Homomorphic Encryption Makes Real-World Gains, Pushed by Google, IBM, Microsoft
eSecurity Planet
JUNE 24, 2021
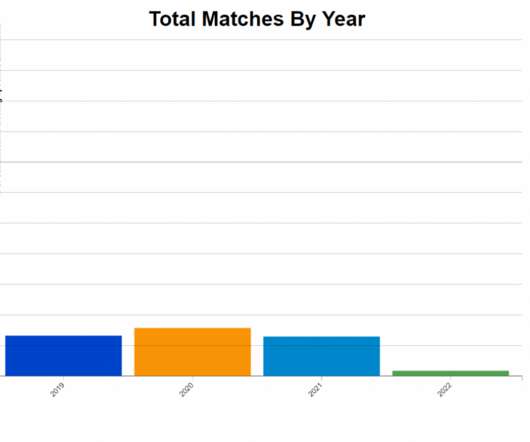
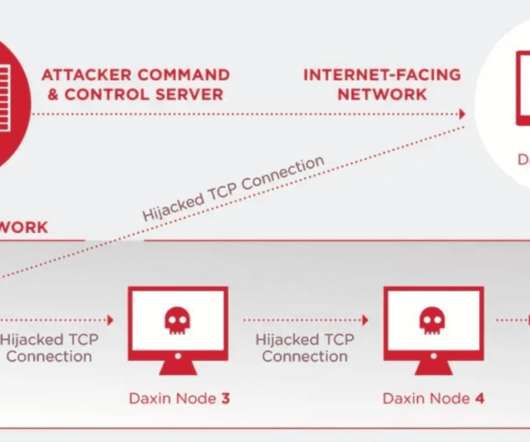
The increasing mobility of data, as it ping-pongs between clouds, data centers and the edge, has made it an easier target of cybercrime groups, which has put a premium on the encryption of that data in recent years. Since then, interest in fully homomorphic encryption (FHE) has increased, largely paralleling the rise of cloud computing.




































Let's personalize your content