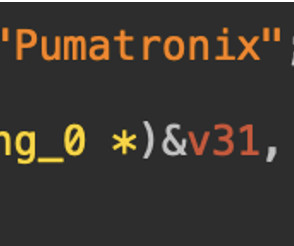
BadBox 2.0 botnet infects millions of IoT devices worldwide, FBI warns
Security Affairs
JUNE 9, 2025
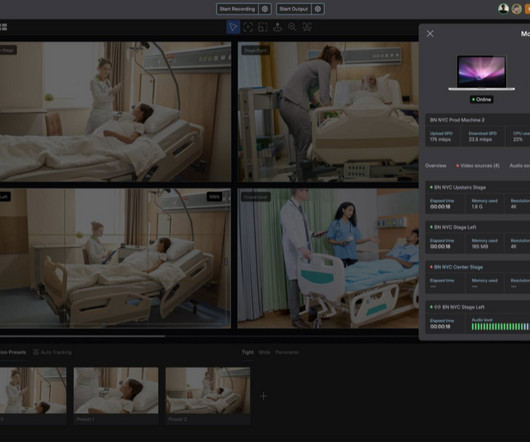
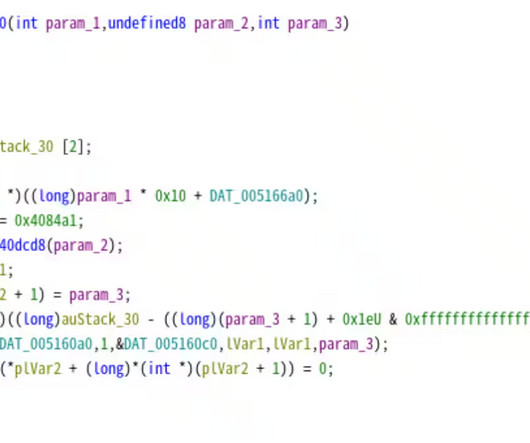
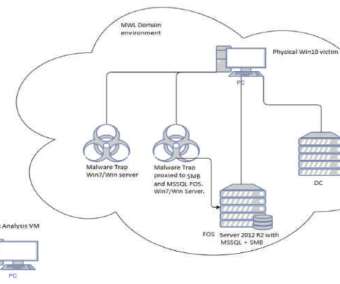
malware has infected millions of IoT devices globally, creating a botnet used for cyber criminal activities, the FBI warns. botnet to exploit IoT devices on home networks, like streaming devices, projectors, and infotainment systems, mostly made in China. “Most of the infected devices were manufactured in China.













































Let's personalize your content