Threat Protection: The REvil Ransomware
Cisco Security
AUGUST 11, 2021
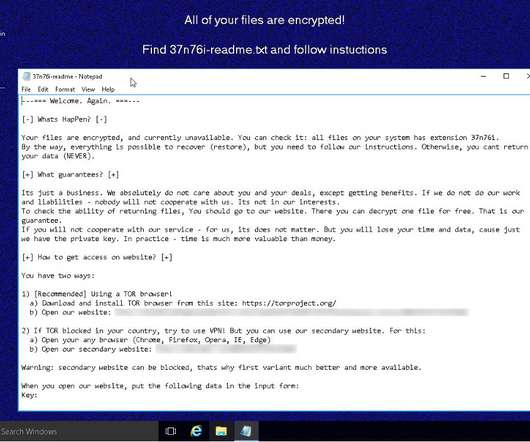
The REvil ransomware family has been in the news due to its involvement in high-profile incidents, such as the JBS cyberattack and the Kaseya supply chain attack. Yet this threat carries a much more storied history , with varying functionality from one campaign to the next. Figure 1-DNS activity surrounding REvil/Sodinokibi.



















Let's personalize your content