Using Generative AI for Surveillance
Schneier on Security
NOVEMBER 20, 2023
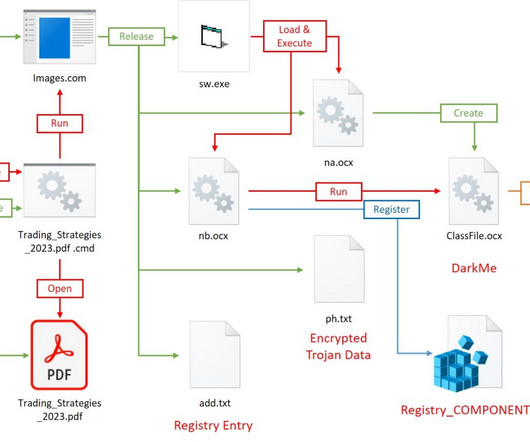
Generative AI is going to be a powerful tool for data analysis and summarization. Here’s an example of it being used for sentiment analysis. My guess is that it isn’t very good yet, but that it will get better.

























Let's personalize your content