Mass Ransomware Attack
Schneier on Security
MARCH 23, 2023
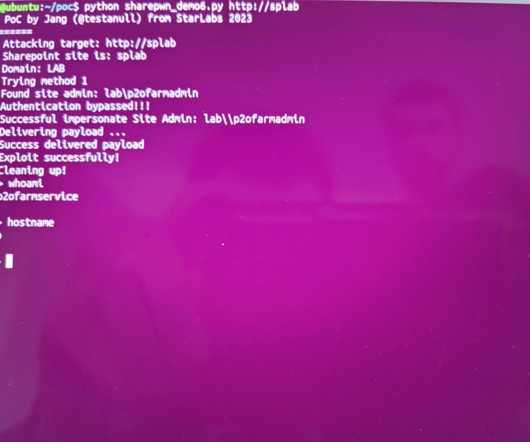
A vulnerability in a popular data transfer tool has resulted in a mass ransomware attack : TechCrunch has learned of dozens of organizations that used the affected GoAnywhere file transfer software at the time of the ransomware attack, suggesting more victims are likely to come forward. However, while the number of victims of the mass-hack is widening, the known impact is murky at best.







































Let's personalize your content