Ransomware gang targets Windows admins via PuTTy, WinSCP malvertising
Bleeping Computer
MAY 18, 2024
A ransomware operation targets Windows system administrators by taking out Google ads to promote fake download sites for Putty and WinSCP. [.]
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Bleeping Computer
MAY 18, 2024
A ransomware operation targets Windows system administrators by taking out Google ads to promote fake download sites for Putty and WinSCP. [.]
Security Affairs
OCTOBER 13, 2023
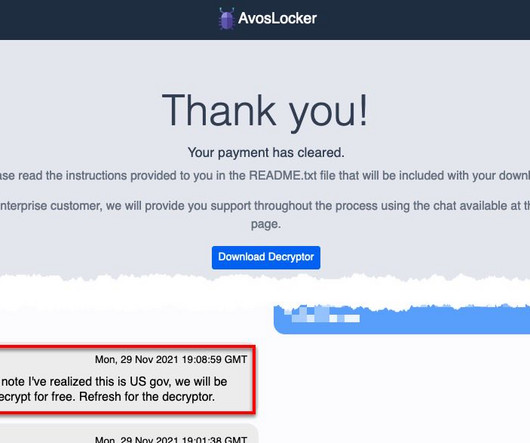
FBI and CISA published a joint Cybersecurity Advisory (CSA) to disseminate IOCs, TTPs, and detection methods associated with AvosLocker ransomware. The joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort aimed at sharing technical details associated with various ransomware operations.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
AUGUST 15, 2022
The top ransomware gangs have become so relentless that it’s not unusual for two or more of them to attack the same company within a few days – or even a few hours. Related: How ‘IABs’ foster ransomware. LockBit went in first and exfiltrated data and passwords, and then used PsExe to distribute their ransomware payload.

Bleeping Computer
MARCH 16, 2021
The Federal Bureau of Investigation (FBI) Cyber Division has warned system administrators and cybersecurity professionals of increased Pysa ransomware activity targeting educational institutions. [.].
Krebs on Security
JUNE 9, 2020
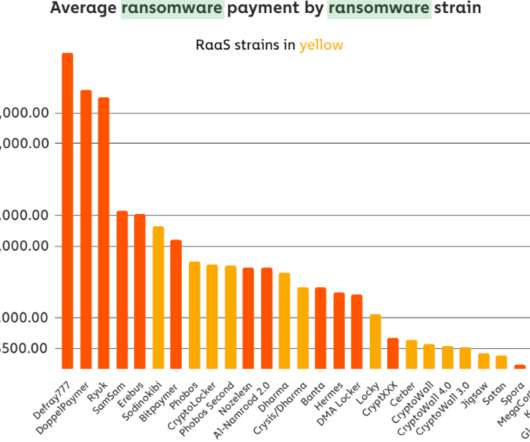
that their information technology systems had been infiltrated by hackers who specialize in deploying ransomware. Nevertheless, on Friday, June 5, the intruders sprang their attack, deploying ransomware and demanding nearly $300,000 worth of bitcoin. The average ransomware payment by ransomware strain.

Thales Cloud Protection & Licensing
MAY 17, 2023
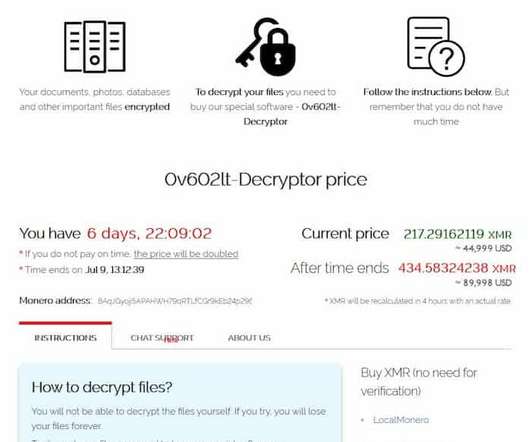
Ransomware – Stop’em Before They Wreak Havoc madhav Thu, 05/18/2023 - 06:03 Cybercriminals have been making a run on your data with ransomware attacks over the last decade in increasing frequency. What is Ransomware? Ransomware is a vicious type of malware that infects your laptop/desktop or server.
The Hacker News
FEBRUARY 11, 2023
Cybersecurity and Infrastructure Security Agency (CISA) released a decryptor for affected victims to recover from ESXiArgs ransomware attacks, the threat actors have bounced back with an updated version that encrypts more data.

CyberSecurity Insiders
DECEMBER 2, 2021
Proxy Shell vulnerabilities identified in Microsoft Exchange Servers are being exploited by hackers operating and distributing a new ransomware variant dubbed BlackByte. Microsoft has issued a fix to a similar vulnerability in May this year by patching flaws that were being used by those launching LockFile Ransomware onto compromised systems.

Security Boulevard
JULY 26, 2021
One of the latest examples in this trend is a ransomware attack on Kaseya’s Virtual System Administrator (VSA) solution for remote monitoring and management (RMM). The post What Security Lessons Can Come From the Kaseya Ransomware Attack? appeared first on Security Boulevard.

The Hacker News
JULY 11, 2021
Florida-based software vendor Kaseya on Sunday rolled out software updates to address critical security vulnerabilities in its Virtual System Administrator (VSA) software that was used as a jumping off point to target as many as 1,500 businesses across the globe as part of a widespread supply-chain ransomware attack.
Security Affairs
SEPTEMBER 23, 2023
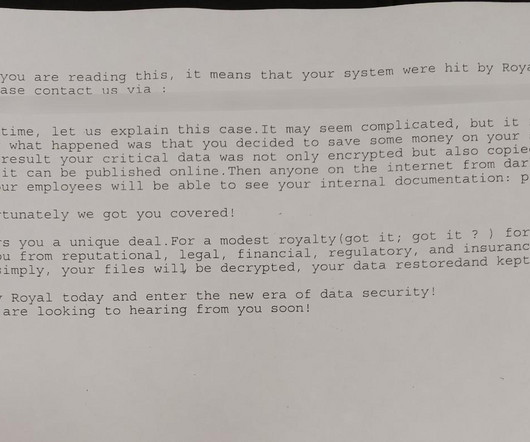
The City of Dallas revealed that the Royal ransomware gang that hit the city system in May used a stolen account. In May 2023, a ransomware attack hit the IT systems at the City of Dallas , Texas. To prevent the threat from spreading within the network, the City shut down the impacted IT systems.

Security Affairs
AUGUST 9, 2021
Taiwanese vendor Synology has warned customers that the StealthWorker botnet is targeting their NAS devices to deliver ransomware. Taiwan-based vendor Synology has warned customers that the StealthWorker botnet is conducting brute-force attacks in an attempt to implant ransomware. Follow me on Twitter: @securityaffairs and Facebook.
Security Boulevard
MARCH 12, 2021
Following exposure and publication of a major remote execution vulnerability like Exchange’s ProxyLogon (CVE-2021-26855), we expect other threat actors to join the race against system administrators trying to patch their systems. The post Exchange Week 2 – Ransomware Joins The Fray appeared first on Infocyte.

Krebs on Security
JULY 8, 2021
Last week cybercriminals deployed ransomware to 1,500 organizations that provide IT security and technical support to many other companies. The attackers exploited a vulnerability in software from Kaseya , a Miami-based company whose products help system administrators manage large networks remotely.
Security Affairs
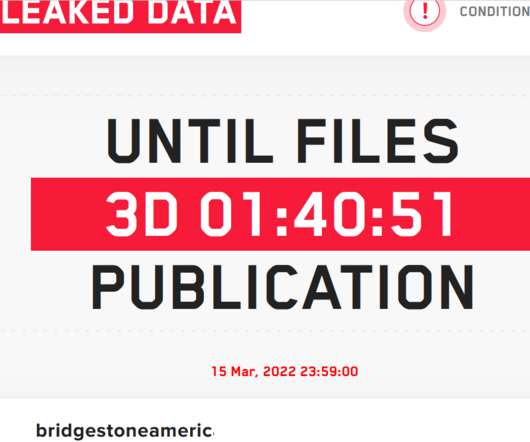
MARCH 13, 2022
LockBit ransomware gang claimed to have hacked Bridgestone Americas, one of the largest manufacturers of tires. LockBit ransomware gang claimed to have compromised the network of Bridgestone Americas, one of the largest manufacturers of tires, and stolen data from the company. Follow me on Twitter: @securityaffairs and Facebook.
eSecurity Planet
NOVEMBER 4, 2021
Ransomware groups seem to change form daily. In the latest news, the BlackMatter ransomware group announced it was shutting down – and just hours later came news that its victims were being transferred to the rival LockBit site. Also read: Best Ransomware Removal and Recovery Services. FIN7 Dupes Security Job Applicants.

eSecurity Planet
FEBRUARY 15, 2022
Ransomware attacks on critical infrastructure and a surge in exploited vulnerabilities are getting the attention of U.S. BlackByte Ransomware Attack Methods, IoCs. The FBI-Secret Service warning came just ahead of news that the NFL’s San Francisco 49ers had also been hit by BlackByte ransomware. The FBI and U.S.

Krebs on Security
SEPTEMBER 30, 2023
Earlier this week, KrebsOnSecurity revealed that the darknet website for the Snatch ransomware group was leaking data about its users and the crime gang’s internal operations. It continues: “Prior to deploying the ransomware, Snatch threat actors were observed spending up to three months on a victim’s system.

Malwarebytes
JULY 6, 2021
At 11:37 pm on the night of September 20, 2019, cybercriminals launched a ransomware attack against Northshore School District in Washington state. Early the next morning, Northshore systems administrator Ski Kacoroski arrived on scene. And importantly, in just four days, the school district needed—by law—to pay its reachers.
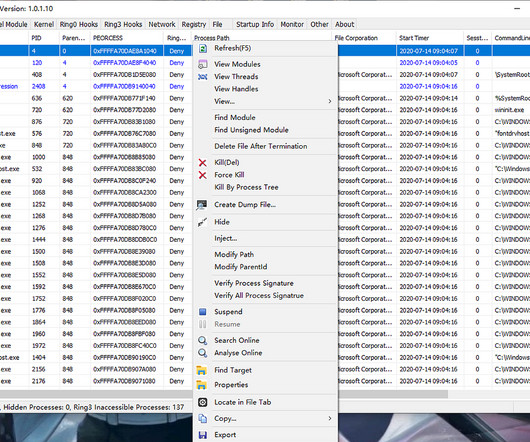
Security Affairs
MARCH 14, 2023
Cyber security researcher Luca Mella analyzed the Makop ransomware employed in a recent intrusion. Executive summary Insights from a recent intrusion authored by Makop ransomware operators show persistence capability through dedicated.NET tools. Everything is freeware software maintained by Voidtools.

Hot for Security
MAY 26, 2021
The Federal Bureau of Investigation has said in a flash announcement that the Conti ransomware group is responsible for at least 16 attacks targeting US healthcare and first responder networks within the last year. Once Conti actors deploy the ransomware, they may stay in the network and beacon out using Anchor DNS.”.

Krebs on Security
NOVEMBER 8, 2021
Department of Justice today announced the arrest of Ukrainian man accused of deploying ransomware on behalf of the REvil ransomware gang, a Russian-speaking cybercriminal collective that has extorted hundreds of millions from victim organizations. The DOJ also said it had seized $6.1 Vasinskyi was arrested Oct. victim organizations.

Security Affairs
FEBRUARY 2, 2021
Ransomware operators are exploiting two VMWare ESXi vulnerabilities, CVE-2019-5544 and CVE-2020-3992, to encrypt virtual hard disks. Security experts are warning of ransomware attacks exploiting two VMWare ESXi vulnerabilities, CVE-2019-5544 and CVE-2020-3992 , to encrypt virtual hard disks. Pierluigi Paganini.

Malwarebytes
OCTOBER 22, 2021
It’s widely known, and endlessly repeated, that the last, best line of defence against the potentially devastating effects of a ransomware attack is your backups. Ski Kacoroski, System administrator, Northshore School District. Ski Kacoroski, System administrator, Northshore School District.
Security Affairs
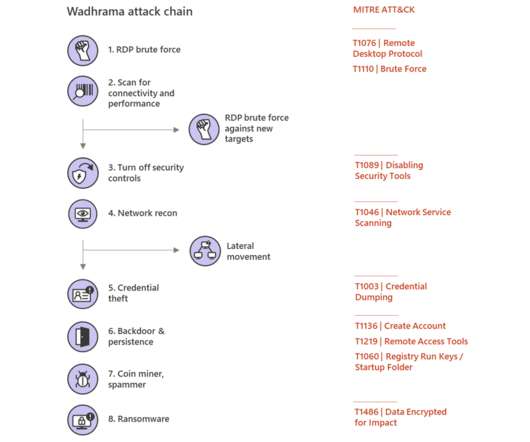
MARCH 10, 2020
Microsoft is warning of human-operated ransomware, this kind of attack against businesses is becoming popular in the cybercrime ecosystem. Human-operated ransomware is a technique usually employed in nation-state attacks that is becoming very popular in the cybercrime ecosystem. ” reads the post published by Microsoft.

Malwarebytes
APRIL 9, 2024
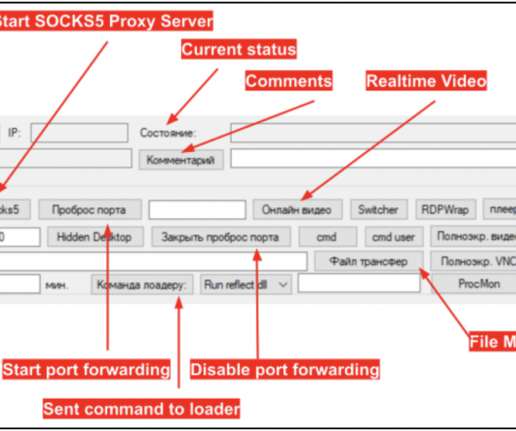
In the past couple of weeks, we have observed an ongoing campaign targeting system administrators with fraudulent ads for popular system utilities. Nitrogen is used by threat actors to gain initial access to private networks, followed by data theft and the deployment of ransomware such as BlackCat/ALPHV. dll (Nitrogen).

Malwarebytes
JULY 7, 2021
Only rarely do companies allow us a look inside their organization while they are recovering from a ransomware attack. The attack used a zero-day vulnerability to create a malicious Kasaya VSA update, which spread REvil ransomware to some of the MSPs that use it, and then on to the customers of those MSPs. Know when to communicate.
Malwarebytes
MARCH 31, 2023
Backups are an organization's last line of defense against ransomware, because comprehensive, offline, offsite backups give you a chance to restore or rebuild your computers without paying a criminal for a decryption key. That's exactly what happened when a ransomware gang attacked the Northshore School District in Washington state.

Malwarebytes
AUGUST 27, 2021
Ransomware gangs have nurtured a nasty habit of starting their attacks at the least convenient times: When computers are idle, when employees who might notice a problem are out of the office, and when the IT or security staff who might deal with it shorthanded. Why out-of-office attacks work.
Security Affairs
OCTOBER 22, 2021
FIN7 hacking group created fake cybersecurity companies to hire experts and involve them in ransomware attacks tricking them of conducting a pentest. The FIN7 hacking group is attempting to enter in the ransomware business and is doing it with an interesting technique. ” concludes the report. Pierluigi Paganini.
Digital Shadows
JULY 5, 2021
On 02 July 2021, details started to emerge of a sophisticated supply-chain attack targeting Kaseya VSA, virtual system administrator software.

Spinone
FEBRUARY 5, 2020
When someone asks you about the best ransomware protection , the first thing you’ll probably come up with is a backup. Antivirus software and firewalls are just the first line of defense, which is far from being 100% effective against ransomware. Ransomware can infect backups. Can Ransomware Encrypt Backups?

Malwarebytes
JULY 23, 2021
Two months after fully restoring its systems, CNA Financial, the leading US insurance company that was attacked by a group using Phoenix CryptoLocker ransomware, issued a legal notice of an information security incident to the Consumer Protection Bureau in New Hampshire. Recovering from ransomware. Data stolen but untouched.

SecureWorld News
JANUARY 13, 2021
Intel recently announced it is adding hardware-based ransomware detection and remediation to its new 11th gen Core vPro processors. Intel claims that “hardened PCs enable best practices for ransomware defense,” and that this security improvement will be a game changer in defending against ransomware.

Quick Heal Antivirus
JULY 29, 2022
PowerShell was originally intended as a task automation and configuration management program for system administrators. However, it. The post PowerShell: An Attacker’s Paradise appeared first on Quick Heal Blog | Latest computer security news, tips, and advice.

CSO Magazine
NOVEMBER 28, 2022
Cobalt Strike is a commercial attack framework designed for red teams that has also been adopted by many threat actors, from APT groups to ransomware gangs and other cybercriminals. Living off the land is a common tactic.

Thales Cloud Protection & Licensing
NOVEMBER 24, 2020
Mitigating Ransomware Attacks – Decoupling Encryption Keys From Encrypted Data. While ransomware attacks have been around for decades, their frequency has exponentially increased in the last few years, let alone the past several months during the pandemic. The potency of a ransomware attack lies in its diabolical ingenuity.

Malwarebytes
APRIL 17, 2023
Regular readers of our monthly ransomware review ( read our April edition here ) know that Ransomware-as-a-Service (RaaS) gangs have been making headlines globally with their disruptive attacks on organizations. Sometimes, though, it’s not enough to merely know about of the problem.
Krebs on Security
JUNE 13, 2023
today released software updates to fix dozens of security vulnerabilities in its Windows operating systems and other software. Microsoft Corp. “An attacker able to gain admin access to an internal SharePoint server could do a lot of harm to an organization,” said Kevin Breen , director of cyber threat research at Immersive Labs.

eSecurity Planet
FEBRUARY 26, 2024
The fix: System administrators are encouraged to install the Exchange Server 2019 Cumulative Update 14 (CU14), which was issued in February 2024 and enabled NTLM credentials Relay Protection. Despite VMware’s three-year-old deprecation statement, unprotected systems remain at risk.

Security Boulevard
JULY 6, 2021
Kaseya is now reporting the software-as-a-service (SaaS) instance of its Virtual System Administrator (VSA) platform will be back online sometime between 4:00 p.m. and 7:00 p.m. It expects the on-premises editions of VSA to be patched within 24 hours after that.

Digital Shadows
JULY 5, 2021
On 02 July 2021, details started to emerge of a sophisticated supply-chain attack targeting Kaseya VSA, virtual system administrator software used to manage and monitor customers’ infrastructure. Kaseya VSA is commonly used by managed service providers (MSPs) in the US and UK to help them manage their clients’ systems.
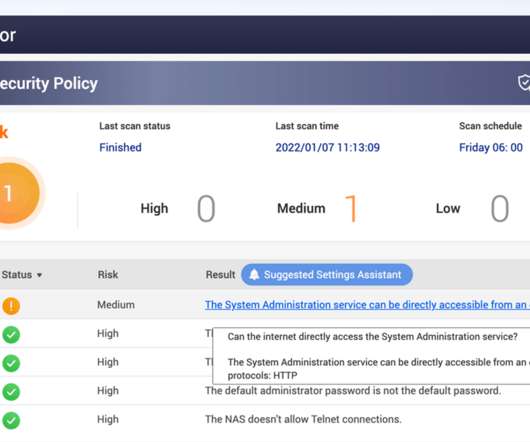
Security Affairs
JANUARY 7, 2022
QNAP is warning customers of ransomware attacks targeting network-attached storage (NAS) devices exposed online. Taiwanese vendor QNAP has warned customers to secure network-attached storage (NAS) exposed online from ransomware and brute-force attacks. In December a new wave of ech0raix ransomware attacks targeted QNAP NAS devices.

Webroot
APRIL 2, 2024
While RDP is a powerful tool for remote administration and support, it has also become a favored vector for brute force attacks for several reasons: Widespread use: RDP is commonly used in businesses to enable remote work and system administration.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content