Vodafone discovered backdoors in Huawei equipment. But it was 2011.
Security Affairs
APRIL 30, 2019
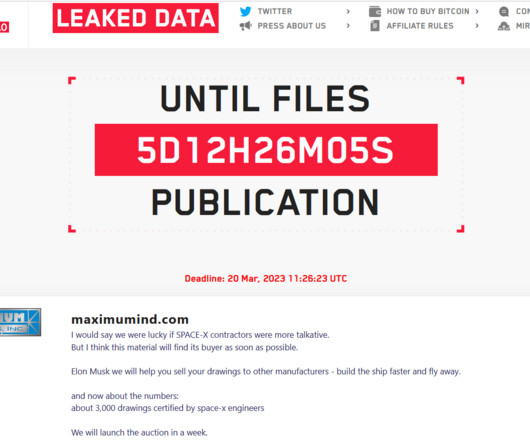
According to Bloomberg, Vodafone identified hidden backdoors in software that could have handed Huawei unauthorized access to the carrier’s fixed-line network in Italy used to connect to the internet. Bloomberg obtained Vodafone’s security briefing documents from 2009 and 2011 and spoke with people involved in the situation.




































Let's personalize your content