Scalable Security with Cisco Secure Firewall Cloud Native
Cisco Security
MAY 26, 2021
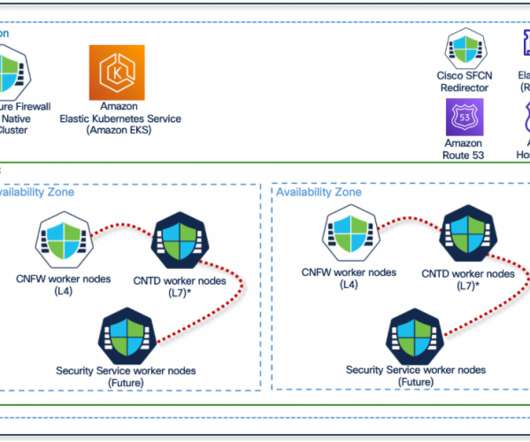
This is where Cisco Secure Firewall Cloud Native (SFCN) comes in. Cisco Secure Firewall Cloud Native brings together the benefits of Kubernetes and Cisco’s industry-leading security technologies, providing a resilient architecture for infrastructure security at scale. Kubernetes orchestrated deployment.


































Let's personalize your content