The Presenting Vendor Paradox
Daniel Miessler
JULY 21, 2021
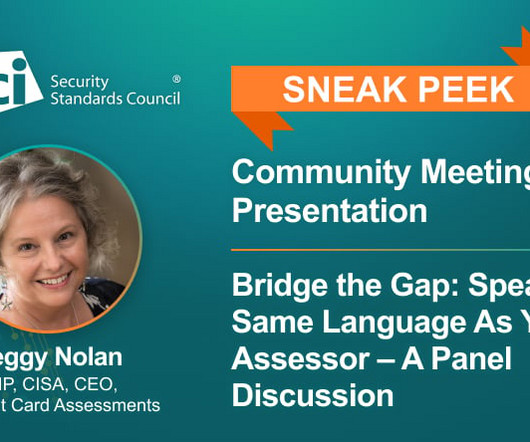
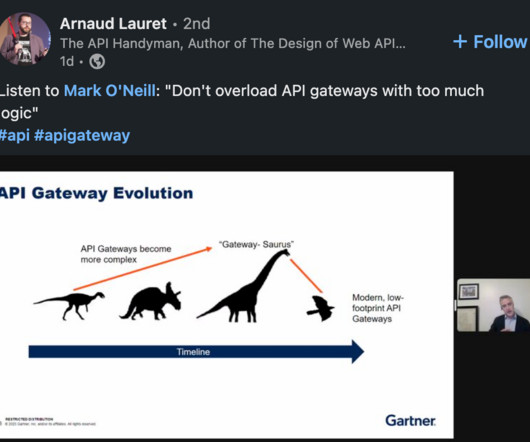
This presenter is just talking their own book! Many conference schedules, however, are full of talks from people who work at vendors. Conversely, people in the crowd at these conferences often have two complaints about the content. There isn’t enough good content, or. They sell service!





































Let's personalize your content