Weekly Update 384
Troy Hunt
JANUARY 27, 2024
That's before we even get into the issue of whether in Trello's case, it should ever be possible for a third party to match email address to username and IRL name.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 en secure-email
en secure-email 
Troy Hunt
JANUARY 27, 2024
That's before we even get into the issue of whether in Trello's case, it should ever be possible for a third party to match email address to username and IRL name.

CSO Magazine
MAY 26, 2021
One can see the appeal: phishing tests allow security staff to craft and send emails to employees en masse that are designed to appear as authentic and enticing as the genuine malicious phishing emails that bombard businesses on a regular basis.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Troy Hunt
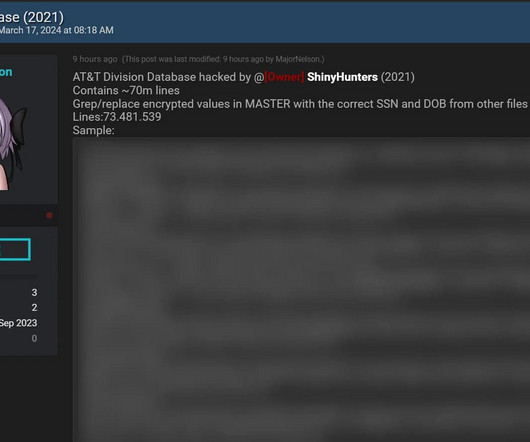
MARCH 18, 2024
From that story: From the samples shared by the threat actor, the database contains customers' names, addresses, phone numbers, Social Security numbers, and date of birth. Just by way of raw numbers, the file that aligns with the "70M" headline actually has 73,481,539 lines with 49,102,176 unique email addresses.
Security Affairs
JANUARY 4, 2024
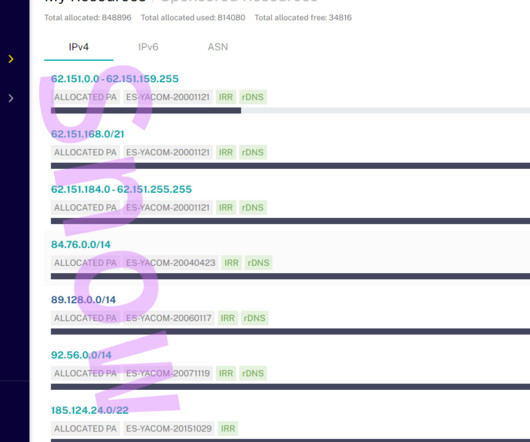
NOTA: La cuenta de Orange en el centro de coordinación de redes IP (RIPE) ha sufrido un acceso indebido que ha afectando a la navegación de algunos de nuestros clientes. RPKI adds a layer of security to BGP by cryptographically binding IP address prefixes to the entities that hold the legitimate right to advertise them.
Security Affairs
FEBRUARY 27, 2021
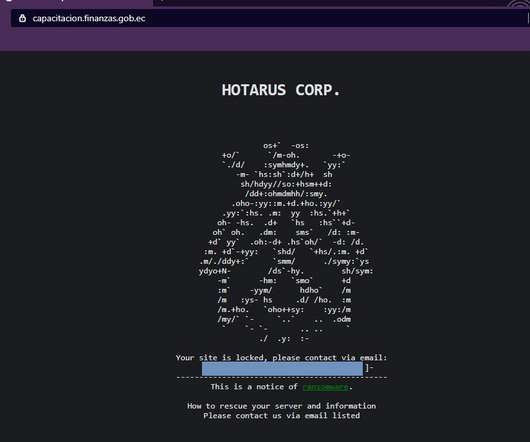
An alleged member of the @HotarusCorp leaked on a hacking forum a link to a file containing 6500 records (Email, Identity Card numbers, and passwords) that claims to Ministry of Finance. breach #infosec #deepwebnews @FinanzasEc @EcuCERT_EC pic.twitter.com/WTbXz8EYLx — Security Chronicle (@SecurChronicle) February 23, 2021.
Security Affairs
DECEMBER 15, 2023
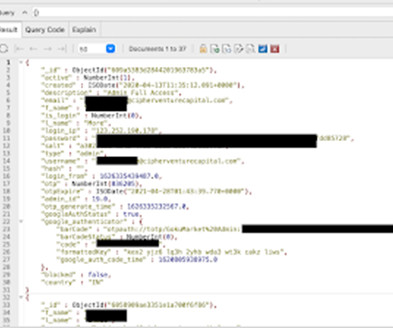
GokuMarket’s exposed database was discovered in October 2023 and secured the next day after researchers sent a responsible disclosure note. However, the database was exposed to the web for some time, which means anyone could have accessed it. Meanwhile, the open instance held a trove of sensitive data on over a million users.
SecureList
APRIL 24, 2024
.” A Singaporean guy, an Indian guy, and a German guy walk into a bar… Three identities pressure XZ Utils creator and maintainer Lasse Collin in summer 2022 to provoke an open-source code project handover: Jia Tan/Jia Cheong Tan, Dennis Ens, and Jigar Kumar. Jia I see you have recent commits. Why can’t you commit this yourself?”

Krebs on Security
AUGUST 25, 2023
Security consulting giant Kroll disclosed today that a SIM-swapping attack against one of its employees led to the theft of user information for multiple cryptocurrency platforms that are relying on Kroll services in their ongoing bankruptcy proceedings. ” A phishing message targeting FTX users that went out en masse today.
Security Affairs
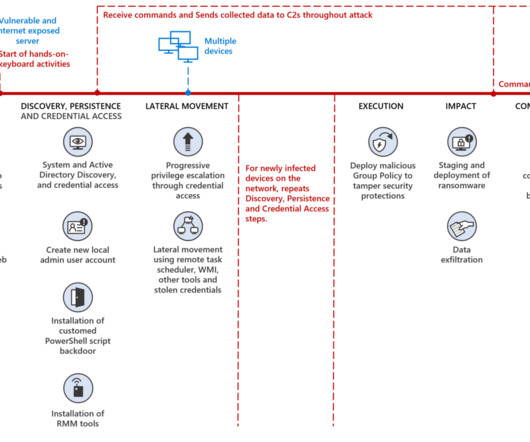
APRIL 10, 2023
MERCURY (aka MuddyWater , SeedWorm and TEMP.Zagros ) has been active since at least 2017, in January 2022 the USCYBERCOM has officially linked the Iran-linked APT group to Iran’s Ministry of Intelligence and Security (MOIS). The attackers were able to interfere with security tools using Group Policy Objects (GPO).

Security Boulevard
NOVEMBER 14, 2022
Unwanted emails steadily creeping into inboxes. of work emails are unwanted. Phishing remains the most common style of email attack, representing 39.6% The post Unwanted emails steadily creeping into inboxes appeared first on Help Net Security. Leer más Help Net Security. of work emails are unwanted.

Security Boulevard
NOVEMBER 7, 2022
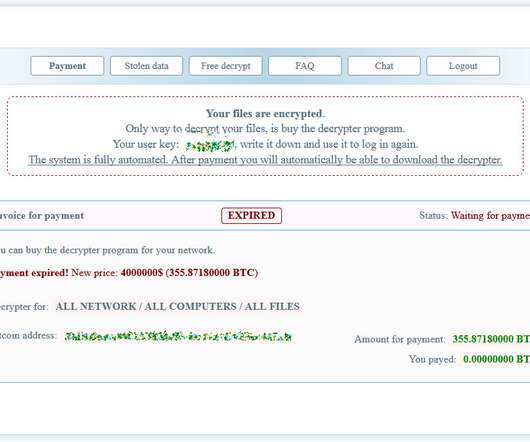
Get our morning and afternoon news emails , free app or daily news podcast Follow our Australia news liveblog for all the updates. La entrada Medibank says it won’t pay ransom for customer data stolen in cyber-attack se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP. Leer más Cybercrime | The Guardian.

McAfee
SEPTEMBER 20, 2021
Protection by ENS Module. For ENS, it’s important to have both Threat Protection (TP) and Adaptive Threat Protection (ATP) with GTI enabled. Protection by ENS Module. Preventing Exploit with McAfee ENS. Rule 312: Prevent email applications from spawning potentially malicious tools. Cobalt Strike BEACON.

Security Boulevard
NOVEMBER 23, 2022
Perception Point announced the publication of a report, “The Rise of Cyber Threats Against Email, Browsers and Emerging Cloud-Based Channels“, which evaluates the responses of security and IT decision-makers at large enterprises and reveals numerous significant findings about today’s enterprise threat landscape.
Security Affairs
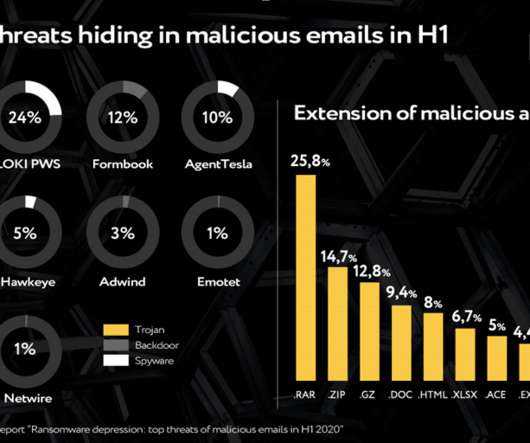
SEPTEMBER 18, 2020
Ransomware , the headliner of the previous half-year, walked off stage: only 1 percent of emails analyzed by Group-IB’s Computer Emergency Response Team (CERT-GIB) contained this kind of malware. Opened email lets spy in. Secure web- phishing. These findings confirm adversaries’ growing interest in Big Game Hunting.
Security Boulevard
NOVEMBER 10, 2022
Cory Doctorow does a great job explaining the context and the general security issues. Leer más Schneier on Security. La entrada An Untrustworthy TLS Certificate in Browsers se publicó primero en CISO2CISO.COM & CYBER SECURITY GROUP. More details by Reardon. government agencies for more than a decade.

Security Affairs
SEPTEMBER 20, 2020
Every week the best security articles from Security Affairs free for you in your email box. The post Security Affairs newsletter Round 282 appeared first on Security Affairs. A new round of the weekly SecurityAffairs newsletter arrived! Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.

Security Boulevard
NOVEMBER 6, 2022
LinkedIn Adds Verified Emails, Profile Creation Dates. The post LinkedIn Adds Verified Emails, Profile Creation Dates appeared first on Security Boulevard. Leer más Security Boulevard. The post LinkedIn Adds Verified Emails, Profile Creation Dates appeared first on Security Boulevard.

Security Boulevard
NOVEMBER 8, 2022
Among the many possible targets, new hires are particularly vulnerable to being duped by a convincing email, phone call or. The post Social Engineering Attacks on New Employees appeared first on Security Boulevard. Leer más Security Boulevard. The post Social Engineering Attacks on New Employees appeared first on Nuspire.

Security Boulevard
NOVEMBER 23, 2022
Because employees often use their business emails and cell phones as their primary point of contact, these scams quickly become a threat to employer computer systems. The post Here’s how to make sure your incident response strategy is ready for holiday hackers appeared first on Help Net Security. Leer más Help Net Security.

Security Affairs
OCTOBER 17, 2021
No somos mejores en tecnología que otros Bancos pero estamos trabajando para superar esta contingencia — FIDEL EGAS (@FEGASG) October 11, 2021. An alleged member of the @HotarusCorp leaked on a hacking forum a link to a file containing 6500 records (Email, Identity Card numbers, and passwords) that claims to Ministry of Finance.

Security Affairs
NOVEMBER 25, 2020
Group-IB supported an INTERPOL-led operation Falcon targeting business email compromise cybercrime gang from Nigeria, dubbed TMT. Group-IB , a global threat hunting and intelligence company, supported an INTERPOL-led operation Falcon targeting business email compromise (BEC) cybercrime gang from Nigeria, dubbed TMT by Group-IB.

Security Affairs
JANUARY 26, 2020
. “The state capital Potsdam has switched off the administration’s internet connection and is therefore no longer accessible by email.” “We put our systems offline for security reasons, because we have to assume an illegal cyber attack,” said Mayor Mike Schubert. ” reads the update.

CyberSecurity Insiders
JUNE 13, 2023
In our increasingly digital world, where technology permeates every aspect of our lives, cyber-security awareness has become an indispensable skill. Learn about strong password creation, multi-factor authentica-tion, secure browsing habits, and data encryption.

Security Affairs
JULY 20, 2020
The security researcher German Fernandez speculated the involvement of REvil ransomware in the attack against Telecom Argentina. Algunos sitios de #Telecom Argentina se encuentran con problemas en este momento, quizás relacionado al ataque. Many websites operated by Telecom Argentina were taken offline by the attack.

Security Affairs
SEPTEMBER 15, 2020
The British National Cyber Security Centre (NCSC) released a guideline, dubbed The Vulnerability Disclosure Toolkit, for the implementation of a vulnerability disclosure process. Having a clearly signposted reporting process demonstrates that your organisation takes security seriously. ” states the document. Pierluigi Paganini.
Krebs on Security
OCTOBER 5, 2022
Last week, KrebsOnSecurity examined a flood of inauthentic LinkedIn profiles all claiming Chief Information Security Officer (CISO) roles at various Fortune 500 companies, including Biogen , Chevron , ExxonMobil , and Hewlett Packard. We’re also exploring new ways to protect our members such as expanding email domain verification.
McAfee
APRIL 8, 2020
At McAfee, our job is to help secure the workloads and data that our customers rely on to power their business. This release of MVISION Cloud for Containers is about taking all the best practices around how these systems should be designed and giving customers a strong security foundation even in workloads as dynamic as containers.

BH Consulting
OCTOBER 6, 2022
Phishing and scam emails are – by some distance – the leading cause of ransomware infections, according to Statista. The Verizon Data Breach Investigations Report tells us that 82 per cent of security incidents have a human component. . Phishing emails or texts are precision crafted to unlock our defences.

Approachable Cyber Threats
MARCH 22, 2021
People aren’t taking the time to verify the authenticity of email senders and often click on links, open attachments, or even fill out forms without a second of thought. Phishing is a specific type of cyber attack through which hackers and scammers use email to trick you. Through phishing. What’s phishing again?” Who’s at risk?”

CyberSecurity Insiders
MAY 3, 2023
By: Craig Debban , Chief Information Security Officer, QuSecure, Inc. No, the sky isn’t falling, and the everyday use of quantum computers is not occurring en masse just yet. As you may have noticed, daily headlines around quantum computing and its impact on technologies are becoming commonplace.

Zigrin Security
APRIL 26, 2023
In this article As someone who tests web application security cautiously, Dawid discovered a vulnerability in MISP, a popular open-source platform for sharing and analyzing threat information. This is a security mechanism designed to prevent unauthorized changes to a user’s profile settings. Safari/537.36

Krebs on Security
AUGUST 5, 2019
Most often, the attacker will use lists of email addresses and passwords stolen en masse from hacked sites and then try those same credentials to see if they permit online access to accounts at a range of banks. Image: Hold Security. Only after verifying those exact amounts will the account-linking request be granted.

McAfee
OCTOBER 30, 2019
Over the past few weeks McAfee Labs has been observing a new phishing campaign using a fake voicemail message to lure victims into entering their Office 365 email credentials. McAfee Customers using VSE, ENS, Livesafe, WebAdvisor and Web Gateway are protected against this phishing campaign.
Security Affairs
SEPTEMBER 6, 2020
According to a criminal complaint published by Argentina’s Unidad Fiscal Especializada en Ciberdelincuencia, the agency started receiving numerous tech support calls from checkpoints at approximately 7 AM on August 27th. Recently the FBI has issued a security alert about Netwalker ransomware attacks targeting U.S.

Malwarebytes
SEPTEMBER 23, 2021
In just a year, they were able to steal a total of 11.72M USD (10M EUR) from hundreds of victims of phishing attacks and other fraudulent activities such as SIM swapping (also known as SIMjacking ), business email compromise (BEC) , and money muling.

Security Affairs
NOVEMBER 17, 2018
Kevin Hertz, Voxox’s co-founder and chief technology officer, wrote in an email that the company is “looking into the issue and following standard data breach policy at the moment,” and that the company is “evaluating impact.” Security Affairs – Voxox, data leak). Security Affairs – Voxox, data leak). Pierluigi Paganini.

Cisco Security
MARCH 28, 2022
As a result of it, the customers of Cisco Secure Network Analytics and Secure Endpoint using GTA get better coverage of the threat now. According to the analysis presented by Brad Duncan [2], the attack vector seems to be phishing, via an email with an attached file (1). Windows NT; Windows NT %; en-US) WindowsPowerShell/5.1.%.
Security Boulevard
SEPTEMBER 9, 2021
From my experience as a Customer Success Engineer, many people want to apply RBAC to their applications’ security findings. Each row in the file defines: A user (users are identified via their email address). The post Automating Role-Based Access Control Assignments in ShiftLeft CORE appeared first on Security Boulevard.

Security Affairs
JULY 31, 2020
In July 2018, FireEye observed a series of new attacks of the group leveraging spear-phishing emails using weaponized Word documents that attempt to deliver the UPPERCUT backdoor, also tracked as ANEL. The post EU has imposed sanctions on foreign actors for the first time ever appeared first on Security Affairs. Pierluigi Paganini.

McAfee
JANUARY 5, 2022
And even better, you found your way to ATR’s monthly security digest where we discuss our favorite vulnerabilities of the last 30 days. From a development perspective, security testing and unit tests should be leveraged to ensure the filtering you are putting in place is working the way it is intended to. Why am I here? .

Identity IQ
MAY 7, 2021
In many cases, however, the attacker simply uses compromised accounts to order amenities, as there are generally fewer security checks associated with these services. Tax documents such as W-2s and 1040s can be purchased for around $1.04, while Social Security numbers range from $0.19 These items are then typically sold for profit.

McAfee
JANUARY 17, 2020
The attacker would use spoofed Elliptic-curve cryptography (ECC) certificates for signing malicious files to evade detection or target specific hostnames to evade browser security alerts by making it appear the file was from a trusted, legitimate source. Microsoft’s security patches are available here.

SecureList
OCTOBER 20, 2021
True, web attacks are not a thing of the past yet, but with increasing browser security, attacks via this vector have become much harder. A typical infection chain looked like this: a legitimate website was compromised — just five years ago securing websites wasn’t really the done thing.

NopSec
FEBRUARY 15, 2017
Do you feel confident that everyone in your organization could identify a phishing email that contained ransomware? This information isn’t only for your security team, but also the C-suite and non-technical employees. Phishing attacks are opportunistic; generally, emails are blasted out en masse, making it a numbers game.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content