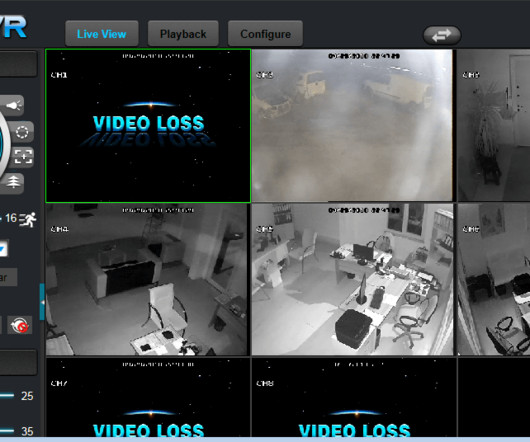
Here’s how anyone with $20 can hire an IoT botnet to blast out a week-long DDoS attack
The Last Watchdog
AUGUST 27, 2018
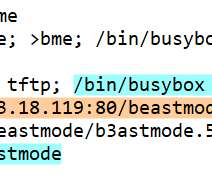
This is borne out by Akamai Technologies’ Summer 2018 Internet Security/Web Attack Report. A nascent cottage industry is starting to gel around DDoS botnets-for-hire , comprised of millions of compromised IoT devices. I had the chance to visit with Don Shin, A10 Networks’ Senior Product Marketing Manager, at Black Hat USA 2018.




























Let's personalize your content