Mastering NIST Penetration Testing: Your Essential Guide to Robust Cybersecurity
Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Security Boulevard
NOVEMBER 28, 2023
Organizations face an ongoing battle against cyber threats; penetration testing is a powerful weapon to avoid these risks.

eSecurity Planet
FEBRUARY 25, 2022
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing. File servers.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

eSecurity Planet
JUNE 23, 2023
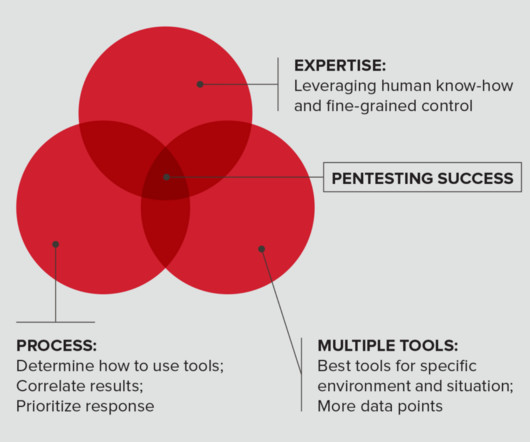
All organizations should perform penetration tests, yet many worry about not receiving the full value of their investment. Organizations have two choices: perform penetration tests with their internal teams, or hire an external vendor and find ways to lower costs.

eSecurity Planet
JUNE 28, 2023
Penetration tests are vital components of vulnerability management programs. In these tests, white hat hackers try to find and exploit vulnerabilities in your systems to help you stay one step ahead of cyberattackers. Here we’ll discuss penetration testing types, methods, and determining which tests to run.

eSecurity Planet
MARCH 7, 2023
Penetration tests are simulated cyber attacks executed by white hat hackers on systems and networks. There are different types of penetration tests, methodologies and best practices that need to be followed for optimal results, and we’ll cover those here. However, they are also the most realistic tests.

Pen Test
OCTOBER 12, 2023
Introduction Radio Frequency (RF) penetration testing, popularly referred to as RF pentesting, stands as a vital domain within ethical hacking. The rapid advancement of technology has woven a complex fabric of wireless networks, each interwoven with vulnerabilities waiting to be exposed. What is Radio Frequency (RF)?

NetSpi Executives
SEPTEMBER 5, 2023
It is transforming the way we work because of its ability to reduce the efforts and costs to complete tasks, but we are only at the beginning of this technology’s potential. AI/ML is being rapidly adopted into many aspects of businesses.
Appknox
APRIL 17, 2023
With just a few clicks, one can engage in commerce, establish a virtual hub for their services, leverage cloud technology, advertise on a massive scale, and so much more. However, we must also be cautious of its darker side - the looming risk of cyber attacks.

SecureWorld News
JUNE 28, 2020
With many organizations now planning their annual penetration tests ("pentest" for short), a change is needed in order to accommodate remote workers. It also begs what are you allowed to test versus what is now considered taboo considering end-users may be operating with their own personal equipment?

Penetration Testing
JANUARY 21, 2024
In the interconnected realm of modern technology, where devices ranging from NAS systems to next-gen routers and headless home servers become the backbone of our digital lives, the software that powers them is of... The post CVE-2024-22416: Exposing pyLoad’s High-Risk CSRF Vulnerability appeared first on Penetration Testing.

The Last Watchdog
JANUARY 2, 2024
In today’s digital landscape, organizations face numerous challenges when it comes to mitigating cyber risks. Related: How AI is transforming DevOps The constant evolution of technology, increased connectivity, and sophisticated cyber threats pose significant challenges to organizations of all sizes and industries.

CyberSecurity Insiders
MAY 3, 2023
Penetration testing (pentesting) is one of the fundamental mechanisms in this area. In contrast to this, red teaming focuses on exploiting a segment of a network or an information / operational technology (IT/OT) system over an extended period. They do overlap in quite a few ways, but each has its unique hallmarks.

eSecurity Planet
APRIL 29, 2024
Integrated risk management (IRM) is a discipline designed to embed risk considerations for the use of technology throughout an organization. In other words, it links technology spending directly to the value of the resource protected and the associated risks controlled by that technology.

NopSec
AUGUST 9, 2022
Once you’ve started a vulnerability scanning system , you may want to take the next step in identifying vulnerabilities: penetration testing, commonly referred to as pentesting. The Basics of Penetration Testing Pentesting can be as broad or narrow as the client wishes. This more closely simulates an actual cyber attack.
NetSpi Executives
APRIL 27, 2024
Table of Contents What is penetration testing? How penetration testing is done How to choose a penetration testing company How NetSPI can help Penetration testing enables IT security teams to demonstrate and improve security in networks, applications, the cloud, hosts, and physical locations.

Penetration Testing
NOVEMBER 28, 2023
In the realm of wireless communications, Bluetooth stands as a ubiquitous technology, integral to billions of devices worldwide.

eSecurity Planet
OCTOBER 31, 2023
A penetration testing report discloses the vulnerabilities discovered during a penetration test to the client. Penetration test reports deliver the only tangible evidence of the pentest process and must deliver value for a broad range of readers and purposes.

The Last Watchdog
JULY 11, 2023
Conduct regular penetration testing. Regular and thorough penetration testing is crucial for identifying vulnerabilities within trading systems. By using real-time antivirus scanning to detect and neutralize security risks as they enter the trading system, threats can be quickly identified and eliminated.
Malwarebytes
SEPTEMBER 3, 2023
By definition, a supply chain is the network of all the individuals, organizations, resources, activities and technology involved in the creation and sale of a product. An organization's security posture is its readiness and ability to identify, respond to and recover from security threats and risks. Look at best practices.

ImmuniWeb
OCTOBER 15, 2020
The data-driven and risk-based approach prevents insufficient or incomplete testing, and precludes excessive or redundant testing by leveraging award-winning Machine Learning technology.

NetSpi Executives
MARCH 19, 2024
Pairing vulnerability scanners with attack surface management (ASM) gives security teams high-fidelity analysis and prioritization of assets and exposures, while limiting noise and false positives commonly associated with technology-only platforms. See if you’re getting the most value from your penetration testing reports.
NetSpi Executives
MARCH 5, 2024
The technology creates a comprehensive view of a company’s external assets by mapping the internet-facing attack surface to provide better insight into changes and where to focus the attention of security teams. Tests often result in a lengthy list of vulnerabilities that are ranked by severity.

The Last Watchdog
AUGUST 7, 2023
LAS VEGAS — Penetration testing, traditionally, gave businesses a nice, pretty picture of their network security posture — at a given point in time. This self-service, self-directed, continuous infrastructure pentesting approach allows organization to discover their exploitable attack surfaces and reduced their risk.

The Last Watchdog
MARCH 15, 2021
When we look at society today, we can see that we are moving further and further ahead with technology. In fact, there is evidence that technology grows exponentially fast. Since we are quickly putting out large technologies, security risks always come with this. As mentioned earlier, technology is rapidly expanding.

NopSec
OCTOBER 25, 2013
So why do so many companies rely on an annual penetration test as the only safeguard against a cyber-attack? However, another reason is that the role of penetration testing in overall vulnerability risk management is not well understood. When does penetration testing apply?

Centraleyes
FEBRUARY 13, 2024
Categorizing risks as high, medium, or low has been the go-to method for organizations seeking to prioritize their cybersecurity efforts. Ten Risks in a Bed Remember the nursery rhyme? Enter the need for a more precise and actionable approach — Cyber Risk Quantification. What is Cyber Risk Quantification?

Penetration Testing
DECEMBER 15, 2023
A risk has brewed in the software world, with four critical vulnerabilities discovered in Perforce Helix Core Server, a staple platform for managing source code in industries like gaming, government, and technology.

eSecurity Planet
OCTOBER 13, 2023
Penetration testing is a critically important cybersecurity practice, but one that many organizations lack the on-staff skills to do themselves. Fortunately, there are many pentesting services out there that can do the job for them across a range of budgets and needs.

IT Security Guru
JANUARY 26, 2024
In the current digital era, technology has become an integral part of various industries, and the transport industry is not left behind. Nevertheless, the development of IoT and fleet management systems brings up issues with cybersecurity risks.

eSecurity Planet
JANUARY 12, 2021
Protecting your organization from IT security risks is an ongoing, fluid task. As a savvy tech leader, you are likely hyperfocused on performing security risk audits to keep your networks strong and protected. Components of Security Risk Assessments. Risk assessment : A risk assessment quantifies what you have to lose (i.e.,

eSecurity Planet
FEBRUARY 23, 2022
These are not uncommon risks. The devices themselves can’t be secured, but that doesn’t mean we can’t use basic IT techniques to reduce our security risks. However, before we dig into the technologies, let’s first examine why we need them. A hard-wired partner realizes a similar isolation, but uses different technology.

The Last Watchdog
FEBRUARY 8, 2024
8, 2024 – Diversified , a leading global technology solutions provider, today announced a partnership and trio of solutions with GroCyber. About Diversified : At Diversified, we leverage the best in technology and ongoing advisory services to transform businesses. Kenilworth, NJ, Feb. Vulnerability management.

The Last Watchdog
NOVEMBER 1, 2023
The new rules are designed to enhance a firm’s risk management and data protection capabilities. AdviserCyber’s primary service offering — AdviserSecure — is a comprehensive suite of technology and services that meet compliance requirements with all current and proposed SEC cybersecurity regulations.

IT Security Guru
MARCH 27, 2024
The Digital Operational Resilience Act (Regulation (EU) 2022/2554) was born from a realisation that businesses, particularly those in financial services, rely increasingly on Information and Communications Technology (ICT) and digital means to operate.

NopSec
JUNE 28, 2017
The car question is very much akin to asking “How much does a great penetration test cost ?” One man’s great penetration test is another man’s disaster. A quick search on Google for “great penetration test” yields 1,130,000 results. What’s your definition of a “great” penetration test?

Security Boulevard
JANUARY 17, 2023
When California allowed car owners to opt for “digital license plates” which could be customized to add personal messages, few who opted into the new technology suspected that they were permitting the government to track their location anywhere they were.

Zigrin Security
SEPTEMBER 13, 2023
This article is not about “How to use the benefits of AI language models while conducting penetration test”. This article is about “How to conduct a penetration test towards AI language models”. In this article you will find: The famous ChatGPT Why Should You Arrange a Penetration Test for Your AI Model as an Executive?

NetSpi Executives
MARCH 5, 2024
The technology creates a comprehensive view of a company’s external assets by mapping the internet-facing attack surface to provide better insight into changes and where to focus the attention of security teams. Tests often result in a lengthy list of vulnerabilities that are ranked by severity.

NetSpi Executives
JANUARY 8, 2024
In case you missed it, Chubb, one of the leading publicly traded property and casualty insurance companies, announced an innovative collaboration with NetSPI to strengthen client cyber-risk profiles via enhanced attack surface management and penetration testing solutions.

CyberSecurity Insiders
OCTOBER 11, 2022
The risk associated with each vulnerability is identified based on its severity score. This risk-based vulnerability assessment process cannot be an isolated, one-off event as the threat landscape constantly evolves and new vulnerabilities are discovered every day. Offers Insights into the Risks . In Conclusion.
NetSpi Executives
FEBRUARY 21, 2024
Artificial Intelligence (AI) and Machine Learning (ML) present limitless possibilities for enhancing business processes, but they also expand the potential for malicious actors to exploit security risks. Like many technologies that came before it, AI is advancing faster than security standards can keep up with.

Lenny Zeltser
AUGUST 23, 2023
You’ll help reduce risk, cut costs, and build goodwill with your colleagues. For each expense that you’d like to add to your budget, capture the following: The cost (upfront, recurring, technology, people, etc.) Help Lower Expenses While Reducing Risk The mission of the cybersecurity team involves safeguarding the organization’s data.

NetSpi Executives
MAY 1, 2024
With deep roots in penetration testing, plus consistent recognition for our people, process, and technology by global analyst firms (see: GigaOm ASM Radar Report ), NetSPI is uniquely positioned to help security teams take a proactive approach to security with more clarity, speed, and scale than ever before.

Security Boulevard
FEBRUARY 3, 2021
The usage of technology is increasing day-by-day, and so are the risks. Considering that, it is always essential to opt for penetration testing. Pen testing is a common procedure of routine security testing activities, protecting your app from hackers.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content