Profiling Russia’s U.S Election Interference 2016 – An OSINT Analysis
Security Boulevard
JANUARY 26, 2022
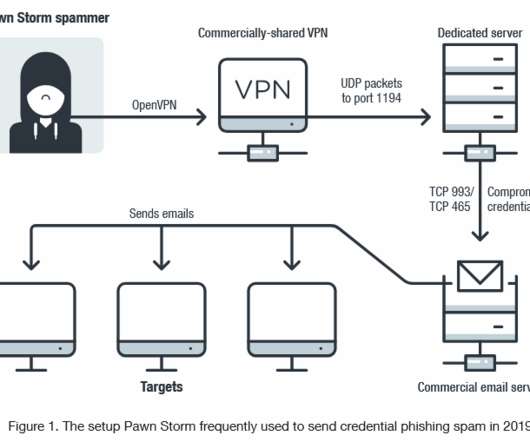
Note: This OSINT analysis has been originally published at my current employer's Web site - [link] where I'm currently acting as a DNS Threat Researcher since January, 2021. . In this analysis we’ll take a closer look at the Internet connected infrastructure behind the U.S Elections 2016 campaign: linuxkrnl[.]net. akamainet[.]net.



























Let's personalize your content