Why Your VPN May Not Be As Secure As It Claims
Krebs on Security
MAY 6, 2024
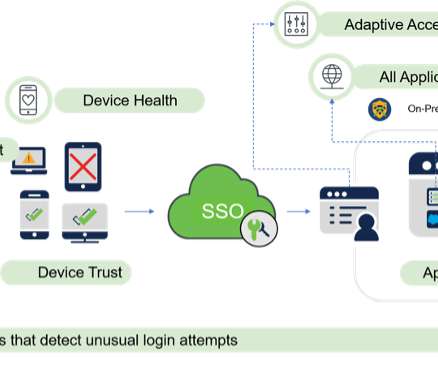
Virtual private networking (VPN) companies market their services as a way to prevent anyone from snooping on your Internet usage. ” The feature being abused here is known as DHCP option 121 , and it allows a DHCP server to set a route on the VPN user’s system that is more specific than those used by most VPNs. .”












































Let's personalize your content