Firefox Enables DNS over HTTPS
Schneier on Security
FEBRUARY 25, 2020
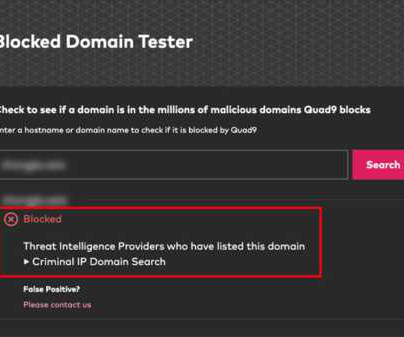
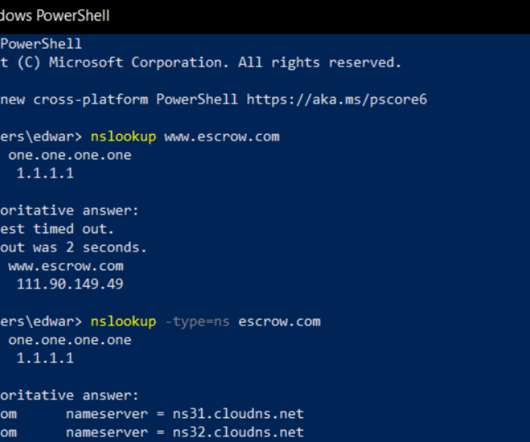
This is good news : Whenever you visit a website -- even if it's HTTPS enabled -- the DNS query that converts the web address into an IP address that computers can read is usually unencrypted. DNS-over-HTTPS, or DoH, encrypts the request so that it can't be intercepted or hijacked in order to send a user to a malicious site. [.].












































Let's personalize your content