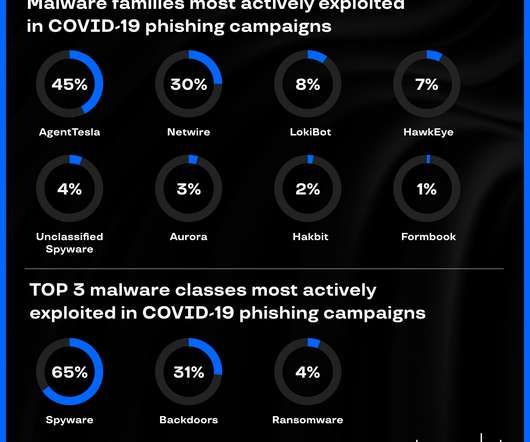
Phishers prefer Tesla, top 3 malware strains in Coronavirus phishing campaigns
Security Affairs
APRIL 9, 2020
Group-IB’s CERT-GIB analyzed hundreds of coronavirus -related phishing emails and discovered top malware strains in COVID-19 campaigns. Group-IB’s Computer Emergency Response Team ( CERT-GIB ) analyzed hundreds of coronavirus-related phishing emails between February 13 and April 1, 2020. Spyware: the most likely COVID-19 payload.














Let's personalize your content