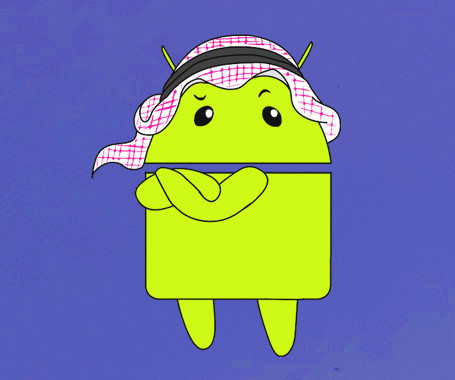
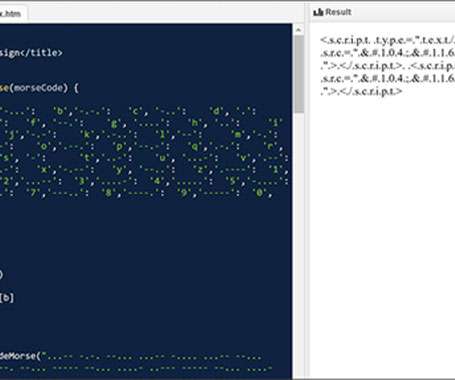
Mobile Malware Uses Deepfakes, Social Engineering to Bypass Biometric Authentication
SecureWorld News
FEBRUARY 15, 2024
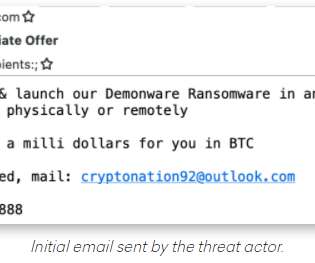
The hackers rely heavily on social engineering tactics to distribute the malware. Education on verifying app downloads, MFA, advanced threat detection, encrypted communications, and tighter mobile device management controls can all contribute to protecting users.





































Let's personalize your content