Watch The CyberStrong Platform Overview Video
Security Boulevard
APRIL 27, 2022
The post Watch The CyberStrong Platform Overview Video appeared first on Security Boulevard.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 platform-overview
platform-overview 
Security Boulevard
APRIL 27, 2022
The post Watch The CyberStrong Platform Overview Video appeared first on Security Boulevard.
The Hacker News
NOVEMBER 20, 2023
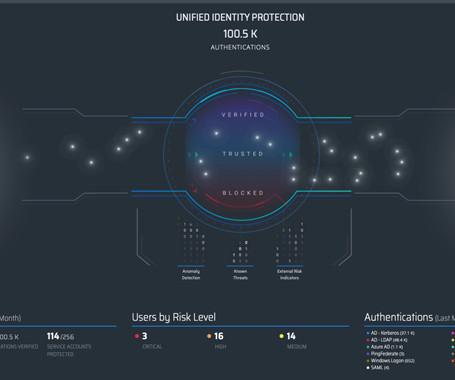
In this article, we will provide a brief overview of Silverfort's platform, the first (and currently only) unified identity protection platform on the market.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Hack the Box
NOVEMBER 2, 2023
A quick overview of the recently discovered vulnerability. Learn how you can practice exploiting (and defending against) the local privilege escalation attack on the HTB platform!

Schneier on Security
JANUARY 17, 2022
Ellis and Stevens’s research offers a historical overview of bounty programs and an analysis of contemporary bug bounty platforms — the new intermediaries that now structure the vast majority of bounty work.

The Hacker News
JANUARY 25, 2024
The information combines data from the platform's surveillance of the Surface, Deep, and Dark Web with insights derived from the in-depth research and investigations conducted by the Threat Intelligence team. The 2023/2024 Axur Threat Landscape Report provides a comprehensive analysis of the latest cyber threats.
Security Boulevard
JANUARY 8, 2024
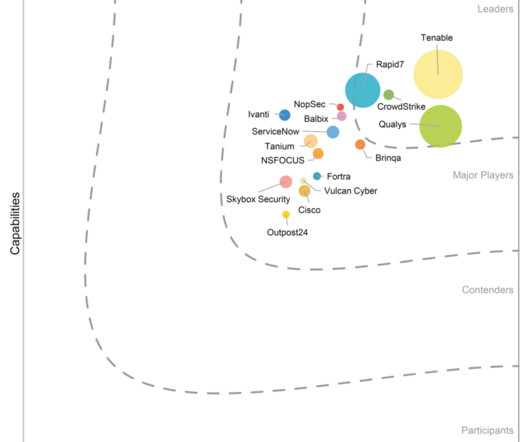
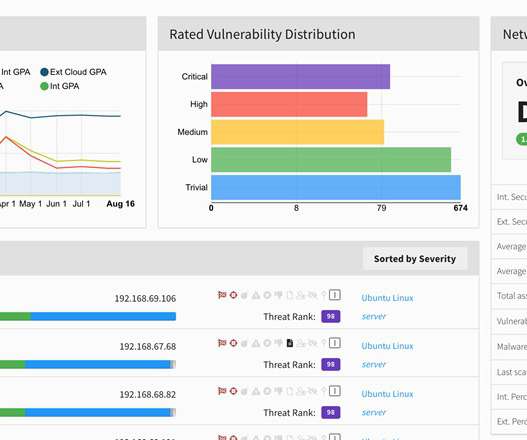
January 9, 2024 – NSFOCUS, a global provider of intelligent hybrid security solutions, today announced that NSFOCUS has been named a Major Player in the IDC MarketScape: Worldwide Risk-Based Vulnerability Management Platforms 2023 Vendor Assessment (doc #US50302323, November 2023). SANTA CLARA, Calif.,
Security Affairs
FEBRUARY 13, 2024
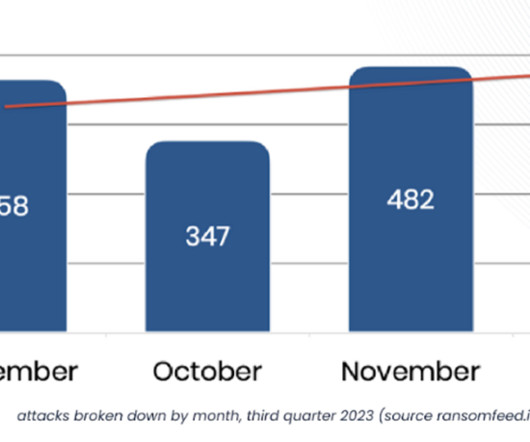
Maintainers behind the Ransomfeed platform have released Q3 Report 2023 including activities of 185 criminal groups operating worldwide. Throughout this period, the platform diligently tracked 185 criminal groups operating worldwide, meticulously tracing 342 servers employed for ransomware activities.

Security Boulevard
MAY 5, 2023
Executive Overview Illicit Telegram channels have become a growing concern in the realm of cybercrime. Telegram has been their answer, and malicious actors are increasingly moving off of Tor and onto the instant messaging platform. Threat actors want to connect with each other in fast, reliable, and “anonymous” ways.

eSecurity Planet
APRIL 24, 2019
We review the ForgeRock Identity Platform, which provides single sign-on (SSO) capabilities as well as other identity and access management features.

CSO Magazine
NOVEMBER 9, 2022
GitHub has announced new security features across its platform to help protect the software development lifecycle (SDLC). These include private vulnerability reporting, CodeQL vulnerability scanning support for the Ruby programming language, and two new security overview options.

CSO Magazine
NOVEMBER 4, 2022
Vulnerability management vendor Qualys this week announced the trial availability of its TotalCloud with FlexScan offering, an agentless, cloud-native vulnerability detection and response platform designed for use in multicloud and hybrid environments.

CyberSecurity Insiders
APRIL 28, 2021
On December 8, 2020, Kubernetes released version 1.20—the third and final release of the popular container orchestration platform in 2020. Before we do that, however, we need to cover the basics of how dockershim relates to Kubernetes and why the platform decided to deprecate the component in the first place. Read full post.

Tech Republic Security
JUNE 26, 2017
iOS and Android security has evolved from nice to have in the platforms' early days to essential. Here's an overview of iOS and Android security features, attacks, and patches through the years.

eSecurity Planet
APRIL 24, 2019
We review OneLogin Unified Access Management Platform, which scales from less than 10 users to more than 100,000.
Security Boulevard
MAY 17, 2022
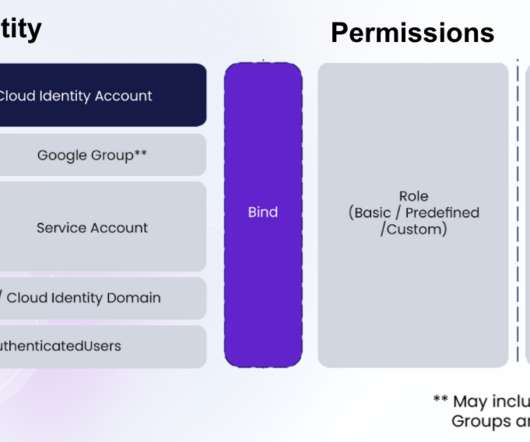
An introduction for anyone getting started with GCP or even experienced professionals who are looking for a structured overview. The post Introduction to IAM in Google Cloud Platform (GCP) appeared first on Ermetic. The post Introduction to IAM in Google Cloud Platform (GCP) appeared first on Security Boulevard.
Security Boulevard
APRIL 27, 2022
An introduction for anyone getting started with GCP or even for experienced professionals who are looking for a structured overview. The post Introduction to IAM in Google Cloud Platform (GCP) appeared first on Ermetic. The post Introduction to IAM in Google Cloud Platform (GCP) appeared first on Security Boulevard.

Dark Reading
FEBRUARY 18, 2021
In a nearly 200-page document, company offers a detailed overview of Secure Enclave and multiple other security controls in Apple silicon-based Macs and other platforms.

Security Affairs
OCTOBER 4, 2023
Our vigilant OSINT DRM platform continuously monitored 300 servers, acting as a watchful sentinel against ransomware attacks. All data was obtained through our Ransomfeed DRM platform, which scrapes data from select dark web sources. Geographical data and affected sectors provide crucial insights into emerging trends and threats.

Bleeping Computer
MARCH 9, 2021
An overview of the hacking activity on the HackerOne vulnerability coordination and bug bounty platform shows that misconfiguration of cloud resources is quickly becoming a hot target for ethical hackers. [.].

Hot for Security
APRIL 29, 2021
The Cybersecurity & Infrastructure Security Agency (CISA) and the National Institute of Standards and Technology (NIST) this week released an overview of supply chain threats. Its purpose: to help organizations keep themselves out of scenarios like the recent SolarWinds incident.

Fox IT
JANUARY 25, 2024
We will give an overview of how this library works, share the thought process and the why’s. This blog post will not cover the inner workings of the memory management of the respective platforms.
Security Boulevard
MARCH 31, 2022
In this post, we’ll provide a short overview of the two vulnerabilities. For Noname Security customers, our API Security Platform detects and blocks cyber attacks caused by Spring4Shell vulnerabilities. The Noname research team has also confirmed that the API Security Platform is not impacted by either new vulnerabilities. .

Heimadal Security
APRIL 2, 2021
Some of them are integrated into the platform your company uses on the daily, while for others you need to install additional layers of defense. The post An Overview of Traditional Email Security Solutions and How to Enhance Them appeared first on Heimdal Security Blog. Email security solutions come in many shapes and sizes.
CyberSecurity Insiders
MARCH 21, 2021
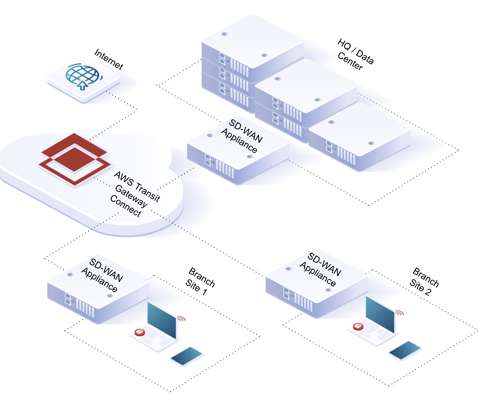
As the only SASE platform built on a Polyscale public cloud architecture, Bitglass leverages AWS Transit Gateway Connect to seamlessly integrate with SD-WAN solutions. This blog provides a short overview of how this is quickly configured and deployed. This post was originally published by Amit Singh. Read more here: [link].

Security Boulevard
AUGUST 30, 2021
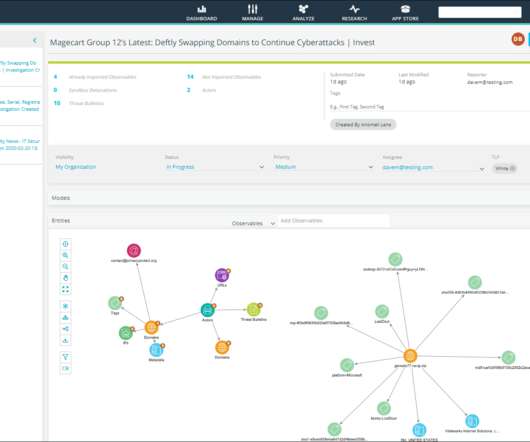
Its name is in dishonor of two actions: shopping carts, and more specifically, those that make use of the open-source ecommerce platform Magento. The post An Overview of Magecart Attacks | Avast appeared first on Security Boulevard.
eSecurity Planet
OCTOBER 18, 2021
Read more: Metasploit: Pen Testing Product Overview and Analysis. In addition, the company offers a full enterprise platform for open source security and license compliance, with support for all major software languages. Read more: Fiddler: Pen Testing Product Overview and Analysis. It scans Java, NuGet, and NPM packages.

NetSpi Executives
NOVEMBER 14, 2023
Risk Management Approach Overview – Communication is key to avoid unnecessary actions that could arise when undergoing a penetration test. This section overviews the steps the penetration testing company takes to proactively avoid potential emergency reactions in response to testing activities.

Security Boulevard
MARCH 5, 2021
This blog provides overview of end-to-end encryption and how it protects the enterprise. Over the past few years, the vulnerability of social networks like Facebook or messaging apps like Chat has given rise to using end-to-end encrypted platforms to protect communications.

The Last Watchdog
JANUARY 18, 2022
All information either stolen or taken from a system without the authorization of the platform’s owner (in other words, proactively hacked or scrapped) is considered a data breach. A quick overview of exposed data in 2021: •Almost one billion emails were exposed last year, affecting nearly 1 out of 5 internet users. •Q4

CyberSecurity Insiders
APRIL 18, 2021
Google One, an app that offers Android phone users an overview of their online storage space on its platform is reported to have bagged the certification making it the first mobile app to bag the privileged certificate in the ecosystem of applications related to Alphabet Inc’s subsidiary.

CyberSecurity Insiders
JUNE 15, 2023
Key Components of Cyberthreat Analysis Training Programs: Threat Landscape Overview: Participants gain insights into the evolving threat landscape, including common attack vectors, threat actors, and emerging trends. Understanding the current cybersecurity landscape is crucial for effective threat analysis.
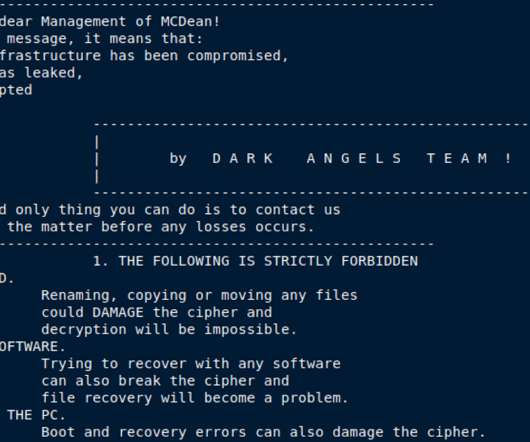
Security Affairs
SEPTEMBER 2, 2022
Technical Overview. Ransomware families targeting Linux systems or going cross-platform to target multiple OSes is not new. The ELF file we found itself is new, but the Onion link found in the ransomware binary appears to be down, indicating that this new Linux-targeted ransomware might still be under development. Conclusion.
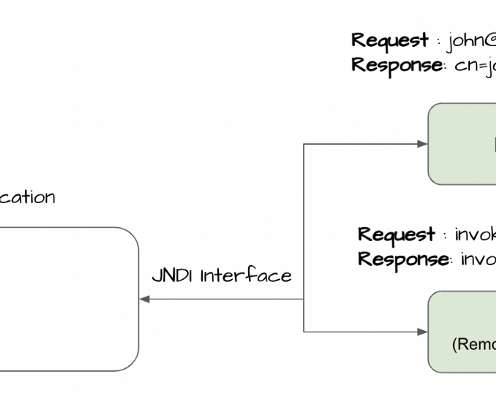
Security Boulevard
DECEMBER 11, 2021
overview of a communication flow for a Java application that utilizes JNDI. overview of a communication flow for a Java application that utilizes JNDI. overview of a attackable flow for a Java application that utilizes JNDI. overview of a attackable flow for a Java application that utilizes JNDI.
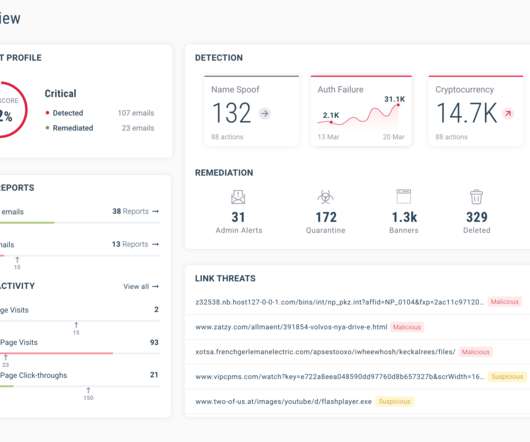
CyberSecurity Insiders
MARCH 20, 2021
Today, we are reviewing the GreatHorn Cloud Email Security Platform, an email security solution to protect organizations against phishing attacks and advanced communication threats. SOLUTION OVERVIEW. GREATHORN CLOUD EMAIL SECURITY PLATFORM BENEFITS. The platform is offered on a subscription basis with an annual term.
eSecurity Planet
FEBRUARY 8, 2023
The Anomali ThreatStream threat intelligence platform (TIP) integrates hundreds of threat information feeds with the analytics a security professional needs to understand how a specific threat might impact the organization. Anomali describes ThreatStream as “a central platform for collecting, managing, and sharing threat intelligence.

NetSpi Technical
MARCH 11, 2024
An Overview of the Vulnerability The original variant of this attack was documented by Etienne Stalmans at SensePost (Orange CyberDefense) in 2017 and leveraged VBScript code inside Outlook form objects to obtain code execution with access to a mailbox. are displayed through a form structure in an “inspector window”.

Centraleyes
APRIL 18, 2024
Centralized Risk and Compliance Platform Implementing a centralized risk and compliance platform can significantly enhance the efficiency of audit evidence collection across various standards. Such a platform serves as a unified repository for all audit documentation and evidence required.

Duo's Security Blog
MARCH 12, 2021
The Mobile Devices and Laptops & Desktops dashboards show which platforms, devices, and browsers connect to your Duo protected applications and services. Decentralization of device management and the rise of BYOD (Bring Your Own Device) can leave administrators wondering how users are accessing resources.

Google Security
DECEMBER 4, 2020
It is an excellent platform for building capable applications, and it powers thousands of services created and maintained by engineers at Google that are depended on by billions of users. We hope this new resource encourages further research into creative attacks and robust defenses for a major class of web security threats.

CyberSecurity Insiders
APRIL 16, 2023
This e-guide offers an in-depth understanding of the email security landscape, actionable guidance on implementing and maintaining robust email security solutions, and an overview of top email security vendors. Mimecast: Mimecast’s cloud-based email security platform offers comprehensive protection against phishing, spam, and malware.

Security Boulevard
FEBRUARY 20, 2022
Campaign overview. Hackers are targeting Teams platform for sharing malicious trojan files at scale to infect unwitting users. While this is probably not the first time that teams have been used for infecting users, this trend has been on the rise with increasing popularity of Teams.

Centraleyes
NOVEMBER 5, 2023
” HIPAA: An Overview HIPAA, short for the Health Insurance Portability and Accountability Act, is a pivotal U.S. HITRUST: An Overview On the contrary, HITRUST is an organization that introduced the HITRUST CSF (Common Security Framework) in 2009. and globally.

Cisco Security
JUNE 29, 2022
The purpose of this document is to provide the reader with a high-level overview of cloud delivery models, introduce the different deployment scenarios in which cloud services can be operated in, and highlight the risks to an organization when deploying and operating a cloud environment. AWS Cloud Security: Shared Responsibility Model.
CyberSecurity Insiders
DECEMBER 9, 2021
SOLUTION OVERVIEW. This easy-to-use platform helps IT teams quickly gauge and prioritize risks and liabilities to their organization. IT teams can quickly learn and operate the platform without needing to dedicate extra resources to managing a complex system. How is the solution unique or different from alternative approaches?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content