MY TAKE: ‘Perimeter-less’ computing requires cyber defenses to extend deeper, further forward
The Last Watchdog
SEPTEMBER 27, 2019
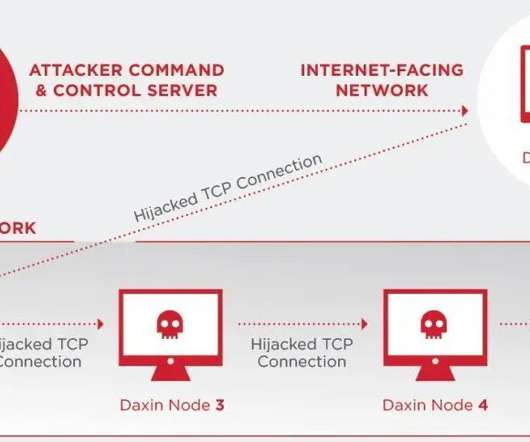
We met at Black Hat 2019 and Schuermann walked me through how Juniper’s security play pivots off the evolving infrastructure of a typical corporate network. Juniper gathers threat feeds via a security framework, called SecIntl , that runs off servers tied together by Juniper equipment deployed globally in corporate networks.























Let's personalize your content