Digital Car Keys Are Coming
Schneier on Security
NOVEMBER 28, 2023
Soon we will be able to unlock and start our cars from our phones. Let’s hope people are thinking about security.

Schneier on Security
NOVEMBER 28, 2023
Soon we will be able to unlock and start our cars from our phones. Let’s hope people are thinking about security.

Tech Republic Security
NOVEMBER 28, 2023
60% of Australian small businesses don’t survive a cyber breach. What can the overworked IT pros in small businesses do with limited budgets against the cyber crime wave?
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
NOVEMBER 28, 2023
San Francisco, Calif., Nov. 28, 2023 – AppDirect , the world’s leading B2B subscription commerce platform, today released key findings from its IT Business Leaders 2024 Outlook Report. The study, conducted by independent research firm Propeller Insights, dives into how IT business leaders feel about their security posture in a world where the technologies they embrace to grow and thrive are also vulnerable to constant and increasing threats.
Tech Republic Security
NOVEMBER 28, 2023
At AWS re:Invent, NVIDIA contributed GPUs to Amazon's cloud efforts and added a retriever system to its AI Enterprise Software platform on AWS Marketplace.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.
Bleeping Computer
NOVEMBER 28, 2023
Researchers at Eurecom have developed six new attacks collectively named 'BLUFFS' that can break the secrecy of Bluetooth sessions, allowing for device impersonation and man-in-the-middle (MitM) attacks. [.

PCI perspectives
NOVEMBER 28, 2023
Risk analysis is a foundational tool to help organizations identify and prioritize potential threats and vulnerabilities within their environment. PCI DSS v4.0 introduced the concept of targeted risk analysis (TRA) with two different types of TRAs to provide entities with the flexibility to evaluate risk and determine the security impact of specific requirement controls, as appropriate for their environment.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
Security Affairs
NOVEMBER 28, 2023
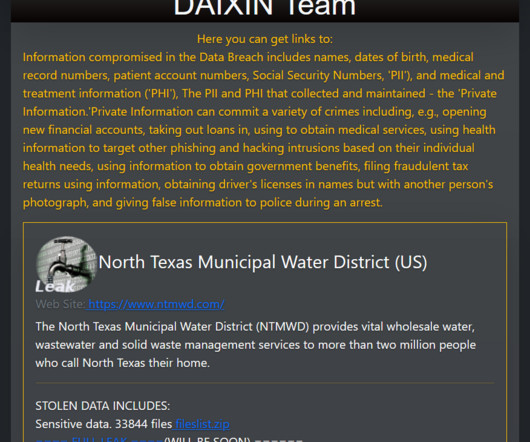
The Daixin Team group claims to have hacked the North Texas Municipal Water District (US) and threatened to leak the stolen data. The North Texas Municipal Water District (NTMWD) is a regional water district that provides wholesale water, wastewater treatment, and solid waste services to a group of member cities and customers in North Texas, United States.

Bleeping Computer
NOVEMBER 28, 2023
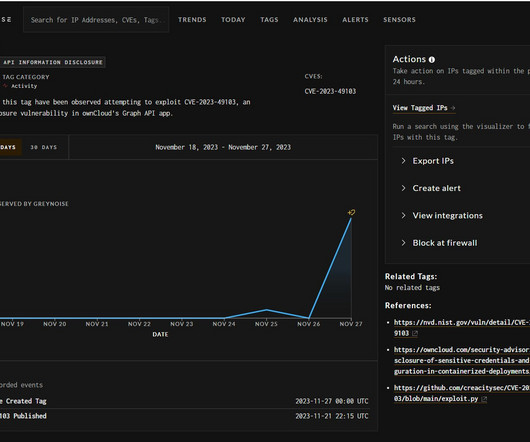
Hackers are exploiting a critical ownCloud vulnerability tracked as CVE-2023-49103 that exposes admin passwords, mail server credentials, and license keys in containerized deployments. [.

We Live Security
NOVEMBER 28, 2023
While it may be too late to introduce wholesale changes to your security policies, it doesn’t hurt to take a fresh look at where the biggest threats are and which best practices can help neutralize them

Bleeping Computer
NOVEMBER 28, 2023
Google has fixed the sixth Chrome zero-day vulnerability this year in an emergency security update released today to counter ongoing exploitation in attacks. [.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

WIRED Threat Level
NOVEMBER 28, 2023
Dozens of advocacy groups are pressuring the US Congress to abandon plans to ram through the renewal of a controversial surveillance program that they say poses an “alarming threat to civil rights.

Security Boulevard
NOVEMBER 28, 2023
Generative AI can help maintain a competitive advantage, but organizations should be mindful of the security and data privacy challenges of a new deployment. The post The Necessity of Security Best Practices When Implementing Generative AI appeared first on Security Boulevard.
Security Affairs
NOVEMBER 28, 2023
Threat actors started exploiting a critical ownCloud vulnerability (CVE-2023-49103) that can lead to sensitive information disclosure. ownCloud is an open-source software platform designed for file synchronization and sharing. It allows individuals and organizations to create their own private cloud storage services, giving them control over their data while facilitating collaboration and file access across multiple devices.

Graham Cluley
NOVEMBER 28, 2023
Warnings are spreading on social media about NameDrop, a new way for iPhone users to quickly share their contact information with others. Should you be worried, and what should you do about it? Read more in my article on the Hot for Security blog.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

Bleeping Computer
NOVEMBER 28, 2023
Google has fixed the fifth Chrome zero-day vulnerability this year in an emergency security update released today to counter ongoing exploitation in attacks. [.

Security Boulevard
NOVEMBER 28, 2023
The 32-year-old head of a threat group alleged to be responsible for ransomware attacks against corporations in 71 countries was arrested last week as part of a four-year investigation by European and U.S. law enforcement agencies. Arrested in Ukraine along with the unnamed ringleader were four other members of the group, which is accused of. The post Ringleader of Ransomware Group in Ukraine Arrested: Europol appeared first on Security Boulevard.

Security Affairs
NOVEMBER 28, 2023
An international law enforcement operation dismantled the core of a ransomware group operating from Ukraine. A joint law enforcement operation led by Europol and Eurojust, with the support of the police from seven nations, has arrested in Ukraine the core members of a ransomware group. Today EUROPOL in conjunction with the Ukraine National Police arrested individuals operating a ransomware group out of Ukraine.

Security Boulevard
NOVEMBER 28, 2023
A federal court in San Fransisco addressed whether the training of AI infringes copyright, and the decision has interesting implications for the technology's future. The post AI Gets a Legal Gift for Thanksgiving appeared first on Security Boulevard.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Security Affairs
NOVEMBER 28, 2023
The US Healthcare provider Ardent Health Services disclosed that it was the victim of a ransomware attack last week. Ardent Health Services is a healthcare company that operates hospitals and other medical facilities in the United States. It is a for-profit health system with a focus on acquiring, managing, and improving hospitals. Ardent Health Services is known for providing a range of healthcare services, including acute care, specialty care, and community health services.

Security Boulevard
NOVEMBER 28, 2023
In an era where digital assets have become an integral part of business operations, the need for a comprehensive cybersecurity plan has never been more critical. The digital realm is fraught with risks, and organizations must prioritize achieving their cyber security goals, which include protecting their valuable information and systems from unauthorized access, breaches, and … Defining Cyber Security Goals and Objectives: A Guide to Protecting Your Digital Empire Read More » The post Defining C

WIRED Threat Level
NOVEMBER 28, 2023
Musk’s recent use of the term “Q*Anon” is his most explicit endorsement of the movement to date. Conspiracists have since spent days dissecting its meaning and cheering on his apparent support.

Security Boulevard
NOVEMBER 28, 2023
Securing your organization’s information systems is a top priority in the ever-evolving digital landscape. Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks. The National Institute of Standards and Technology (NIST) Penetration Testing Framework, known as “nist pen testing,” offers a robust and structured approach to … Mastering NIST Penetration Testing: Your Essential Guide to Robust Cybersecurity Read More » The post Maste

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.

Penetration Testing
NOVEMBER 28, 2023
In the world of data visualization and business intelligence, Apache Superset stands out as a modern, enterprise-ready web application. Renowned for its speed, lightness, and intuitive design, it empowers users across various skill levels... The post Critical Vulnerabilities Found in Apache Superset: Upgrade Urged appeared first on Penetration Testing.

Security Boulevard
NOVEMBER 28, 2023
Cybersecurity incidents are more than availability problems Malicious actors are using the legal process to their advantage Personal liability for cybersecurity mishandling is becoming more common Cybersecurity incidents, once dismissed as minor disruptions, have evolved into significant threats with far-reaching consequences. Initially seen as temporary setbacks, their impact on business operations was underestimated.

The Hacker News
NOVEMBER 28, 2023
Google has rolled out security updates to fix seven security issues in its Chrome browser, including a zero-day that has come under active exploitation in the wild. Tracked as CVE-2023-6345, the high-severity vulnerability has been described as an integer overflow bug in Skia, an open source 2D graphics library.

Bleeping Computer
NOVEMBER 28, 2023
Today, Microsoft shared a temporary fix for a known issue causing Outlook Desktop to crash when sending emails from Outlook.com accounts. [.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
WIRED Threat Level
NOVEMBER 28, 2023
A WIRED analysis of more than 100 restricted channels shows these communities remain active, and content shared within them often spreads to channels accessible to the public.

Bleeping Computer
NOVEMBER 28, 2023
International logistics giant DP World has confirmed that data was stolen during a cyber attack that disrupted its operations in Australia earlier this month. However, no ransomware payloads or encryption was used in the attack. [.

Malwarebytes
NOVEMBER 28, 2023
We’ve told you about ransomware-as-a-service (RaaS) gangs ; we’ve told you about living off the Land (LOTL) attacks. What do you get when you bring the two together? Bad news. Our recent report, Threat Brief: Ransomware Gangs & Living Off the Land Attacks , takes a deep dive into why the intersection of these two threats is so dangerous. Our Threat Brief details how LOTL attacks fit in the ransomware attack chain of major gangs Ransomware gangs use LOTL attacks to carry out their malicious a

Bleeping Computer
NOVEMBER 28, 2023
The Qilin ransomware group has claimed responsibility for a cyber attack on Yanfeng Automotive Interiors (Yanfeng), one of the world's largest automotive parts suppliers. [.

Speaker: Erika R. Bales, Esq.
When we talk about “compliance and security," most companies want to ensure that steps are being taken to protect what they value most – people, data, real or personal property, intellectual property, digital assets, or any other number of other things - and it’s more important than ever that safeguards are in place. Let’s step back and focus on the idea that no matter how complicated the compliance and security regime, it should be able to be distilled down to a checklist.
Let's personalize your content