The ticking time bomb of Microsoft Exchange Server 2013
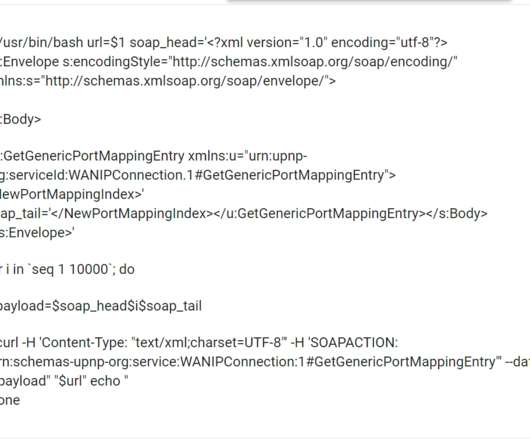
DoublePulsar
DECEMBER 22, 2023
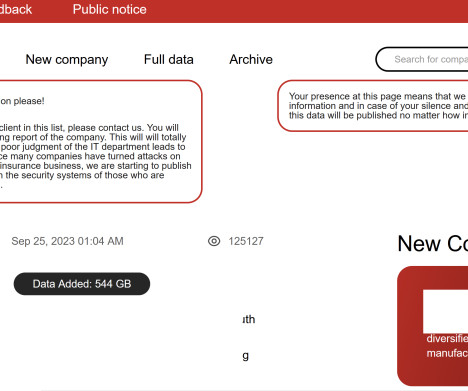
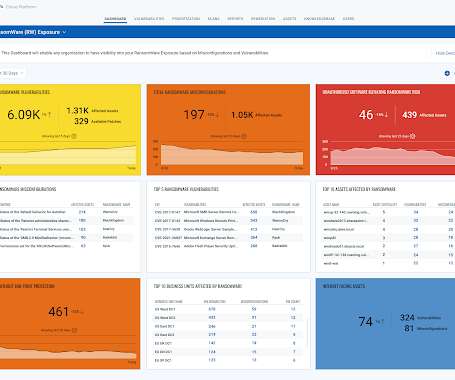
I monitor (in an amateur, clueless way) ransomware groups in my spare time, to see what intelligence can be gained from looking at victim orgs and what went wrong. toasty Something curious has been happened over the last few months — more and more ransomware group victims have Outlook Web App facing the internet.











































Let's personalize your content