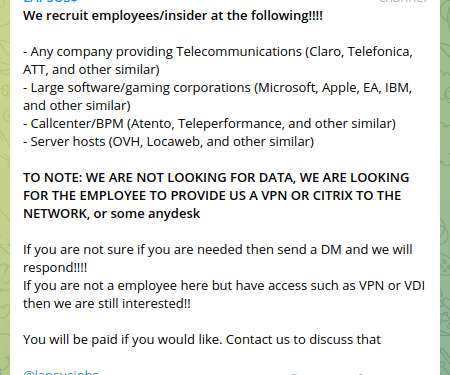
Lapsus$ Ransomware Group is hiring, it announced recruitment of insiders
Security Affairs
MARCH 11, 2022
Their scope of interests include – major telecommunications companies such as Claro, Telefonica and AT&T. Cybersecurity experts agree such activity creates a major insider threat risk and likely will be leveraged more actively by various threat actors on Dark Web. .





















Let's personalize your content