CloudFlare Web Application Firewall Sucuri Website Firewall Azure Web Application Firewall AWS WAF Imperva Early Warning Signs of a DDoS Attack Having tools like web application firewalls and monitoring services in place are your best defense against a DDoS attack.

SC Magazine
MAY 5, 2021
Signage with logo at the Silicon Valley headquarters of computer security and firewall company Palo Alto Networks, Santa Clara, California, August 17, 2017. Some cybersecurity observers raised similar questions after Centripetal initially filed the lawsuit. Photo via Smith Collection/Gado/Getty Images).

Security Affairs
JUNE 20, 2022
Security Affairs is one of the finalists for the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS. If you want to also receive for free the newsletter with the international press subscribe here. I ask you to vote for me again (even if you have already done it), because this vote is for the final.

CyberSecurity Insiders
JANUARY 6, 2022
On top of that, new cybersecurity threats keep popping up constantly. No cybersecurity experts. Cybersecurity is a complex issue that requires comprehensive knowledge. Sadly, most companies don’t hire any cybersecurity experts. A multi-layered security approach is a defense mechanism for cybersecurity protection.

eSecurity Planet
SEPTEMBER 24, 2021
Rapid7 combines threat intelligence , security research, data collection, and analytics in its comprehensive Insight platform, but how does its detection and response solution – InsightIDR – compare to other cybersecurity solutions? Alert Logic AT&T Cybersecurity BeyondTrust Crowdstrike F-Secure Invicti LogRhythm.

eSecurity Planet
JULY 29, 2021
As social engineering tactics become more advanced, it’s important to know how to identify them in the context of cybersecurity. Social engineering in cybersecurity attacks. Whaling attacks are among the most successful cybersecurity attacks because they target a narrow pool of C-level executives.

CyberSecurity Insiders
JUNE 29, 2023
Executive summary Credential harvesting is a technique that hackers use to gain unauthorized access to legitimate credentials using a variety of strategies, tactics, and techniques such as phishing and DNS poisoning. Incident response is an organizational approach and process to manage cybersecurity breaches, incidents, or cyberattacks.
Security Affairs
MARCH 22, 2020
. “On March 16th I have found an unprotected and thus publicly available Elasticsearch instance which appeared to be managed by a UK-based security company, according to the SSL certificate and reverse DNS records.” “Our extensive cybersecurity knowledge lends itself well to searching for and analyzing data leaks.

Security Boulevard
MARCH 3, 2023
To be fair, the cybersecurity community has made ongoing efforts to mitigate the phishing threat by instructing users how to avoid them by following some basic rules, such as manually typing in the URL of a company's website rather than simply clicking the first link that appears after performing a search with Google. Next-gen protective DNS.

eSecurity Planet
MARCH 15, 2021
Also Read: Microsegmentation: The Next Evolution in Cybersecurity . Ten years after the conceptual roots of zero trust, the cybersecurity industry has four methods for implementing microsegmentation: network fabric, hypervisor, agent, or NFGWs. Raise Next-Generation Firewalls . Approaches to microsegmentation.

SiteLock
AUGUST 27, 2021
With cyberthreats increasing in variety, protecting your website is no longer about installing a basic firewall. To help you start your own deployment, below are three non-firewall add-ons that you should have in order to develop a comprehensive website security plan. Add-Ons That Help Website Security. CDN Deployment.

SC Magazine
MAY 18, 2021
Companies transitioning to the cloud have to think of cybersecurity as more than firewalls, access controls and incident response, and define goals of security that go beyond confidentiality, integrity and availability, said Randy Vickers, chief information security officer for the U.S. Sean Gallup/Getty Images). Technical review.

eSecurity Planet
MAY 25, 2022
Intrusion detection system (IDS) and intrusion prevention system (IPS) technologies – often combined as intrusion detection and prevention (IDPS) – have been in use for decades, yet they remain important cybersecurity tools even in the face of today’s rapidly changing cyber threats and complex IT environments.

Malwarebytes
FEBRUARY 10, 2023
At the end of January, the Health Sector Cybersecurity Coordination Center warned that the KillNet group is actively targeting the US healthcare sector with distributed denial-of-service (DDoS) attacks. The Cybersecurity and Infrastructure Security Agency (CISA) says it helped dozens of hospitals respond to these DDoS incidents.
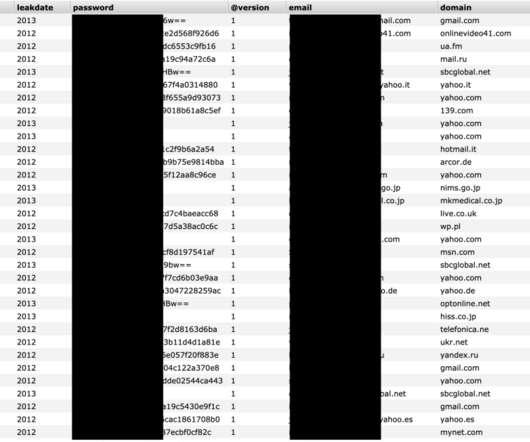
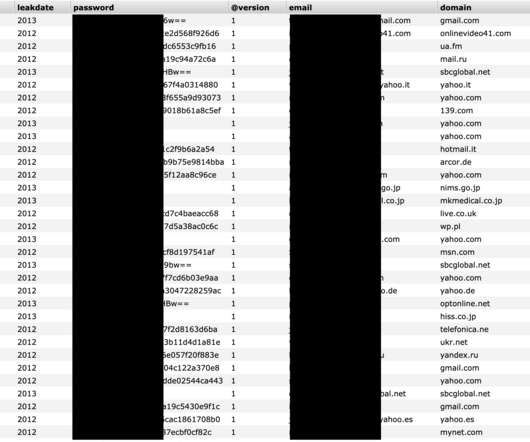
Security Affairs
MARCH 22, 2020
Expert discovered an Elasticsearch instance belonging to security firm Keepnet Labs containing over 5 billion records of data leaked in previous cybersecurity incidents. The firewall was temporarily disabled for roughly 10 minutes during the migration, which allowed the search engine to index the database. ” concludes the expert.

McAfee
FEBRUARY 4, 2021
And they didn’t even give it a DNS look up until almost a year later. The majority of this tactic took place from a C2 perspective through the partial exfiltration being done using DNS. When protection fails, it could be a firewall rule that can be any type of protection. This is continuity planning.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content