New Reductor Nation-State Malware Compromises TLS
Schneier on Security
OCTOBER 10, 2019
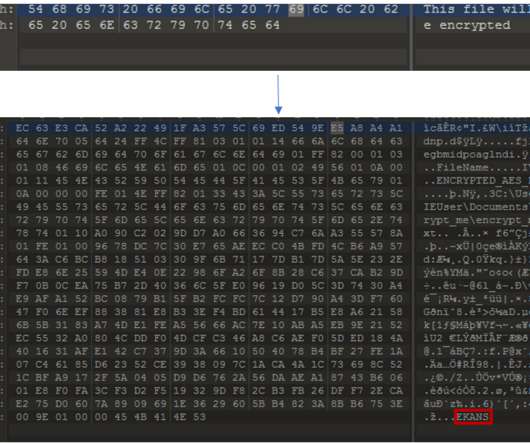
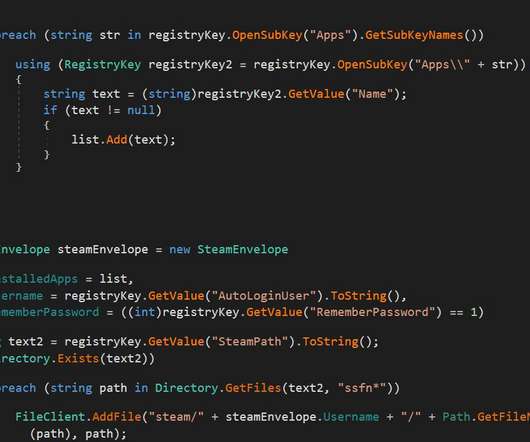
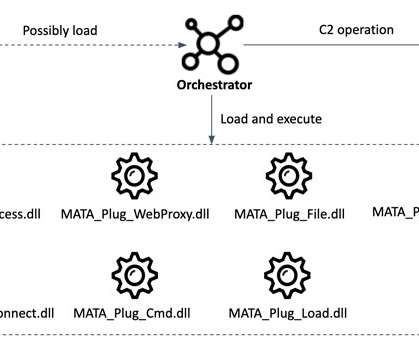
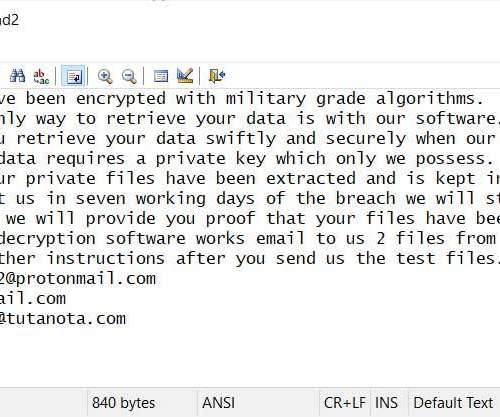
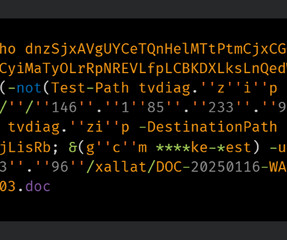
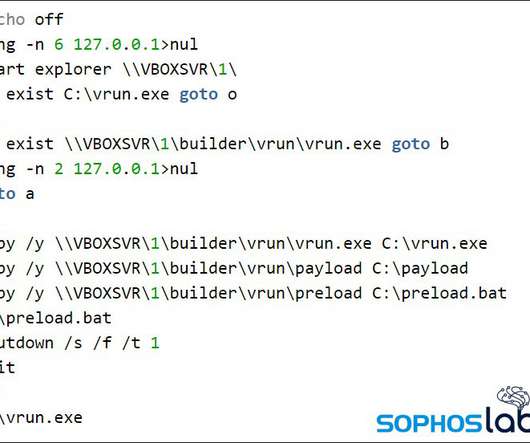
Kaspersky has a detailed blog post about a new piece of sophisticated malware that it's calling Reductor. Based on these similarities, we're quite sure the new malware was developed by the COMPfun authors. The COMpfun malware was initially documented by G-DATA in 2014.


























Let's personalize your content