Apple Announces Post-Quantum Encryption Algorithms for iMessage
Schneier on Security
FEBRUARY 26, 2024
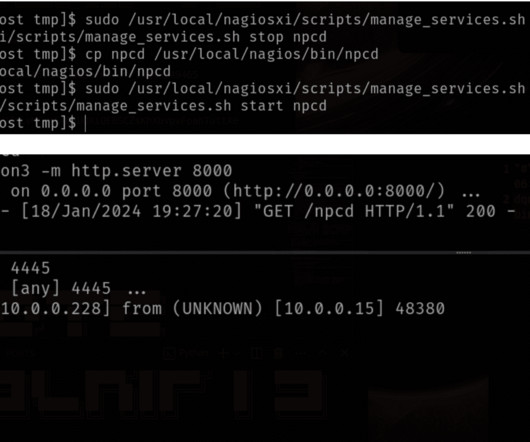
Apple announced PQ3 , its post-quantum encryption standard based on the Kyber secure key-encapsulation protocol, one of the post-quantum algorithms selected by NIST in 2022. There’s a lot of detail in the Apple blog post , and more in Douglas Stabila’s security analysis. I am of two minds about this. On the one hand, it’s probably premature to switch to any particular post-quantum algorithms.


















Let's personalize your content