Top 5 Web Application Penetration Testing Companies UK
IT Security Guru
MARCH 28, 2025
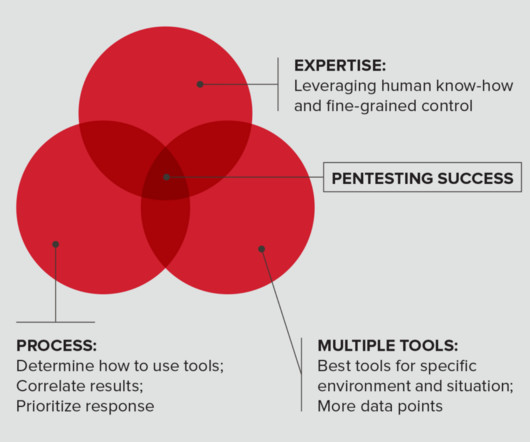
Web Application Penetration Testing (WAPT) is a methodical approach to security that involves ethical hackers simulating real-world cyber-attacks on your web application to uncover vulnerabilities. Ethical hackers perform detailed tests to pinpoint security gaps, providing businesses with the insights needed to enhance their defences.















































Let's personalize your content