How to Mitigate DDoS Attacks with Log Analytics
CyberSecurity Insiders
APRIL 30, 2021
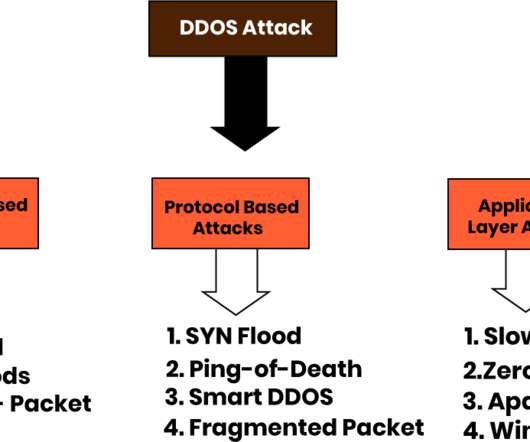
Is your organization prepared to mitigate Distributed Denial of Service (DDoS) attacks against mission-critical cloud-based applications? A DDoS attack is a cyber attack that uses bots to flood the targeted server or application with junk traffic, exhausting its resources and disrupting service for real human users. Source: Testbytes.

















Let's personalize your content