I/O 2024: What’s new in Android security and privacy
Google Security
MAY 15, 2024
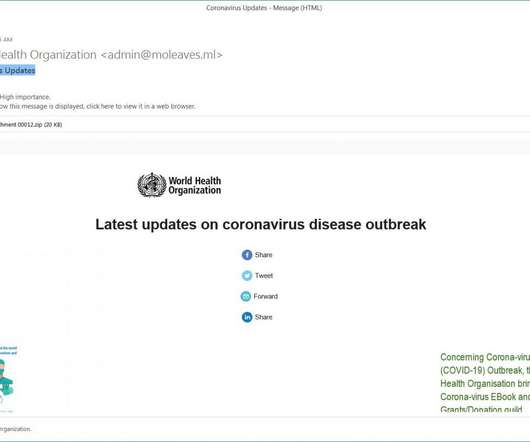
In addition to our new suite of advanced theft protection features to help keep your device and data safe in the case of theft, we’re also focusing increasingly on providing additional protections against mobile financial fraud and scams. We’re also sharing new tools and policies to help developers build safer apps and keep their users safe.
























Let's personalize your content