Why Your VPN May Not Be As Secure As It Claims
Krebs on Security
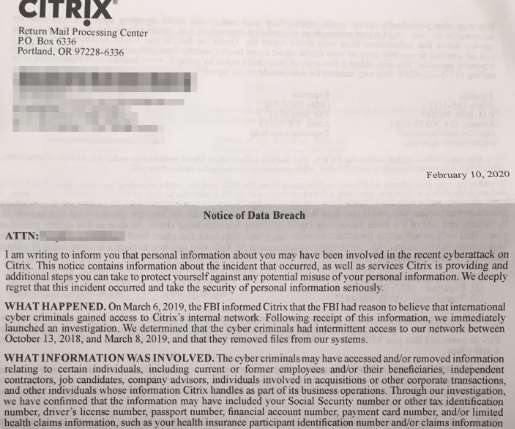
MAY 6, 2024
Virtual private networking (VPN) companies market their services as a way to prevent anyone from snooping on your Internet usage. VPNs work by creating a virtual network interface that serves as an encrypted tunnel for communications. “This is intended functionality that isn’t clearly stated in the RFC [standard]. .






































Let's personalize your content