Chinese Antivirus Firm Was Part of APT41 ‘Supply Chain’ Attack
Krebs on Security
SEPTEMBER 17, 2020
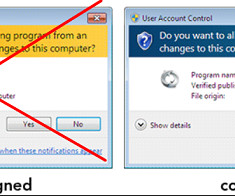
While the various charging documents released in this case do not mention it per se, it is clear that members of this group also favored another form of supply chain attacks — hiding their malware inside commercial tools they created and advertised as legitimate security software and PC utilities.




















Let's personalize your content