Apple Warns Users of Targeted Spyware Attacks – Here’s How to Stay Safe
Penetration Testing
APRIL 11, 2024
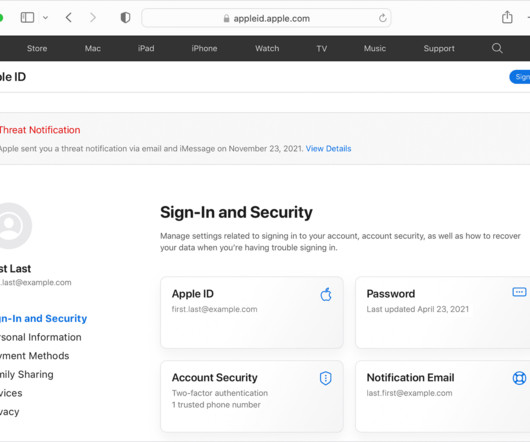
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Penetration Testing
APRIL 11, 2024
Apple has sent warnings to a growing number of users, alerting them about highly sophisticated mercenary spyware attacks.

SecureList
FEBRUARY 16, 2023
Short-lived phishing sites often offered to see the premieres before the eagerly awaited movie or television show was scheduled to hit the screen. Thus, during the World Cup a brand-new scam appeared: it offered users to win a newly released iPhone 14 for predicting match outcomes.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Malwarebytes
FEBRUARY 16, 2021
When COVID-19 cases first began spiking in several countries, cybercriminals preyed upon people’s fears mercilessly, with an avalanche of coronavirus phishing emails and scams. And as people adapted to their “new normal,” scammers exploited their isolation with a resurgence in tech support scams.

BH Consulting
OCTOBER 6, 2022
Is it just us, or is phishing everywhere right now? Banks and insurance companies are telling customers to be wary of scam messages. Social engineering techniques, such as phishing, target not the systems but the people using them. Social engineering techniques, such as phishing, target not the systems but the people using them.
SecureList
FEBRUARY 15, 2021
The Kaspersky Anti-Phishing component blocked 434,898,635 attempts at accessing scam sites. The most frequent targets of phishing attacks were online stores (18.12 The contact phone trick was heavily used both in email messages and on phishing pages. Agentb malware family. Trends of the year. Malicious links.
SecureList
FEBRUARY 9, 2022
Our Anti-Phishing system blocked 253 365 212 phishing links. Safe Messaging blocked 341 954 attempts to follow phishing links in messengers. This means the person who completes the full task not only gives the scammers money, but also recommends the scam to people in their list of contacts. Trends of the year.

Webroot
OCTOBER 25, 2021
Even strong security can’t prevent an account from being hacked if account credentials are stolen in a phishing attack, one of the most common causes of identity theft. In 2020, phishing scams spiked by 510 percent between January and February alone. Web-borne malware remains widespread.

Identity IQ
FEBRUARY 21, 2023
The trojan horse can be hidden in software or attachments that, if downloaded, install different spyware and viruses on your device. This spyware and viruses can cause many problems on your device and compromise personal details. Phishing Phishing is a very costly threat to individuals. This is a trap.

IT Security Guru
FEBRUARY 13, 2023
With so many well known banking sites falling short when it comes to blocking fraudsters, cybersecurity experts at VPNOverview have compiled a list of 12 safety tips to keep your money safe from malware and phishing scams. What are the possible dangers of online banking?

Malwarebytes
JULY 11, 2022
TikTok is “unacceptable security risk” and should be removed from app stores, says FCC Google to delete location data of trips to abortion clinics IconBurst software supply chain attack offers malicious versions of NPM packages Discord Shame channel goes phishing Verified Twitter accounts phished via hate speech warnings Apple Lockdown (..)

Malwarebytes
OCTOBER 26, 2021
Some people get so convinced they have spyware on their system that they contact our support team to help them get rid of it. Social media and scams. There are many kinds of Bitcoin scams to be found on YouTube, Twitter, and other platforms. More Facebook concerns. Every Facebook user will have seen posts like this.

Security Affairs
APRIL 24, 2022
If you want to also receive for free the newsletter with the international press subscribe here. T-Mobile confirms Lapsus$ had access its systems Are you using Java 15/16/17 or 18 in production? Patch them now!
Security Affairs
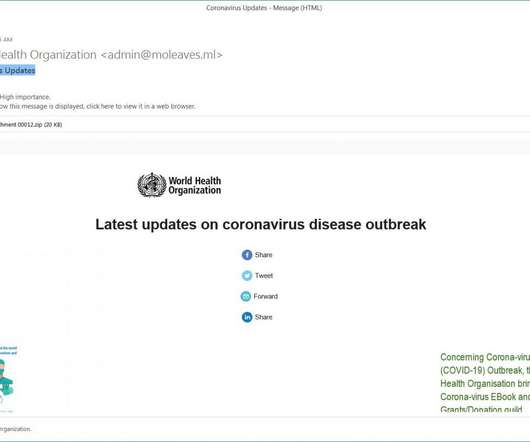
MARCH 8, 2020
The emails provide updates on the Coronavirus outbreak, it includes stats on the epidemic and contains an email of corona-virus@caramail.com that is likely used for phishing purposes. See Using Caution with Email Attachments and Avoiding Social Engineering and Phishing Scams for more information.

Hot for Security
JUNE 15, 2021
Given the portability and myriad of functionalities, mobile devices are highly susceptible to cyber threats, including malware, spyware and phishing attempts that may compromise that precious piece of tech we keep in our pocket and any information stored on it. Avoid smishing and phishing attacks.

eSecurity Planet
JUNE 16, 2022
Cisco Umbrella , analyzing the threat environment for 2022, found that 86% of organizations experienced phishing, 69% experienced unsolicited crypto mining, 50% were affected by ransomware, and 48% experienced some form of information-stealing malware. Phishing attacks continue to dominate cyber threats. Crimeware and spyware.

Identity IQ
APRIL 29, 2021
These are some ways malware can find its way into your devices: Phishing Emails. Phishing emails trick a victim into clicking on a link or opening an attachment that contains a malicious file. Spyware is software designed to capture your activity and sensitive information without your knowledge or consent. Anti-Fraud.

Identity IQ
FEBRUARY 18, 2021
A common example is phishing. Phishing is a type of social engineering attack whereby hackers send fictitious emails or other communication , from what appears to be a trusted company, to induce victims to reveal personal information such as passwords, usernames or payment details. Awareness of Phishing Scams.

Hot for Security
JUNE 14, 2021
Most security threats faced by regular users arrive via the Internet, whether it’s a malicious app or a rigged website , a scam delivered through the user’s social media channels, or a phishing scheme carried out via email or SMS. A well-timed phishing attack is all it takes to steal a user’s personal or financial information.

SecureList
MARCH 15, 2021
From targeted attacks to exploiting all things COVID-related, the biggest trends in spam and phishing. Phishing is still one of the most effective types of attacks because it exploits users’ emotions, particularly their fear and anxiety. A fake landing page for a mask advertised in a phishing email. Lessons learned.

Malwarebytes
SEPTEMBER 27, 2021
Uber scam lures victims with alert from a real Uber number Teaching cybersecurity skills to special needs children with Alana Robinson: Lock and Code S02E18. Other cybersecurity news.

Security Boulevard
MAY 3, 2021
Millions in the UK Targeted by Malware via a DHL Scam Text Message. Millions of UK citizens received a scam text message (aka smashing) which impersonated DHL in April. NCSC advice FluBot: Guidance for ‘package delivery’ text message scam . Flubot: Warning over SMS “Package Delivery” Scam Message which Delivers Android Malware.

Identity IQ
MAY 7, 2021
Once they have access to an account with sufficient authority, cybercriminals can use that trusted email address to scam other companies into making fraudulent payments or just distribute malware en mass. Research by Verizon has shown that a third of all breaches in the past year involved phishing scams.

SiteLock
AUGUST 27, 2021
You may be most familiar with computer malware such as Trojan viruses and spyware, which can be used to retrieve sensitive data from a computer or even take control of the system. Phishing attacks may be commonly associated with email scams, but they can be executed through websites as well.

SecureWorld News
APRIL 11, 2023
According to an FBI "Scams and Safety" brief , which also discusses system and data protection and protecting money information: Be careful when connecting to a public Wi-Fi network and do not conduct any sensitive transactions, including purchases, when on a public network.
Security Affairs
APRIL 9, 2020
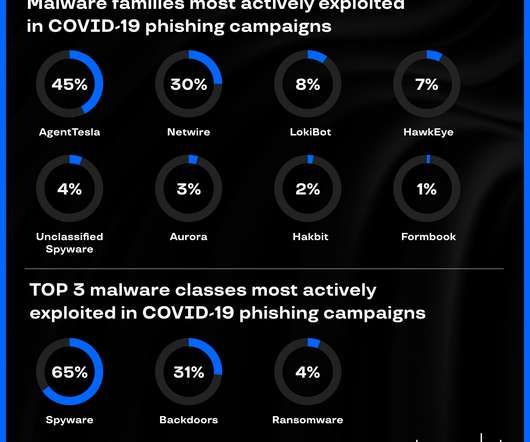
Group-IB’s CERT-GIB analyzed hundreds of coronavirus -related phishing emails and discovered top malware strains in COVID-19 campaigns. Group-IB’s Computer Emergency Response Team ( CERT-GIB ) analyzed hundreds of coronavirus-related phishing emails between February 13 and April 1, 2020. Spyware: the most likely COVID-19 payload.

SecureList
AUGUST 5, 2021
A fake notification about a Microsoft Teams meeting or a request to view an important document traditionally takes the victim to a phishing login page asking for corporate account credentials. Parcel scam: buy one, get none. Therefore, any offer to buy them is evidently a scam. Investments and public property scams.

SecureList
NOVEMBER 22, 2022
Despite these uncovered campaigns, attackers were still more likely to hunt for cryptocurrency using phishing, offering dubious cryptocurrency exchange platforms, and launching cryptojacking to illicitly mint cryptocurrency. According to the freshest data on DeFi, every hour 15 newly deployed scams against smart contracts are detected.

SecureList
NOVEMBER 1, 2021
Scamming championship: sports-related fraud. Scam: get it yourself, share with friends. million redirects to phishing pages. Spam in the name of generous philanthropists and large organizations offering lockdown compensation is already a standard variant of the “Nigerian prince” scam. Statistics: phishing.

Digital Shadows
NOVEMBER 10, 2022
Scams could present themselves in many forms. For instance, financially-motivated threat actors often plant in malicious URLs spoofing these events to fraudulent sites, hoping to maximize their chances of scamming naive internet users for a quick (illicit) profit. pro is flagged as a phishing domain by multiple security providers.

SecureList
MAY 3, 2021
Banking phishing: new version of an old scheme. In Q1 2021, new banking scams appeared alongside ones that are more traditional. Clients of several Dutch banks faced a phishing attack using QR codes. The link redirected them to a phishing page requesting their Microsoft account credentials. Quarterly highlights.
Security Affairs
MAY 8, 2020
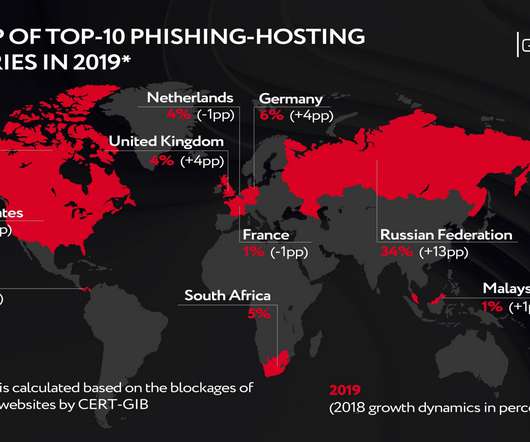
Group-IB, a Singapore-based cybersecurity company, observed the growth of the lifespan of phishing attacks in the second half of 2019. Figure 1 The distribution of web-phishing among target categories . CERT-GIB’s findings indicate that phishing attack perpetrators have revised their so-called target pool. Target reshuffle.

Malwarebytes
MAY 10, 2023
Just check out the following stats from last year: 18 percent of clicked phishing emails in 2022 came from a mobile device. Or even scarier—a backdoor could be placed or a nefarious piece of spyware. ” The number of phishing sites targeting mobile has shot up by 50 percent from 2019 to 2021. . And the kicker?

Spinone
NOVEMBER 1, 2019
Spyware – malware that spies on the computer to collect the information about a product, a company, a person. The most widespread spyware are keyloggers and trojans. Phishing – a wide range of scams when someone impersonates themselves as trustworthy entities in an attempt to obtain information. You did it!

Tech Republic Security
AUGUST 16, 2023
This exclusive bundle includes online dark web monitoring and identity theft support, so don't miss out on this discounted year-long subscription.
Security Affairs
NOVEMBER 11, 2023
Police seized BulletProftLink phishing-as-a-service (PhaaS) platform Serbian pleads guilty to running ‘Monopoly’ dark web drug market McLaren Health Care revealed that a data breach impacted 2.2 Virtual Kidnapping: AI Tools Are Enabling IRL Extortion Scams How a ‘Refund Fraud’ Gang Stole $700,000 From Amazon Info from 5.6

SecureList
MARCH 1, 2021
The word “covid” in various combinations was typically used in the names of packages hiding spyware and banking Trojans, adware or Trojan droppers. For example, an attacker could log in to a victim’s Facebook account and post a phishing link or spread spam. Pandemic theme in mobile threats. apk and coviddetect.apk.

CyberSecurity Insiders
JANUARY 31, 2021
Cybercriminals often leverage social engineering tactics like phishing and spear-phishing to propagate sophisticated malware. It is not unusual to have your system or network infected with malware, such as spyware, that often lingers secretly with no apparent symptoms. Don’t worry though. Common Types of Malware. Ransomware.

Malwarebytes
AUGUST 25, 2022
In the first half of the year, we observed spiking detections of threats associated with tech support scams. These threats install applications on the system that create fake error messages, urging the user to call a "help center" that is, in reality, a scam operation. United States manufacturing family threat detections pie chart.

Webroot
MAY 12, 2021
Bitcoin scams. We observed targeted and localised bitcoin scams promising riches and asking users for banking details. We observed convincing ads and websites that link directly to fake news sites or feature local(ised) celebrities and politicians selling scams. A fake AV scam claiming to have found threats on your machine.

eSecurity Planet
SEPTEMBER 29, 2021
Integrated one-on-one Spyware HelpDesk support. They provide a first line of defense against fake, scam, phishing and spoofed websites, created to harm devices, compromise security, and even steal personal information. Anti-phishing, spam and fraud prevention. Rapid malware scan for quick and easy detection of threats.

SecureList
MARCH 7, 2024
To get access to the content (or contest), phishing sites prompted the victim to sign in to one of their gaming accounts. If the victim entered their credentials on the phishing form, the account was hijacked. Alongside the usual get-rich-doing-nothing and paid survey scams, we encountered a few less conventional scenarios.

SecureList
NOVEMBER 10, 2021
With millions of new users on streaming platforms, cyberattackers have recognized this heightened demand and seek to take advantage of it by distributing streaming phishing scams and spreading malware under the guise of users’ favorite shows. An example of a phishing page offering to stream Money Heist. Methodology.

eSecurity Planet
JUNE 8, 2023
Email security consists of the policies, tools, and services deployed to protect against threats specific to email such as spam, phishing attacks, malware-infested attachments, impersonation, and email interception. Multi-factor Authentication Compromised credentials stolen from a phishing campaign can be quite dangerous.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content