Secure Business-Critical Resources with a Web Application Firewall
Tech Republic Security
JULY 18, 2023
Request a demo of an Array web application firewall to learn how you can protect your business from DDoS & zero-day attacks.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 request-demo
request-demo 
Tech Republic Security
JULY 18, 2023
Request a demo of an Array web application firewall to learn how you can protect your business from DDoS & zero-day attacks.

Troy Hunt
APRIL 1, 2023
Pwned Passwords has now surpassed 4 billion monthly requests! (I'm Book a demo today. 🤷♂️) The tweet that went nuts (can we all just agree that Twitter - and Elon - are polarising, but both are still here, still working and probably not going anywhere soon?) It's Zero Trust tailor-made for Okta.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
JULY 18, 2023
Request a demo now. Array Networks offers SSL VPN gateways to meet a variety of needs for small and medium enterprises.

Tech Republic Security
JULY 18, 2023
Request a demo of load balancing from Array Networks, purpose-built for the requirements of small and medium enterprises.

Troy Hunt
JUNE 8, 2023
I spent most of this week's update on the tweaking I went through with Azure's API Management service and then using Cloudflare to stop a whole bunch of requests that really didn't need to go all the way to the origin (or at least all the way to the API gateway sitting in front of the origin Azure Function instance).
Troy Hunt
MARCH 10, 2023
Book a demo today. Sponsored by: Kolide ensures only secure devices can access your cloud apps. It's Device Trust tailor-made for Okta.

NetSpi Technical
SEPTEMBER 22, 2023
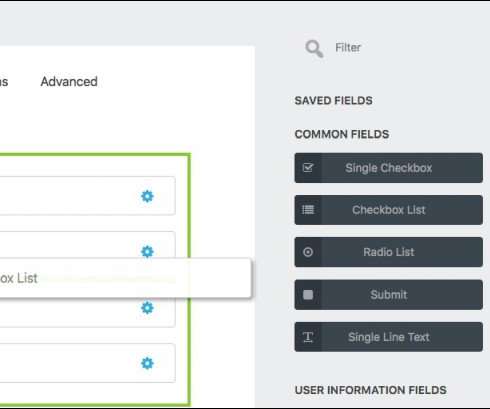
Basics of Macros Gathering Dynamic Values Macros for Complex Situations Basics of Macros In this first video, I cover a couple of basics of Macros: what they are, why we might use them, and 2 demos of basic usage. Note that the tricky thing with that is the login request doesn’t contain a “Set-Cookie” header in the response.
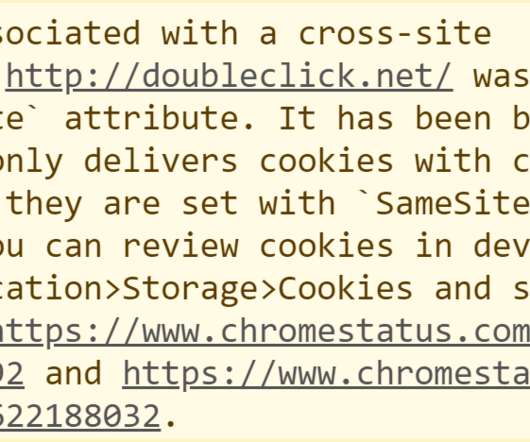
Troy Hunt
JANUARY 3, 2020
I mean have a think about it: If a website sets a cookie then you click a link to another page on that same site, will the cookie be automatically sent with the request? Cookies just don't care about how the request was initiated nor from which origin, all they care about is that they're valid for the requested resource.
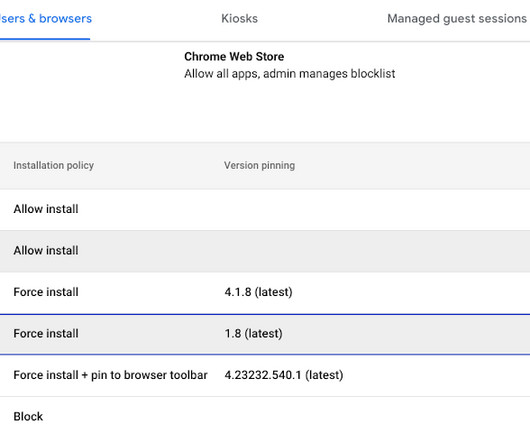
Google Security
JUNE 20, 2023
Extension workflow Extension workflow allows end users to request extensions for review. We recently added a prompt for business justification for documenting why users are requesting the extension. From there, IT can either approve or deny them.
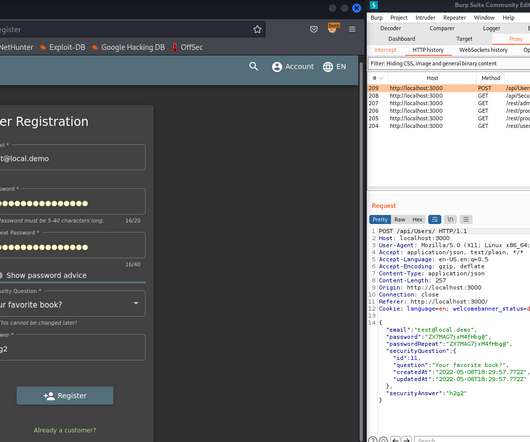
eSecurity Planet
MAY 9, 2022
HTTP requests). The Burp suite has many advanced features but the most popular is probably the Burp proxy that can intercept requests. Setting Up a Demo. Burp Suite Demo: Intercepting Requests. The Burp suite is widely used by security professionals to perform advanced scans and various traffic interceptions (e.g.,

Troy Hunt
JULY 12, 2018
So that's precisely what I've done - intercepted my own traffic passed over an insecure connection and put together a string of demos in a 24-minute video explaining why HTTPS is necessary on a static website. Here's the video and there's references and code samples for all the demos used immediately after that: HTTPS Is Easy.
Security Affairs
FEBRUARY 17, 2020
A serious flaw in the ThemeGrill Demo Importer WordPress theme plugin with over 200,000 active installs can be exploited to wipe sites and gain admin access to the site. Experts from the security firm WebARX have discovered a serious flaw in the WordPress theme plugin ThemeGrill Demo Importer with over 200,000 active installs.

Security Boulevard
MAY 17, 2024
The alarm bells would have been going off as soon as the first 5k request was received. If you would like to learn more about Salt and how we could provide you with API discovery, governance, and protection, please contact us , schedule a demo , or check out our website.

Security Boulevard
FEBRUARY 14, 2024
How is FireMon Better Book a Demo Healthcare companies have a responsibility to protect sensitive patient data and ensure compliance with regulations like HIPAA. To learn more about how FireMon can help your healthcare organization, request a demo today. Why Act Now? Why Choose FireMon?
Security Boulevard
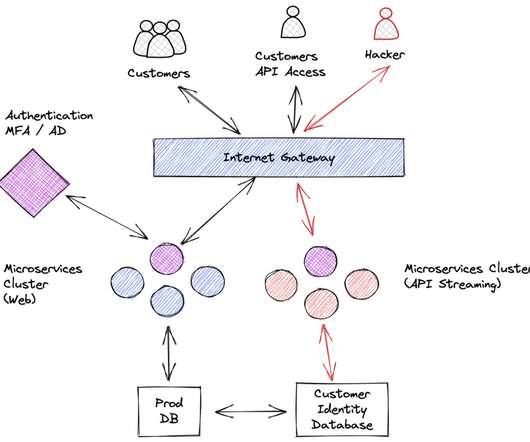
SEPTEMBER 26, 2022
Essentially anyone in public domain is allowed to send a request asking the server “fetch contact details for Optus customer with contactid=XXXXXXXXX”. Lack of authorization checks for every user request. Sending sensitive information in the URL of a request: When in doubt, send parameters within the body of a POST request.

CyberSecurity Insiders
SEPTEMBER 23, 2021
In this demo, let's try capturing and analyzing ARP traffic. Find existing ARP cache -> Delete the existing one to understand the demo -> Check ARP cache for verification. Analyze an ARP Request. Click the ICMP echo-request packet from the Wireshark capture window and start observing the information.

Duo's Security Blog
FEBRUARY 19, 2024
Think of it like having a dedicated advocate behind the curtain who is highlighting the ideas that you’ve submitted as feature requests and proactively looking out for new functionalities that might be of interest to you or that might help you better achieve your security goals. It could be a combination of conversations and demos.
ForAllSecure
OCTOBER 25, 2022
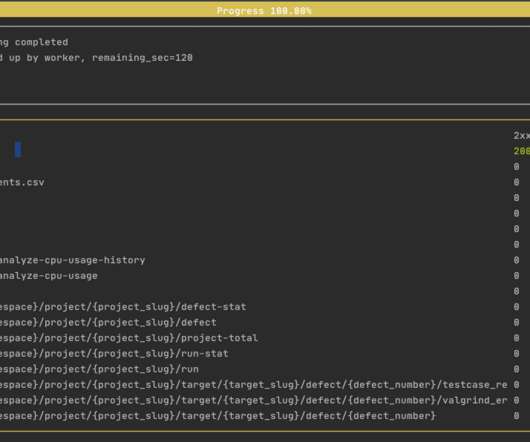
Tells the fuzzer to base its testing on the OpenAPI 3 specification of the petstore demo API, which is hosted on our site for demo purposes. --url Tells the fuzzer, which is running locally on your computer, to address its tests to the petstore demo API on our network. Get Free Request A Demo. url "[link].
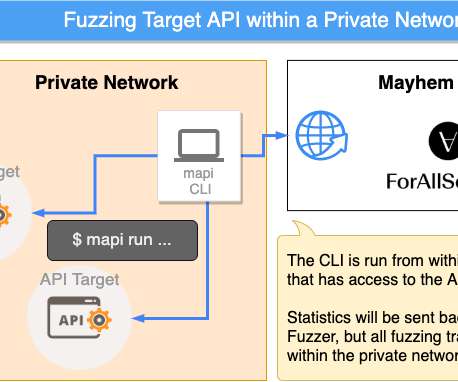
ForAllSecure
SEPTEMBER 30, 2022
You've seen what Mayhem for API can do in a demo. Because the requests come directly from the mapi CLI tool running locally on your computer, this will work for APIs that are: Behind a corporate firewall. Get Free Request A Demo. Now it's time to fuzz your own! Mayhem for API needs to know the URL of your API server.

CyberSecurity Insiders
MAY 12, 2023
Learn more about the benefits of compliance automation and then schedule a demo to see how you can streamline your audit processes. Streamlined Audits Companies that monitor compliance manually dread requests for audits. Schedule a demo to see how Drata can transform your audit experience. What is Compliance Automation?
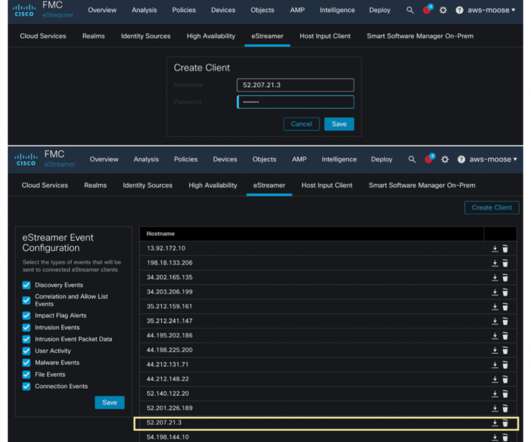
Cisco Security
NOVEMBER 29, 2022
The eNcore client can request event and host profile data from a Management Center, and intrusion event data only from a managed device. The eNcore client provides a way to tap into message-oriented protocol to stream events and host profile information from the Cisco Secure Firewall Management Center. re:Invent .
Security Boulevard
DECEMBER 1, 2022
I was deeply involved in the request for information (RFI) with Forrester for the 2022 report, and I believe I can shed some light on the evaluation process. Vendors had to document and demonstrate their effectiveness in all of them, for a total of 50 use case demos.

ForAllSecure
OCTOBER 12, 2022
Ultimately, if your Postman request works, we want Mayhem to just work. Try running the demo yourself against the Pet Store API: mapi run. Try running the demo yourself against the Pet Store API: mapi run. --url postman-integration-demo 30. Getting Started. You will need to create an API key in postman. url [link].
Security Affairs
MARCH 14, 2021
Below the description of the demo published on a site set up by Google to host the PoC code. “This demo is split into three parts: Calibrating the timer to observe side effects of the CPU’s speculative execution. A demonstration that infers the memory layout of a JavaScript array.
Malwarebytes
JANUARY 19, 2022
It also houses a database of consent history for app requests. Here’s a link to the demo video of how it now works in Monterey. The TCC is essentially the technology that keeps user data within a device private, so apps without full disk access rights cannot just access data without the user’s consent.

Spinone
JUNE 2, 2020
Request a demo and get them answered! Request a Demo The post SpinOne Application Auditing Capabilities first appeared on SpinOne. If one of G Suite users tries to give the blacklisted application access to corporate data, SpinOne will notify the administrator about it to prevent the possible data breach.

Security Boulevard
MARCH 19, 2021
For more information on tools to secure the remote workforce, speak to one of our cybersecurity experts or request a demo. . Request a Demo. Doing this ensures that when people work from home, they don’t cut corners and are as switched on and aware of potential threats as they would be in the office. Additional Resources.

Security Boulevard
MARCH 17, 2021
To see how Clearswift security products can be used alongside Office 365, you can request a full demo from the team. Request a Demo. Deploying Clearswift DLP in conjunction with Office 365 provides the best of both worlds – complete data protection without compromising on internal or external collaboration.

Krebs on Security
JUNE 19, 2018
At issue are companies known in the wireless industry as “location aggregators,” entities that manage requests for real-time customer location data for a variety of purposes, such as roadside assistance and emergency response. LocationSmart disabled its demo page shortly after that story. By that time, Sen. ” Sen.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . Kasada uses a unique mitigative method that scales the difficulty of accessing web applications based on a growing number of requests. You can request a demo or contact the company for a quote. Kasada plans.

eSecurity Planet
MARCH 29, 2021
Request a Kaspersky product demo. You can request a free demo of Symantec solutions from their website. . In order to figure out which of the two solutions is a better fit for your organization, request a free demo at your convenience. . Kaspersky Endpoint Security Cloud Plus – $513.70 for 10 endpoints.

eSecurity Planet
FEBRUARY 26, 2021
This information is then analyzed to determine if the client request is from a human user or a bot. . Kasada uses a unique mitigative method that scales the difficulty of accessing web applications based on a growing number of requests. You can request a demo or contact the company for a quote. Kasada plans.

Security Affairs
MAY 27, 2021
A demo app to access this register is available here.” one side writes 1x to send data, the other side writes 00 to request the next bit). This makes it a two-bit covert channel that any arbitrary process can use to exchange data with another cooperating process. ” said Hector Martin.

Pentester Academy
APRIL 20, 2023
This can be confirmed by sending a curl request to the available candidate ports. Step 3: Send a request to the Java application on port 8080. Request contents for that link: Command: curl [link] The response says forbidden. Command: curl [link] Notice one link in the response: /admin/index.
ForAllSecure
SEPTEMBER 8, 2022
Security - With a growing list of Security Checkers , Mayhem for API can discover issues such as Server Side Request Forgery (SSRF) and SQL Injection. Get Free Request A Demo. With the help of fuzzing, Mayhem for API identifies blind spots in your existing testing, without the bias or the tedium of manually written tests.
Security Affairs
FEBRUARY 19, 2020
When doing so, it does not verify that a request is coming from an administrative user. 2020 – Over 200K WordPress sites are exposed to attacks due to a high severity cross-site request forgery (CSRF) bug in Code Snippets plugin. “One of the plugin’s functions registers a WordPress REST-API endpoint.

Pentester Academy
MARCH 10, 2023
To learn more about how INE Business Solutions can solve your business’s IT training challenges, request a free demo of our platform. Sources cited: [link] [link] [link] Originally published at [link].

Security Boulevard
FEBRUARY 7, 2022
Request a personalized demo. These two most recent awards join the long list of accolades we’ve earned – we’d love to show you how our award-winning API security platform can protect your most vital data and services. undefined.

The Last Watchdog
AUGUST 31, 2023
A demo is available upon request. The platform keeps workers safe, while helping companies significantly reduce overhead costs from general liability, worker’s compensation, and property claims. ??Voxel For more information, visit [link] or follow via LinkedIn and X.

Security Affairs
MARCH 9, 2019
The researchers discovered that the APIs for both applications failed to authenticate requests allowing attackers to take over customers’ accounts due to insecure direct object references (IDORs) issues. Both products allow anyone to create a test/demo account. the attacker’s) and take over the account,” continues the experts.
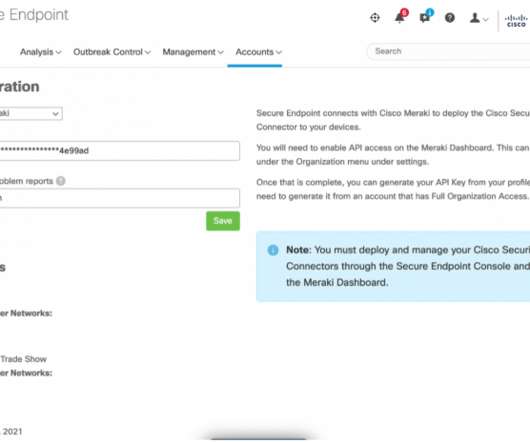
Cisco Security
NOVEMBER 29, 2021
This offers application auditing and correlation, logging of encrypted URL requests without SSL decryption, and full visibility of network traffic from the device, by taking advantage of the supervised mode iOS API’s. The conference Umbrella org does not block any requests since we do not want to interrupt demos or any network activity.
Security Boulevard
DECEMBER 9, 2021
If you want to follow along with the demo, the vulnerable project Tarpit Java is here. You’ll see that this gives us a list of identifiers that contain input from HTTP requests. For this demo, let’s focus on calls to “exec”, which often indicates system command execution. I typically run cpg.method.name.l for this purpose.
Security Affairs
MAY 1, 2020
The developers behind the Ninja Forms WordPress plugin have addressed a Cross-Site Request Forgery (CSRF) vulnerability that could lead to Stored Cross-Site Scripting (Stored XSS) attacks. Experts noticed that two of these functions failed to check nonces, this means that they don’t verify the identity of the user that sent a request.

Duo's Security Blog
NOVEMBER 3, 2023
If an unauthenticated user attempts to gain access to an application, their request is redirected to Duo. The diagram below illustrates the integration’s architecture: Datawiza Access Proxy functions as a reverse proxy that resides ahead of the applications. It communicates with Duo through OIDC or SAML protocols.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content