Interpol arrests 2000 criminals launching social engineering attacks
CyberSecurity Insiders
JUNE 17, 2022
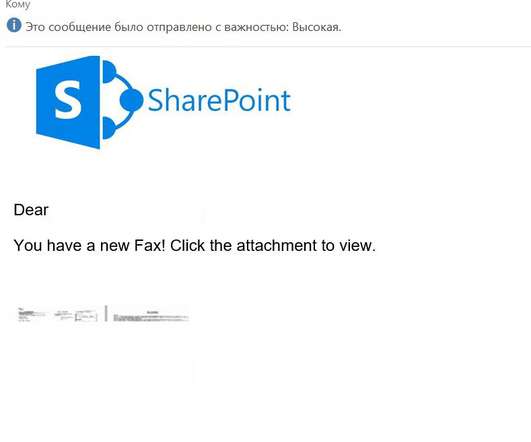
In what appears as an operation first of its kind, Interpol has arrested over 2000 criminals who launched social engineering attacks worldwide. Usually, in such scams, cybercriminals manipulate victims in the disguise of company employees or individuals. More details about the scam will be updated shortly! .






































Let's personalize your content