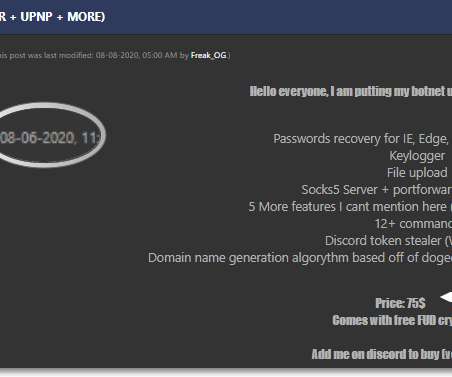
The source code of the 2020 variant of HelloKitty ransomware was leaked on a cybercrime forum
Security Affairs
OCTOBER 9, 2023
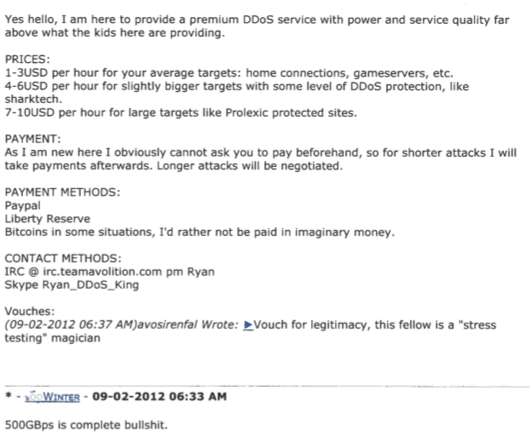
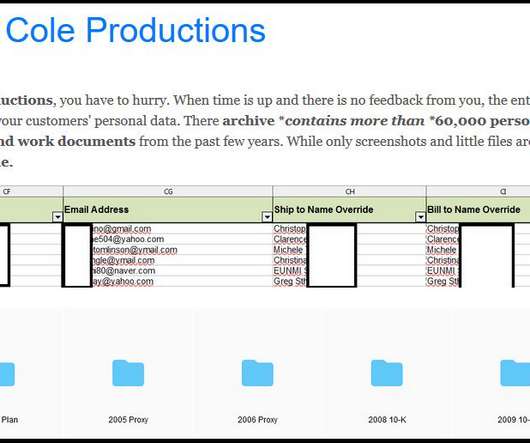
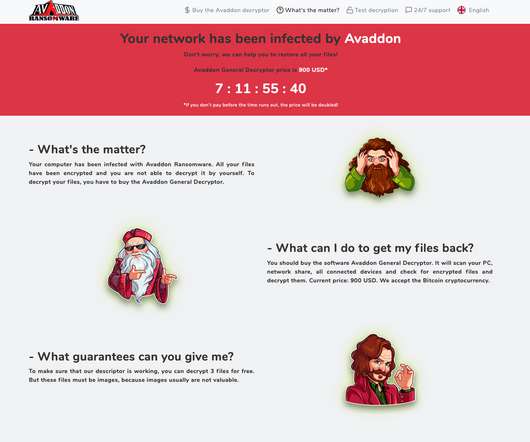
A threat actor has leaked the source code for the first version of the HelloKitty ransomware on a Russian-speaking cybercrime forum. The availability of the source in the cybercrime ecosystem can allow threat actors to develop their own version of the Hello Kitty ransomware. The HelloKitty gang has been active since January 2021.
































Let's personalize your content