Sharp Stealer: New Malware Targets Gamers’ Accounts and Online Identities
Penetration Testing
APRIL 22, 2024
A new threat has emerged in the cybercrime world, specifically designed to prey on the lucrative gaming community.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Penetration Testing
APRIL 22, 2024
A new threat has emerged in the cybercrime world, specifically designed to prey on the lucrative gaming community.

Cytelligence
DECEMBER 11, 2023
In recent developments that have sent shockwaves through the cybersecurity community, it has come to light that over 100,000 user account credentials of ChatGPT, a popular language model developed by OpenAI, have been stolen and sold on various dark web marketplaces. The consequences of this breach are far-reaching.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
MARCH 13, 2019
[ NASDAQ: SZMK ] says it is investigating a security incident in which a hacker was reselling access to a user account with the ability to modify ads and analytics for a number of big-name advertisers. He acknowledged that the purloined account had the ability to add or modify the advertising creatives that get run on customer ad campaigns.

SecureList
OCTOBER 20, 2021
Having been in the field for so long, we have witnessed some major changes in the cybercrime world’s modus operandi. This report shares our insights into the Russian-speaking cybercrime world and the changes in how it operates that have happened in the past five years. These services, too, have been outsourced.
Security Affairs
JANUARY 1, 2024
The MultiLogin endpoint endpoint is an internal mechanism that allows the synchronization of Google accounts across services. This endpoint receives a vector containing account IDs and auth-login tokens for efficiently handling concurrent sessions or seamlessly transitioning between user profiles. ” continues the report.

Security Boulevard
DECEMBER 19, 2022
biased exclusivity and double layer monetization combination where the attacker might only sell the database to its actual owner and actually get rid of it once they receive the payment.

SecureWorld News
FEBRUARY 27, 2021
One of the major issues surrounds keeping remote workers protected against cybercrime. Putting strong systems, processes, and cybersecurity products in place is a good start, but the next step is testing your system for any underlying weaknesses and vulnerabilities. Without these protections, remote staff can potentially be vulnerable.
Krebs on Security
JULY 23, 2020
As first reported here last year , First American’s website exposed 16 years worth of digitized mortgage title insurance records — including bank account numbers and statements, mortgage and tax records, Social Security numbers, wire transaction receipts, and drivers license images. It employs some 18,000 people and brought in $6.2
Krebs on Security
FEBRUARY 16, 2022
The same day the ICRC went public with its breach, someone using the nickname “ Sheriff ” on the English-language cybercrime forum RaidForums advertised the sale of data from the Red Cross and Red Crescent Movement. Sheriff says they will only accept offers that are guaranteed through the forum’s escrow account.

CyberSecurity Insiders
JANUARY 28, 2022
Some advanced network monitoring tools can automate this process, restricting accounts when they behave irregularly. Penetration Test Regularly. In light of these ongoing challenges, you should penetration test regularly to find any vulnerabilities that need fixing.
Security Affairs
APRIL 7, 2023
Cobalt Strike is a paid penetration testing product that allows an attacker to deploy an agent named ‘Beacon’ on the victim machine. Microsoft announced it has taken legal action to disrupt the illegal use of copies of the post-exploitation tool Cobalt Strike by cybercriminals. Our action is therefore not one and done.”

Security Affairs
MARCH 19, 2020
According to the report issued by the CERT-FR, operators behind the Pysa ransomware launched brute-force attacks against management consoles and Active Directory accounts. “Brute force connection attempts on a supervisory console have been observed, as well as on several ACTIVE DIRECTORY accounts. ” continues the alert.

SecureWorld News
OCTOBER 22, 2023
If you are already familiar with the evolving cyber threat landscape in your home country, you’ll know that humans are often the most exploited attack vector for cybercrime, and how frequently small businesses are breached. So, how exactly are these challenges exacerbated when moving your operations beyond borders?

Security Affairs
MARCH 18, 2023
ransomware include remote desktop protocol (RDP) exploitation, drive-by compromise, phishing campaigns, abuse of valid accounts, and exploitation of public-facing applications. Artifacts of professional penetration-testing tools such as Metasploit and Cobalt Strike have also been observed.” ” continues the report.

Security Affairs
DECEMBER 21, 2021
According to the unsealed indictment, Klyushin, Ermakov and Rumiantcev worked at M-13, a Russian cybersecurity firm offering penetration testing services and investment management services. For the latter service, the men were keeping for them up to 60% of the profit. ” reads the press release published by DoJ.

The Last Watchdog
MAY 2, 2019
While the internet and social media have been very positive for businesses, there remains an inherent risk when it comes to how brands manage their Facebook, Twitter, and Instagram accounts. 1 : Cybercrime Businesses should always be very aware of the threat of cybercriminals, and social media also poses very real cyber-security risks.

Herjavec Group
SEPTEMBER 23, 2021
Not using easy to decrypt passwords or the same password for multiple accounts. Penetration Testing. A network penetration test aims to find weaknesses in the defense capabilities before an adversary can take advantage through a combination of security expertise and best-of-breed technology.

CyberSecurity Insiders
SEPTEMBER 21, 2021
In the world of cybercrime, a flawed application is a potential goldmine for them, but an onramp to disaster for most organizations. Compromised accounts due to password reuse, credential stuffing attacks, and compromised email accounts remain major problems globally. This blog was written by a guest blogger. A vulnerable state.

Security Affairs
AUGUST 2, 2018
Three members of the cybercrime group tracked as FIN7 and Carbanak have been indicted and charged with 26 felony counts. Three members of the notorious cybercrime gang known as FIN7 and Carbanak have been indicted and charged with 26 felony counts of conspiracy, wire fraud, computer hacking, access device fraud and aggravated identity theft.

SecureList
NOVEMBER 22, 2022
Unlike common stealers, this malware gathered data that can be used to identify the victims, such as browsing histories, social networking account IDs and Wi-Fi networks. These are attractive aspects that cybercrime groups will be unable to resist. One of the most striking new stealers has been OnionPoison.

Security Affairs
MARCH 17, 2021
According to the report issued by the CERT-FR, operators behind the Pysa ransomware launched brute-force attacks against management consoles and Active Directory accounts. Once compromised the target network, attackers attempt to exfiltrate the company’s accounts and passwords database. newversion file extension instead of .
Security Affairs
AUGUST 8, 2021
Figure 6 – Graph of compromised bank card data distribution by country According to the findings, 77% of the cards in the batch were debit cards, 23% were credit cards, and the rest accounted for less than 1 percent. Another 1% of the cards belonged to American Express, the rest of the systems accounted for less than a percent.

eSecurity Planet
DECEMBER 3, 2021
Here are the top Twitter accounts to follow for the latest commentary, research, and much-needed humor in the ever-evolving information security space. Brian Krebs is an independent investigative reporter known for his coverage of technology, malware , data breaches , and cybercrime developments. Brian Krebs | @briankrebs.

SecureList
DECEMBER 14, 2021
We determined that Owowa is specifically targeting OWA applications of Exchange servers because its code is purposely ignoring requests from OWA-specific monitoring of account names that start with the HealthMailbox string. Notably, it shares offensive tools, such as Cobalt Strike and Core Impact: s3crt Keybase account.

Security Affairs
FEBRUARY 9, 2019
From Mirai source code the Cayosin was taken the table scheme to hide strings used by the botnet to hack the login credential of the vulnerable telnet accounts for known IOT devices, along with other Mirai botnet functionalities. You can learn more about these tools by following the various Instagram accounts of the crew.

Security Boulevard
MARCH 31, 2021
conduct employee phishing tests. conduct penetration testing. Cybercrime to cost over $10 Trillion by 2025. FBI Internet Crime Report 2020: Cybercrime Skyrocketed, with Email Compromise Accounting for 43% of Losses. review Active Directory password policy. implement offline storage and tape-based backup.
SecureWorld News
MARCH 1, 2023
During penetration tests, security professionals use harmless decoy elements that allow them to keep a record of link hits or instances of opening attachments. The former typically results in visiting a credential phishing page, and the latter mostly triggers rogue macros within a Microsoft Office document.

Security Affairs
NOVEMBER 6, 2018
Based on the risk score, CryptoIns experts have calculated insurance rates for cryptocurrency exchange users who can now insure their accounts against cyber threats. A Group-IB report “ 2018 Cryptocurrency Exchanges: Analysis of User Account Leaks ” shows a steady increase in incidents involving compromised user accounts.

Jane Frankland
APRIL 28, 2022
Just like yesterday, all tech is hackable and cybercriminals penetrate 93% of company networks in less than 2-days. Today they account for only 25% of the cybersecurity workforce, a 1% improvement in the last two years. But it’s not all doom and gloom.

IT Security Guru
JANUARY 12, 2021
Here’s a brief overlook of the kind of specializations you can earn if you decide to take a plunge into cybersecurity: Penetration testing (or, pentesting). As a CBO at Ampcus Cyber, Viral overlooks the go-to-market Strategy, channel partner programs, strategic accounts, and customer relationship management. Secure DevOps.

Malwarebytes
MAY 31, 2022
Like ransomware groups, they also have channels in place—a Telegram account and a leak site—to communicate with victims, journalists, and those who want to track their activities. After stealing data from targets, they offer to delete it and then provide a full report on what vulnerabilities they exploited and how.

Jane Frankland
JULY 13, 2020
Qualifications certainly don’t make a hacker, consultant or practitioner and there are so many positions within the cybersecurity ecosystem that are available to you—from cryptographics, mobile device forensic analysis and incident response to penetration testing (hacking), endpoint security, or security awareness, and so on.

Krebs on Security
OCTOBER 8, 2020
There’s an old adage in information security: “Every company gets penetration tested, whether or not they pay someone for the pleasure.” ” Many organizations that do hire professionals to test their network security posture unfortunately tend to focus on fixing vulnerabilities hackers could use to break in.
SecureList
MAY 8, 2024
Another three were: compromise of internet-facing applications, which accounted for 50% of all ransomware attacks; compromised credentials (40%), of which 15% were obtained as a result of brute force attacks; and phishing. Conduct regular penetration tests and vulnerability scanning to identify and address vulnerabilities promptly.

SC Magazine
MARCH 10, 2021
“When an attacker gains access to surveillance cameras, the amount of knowledge which stands to be gained could be vast and poses a very real physical security threat,” said James Smith, principal security consultant and head of penetration testing at Bridewell Consulting. What did Verkada do wrong?

CyberSecurity Insiders
APRIL 11, 2023
By Chinatu Uzuegbu, CISSP, CEO/Managing Cyber Security Consultant at RoseTech CyberCrime Solutions Ltd. For example, the organization would enroll every human and non-human identity considering the identification process first, then authentication second, authorization third and accountability last.
Security Boulevard
OCTOBER 2, 2023
Business Email Compromise (BEC), a type of phishing attack, results in the greatest financial losses of any cybercrime. Often used to compromise executive and privileged accounts. In 2021 alone, estimated adjusted losses from BEC totaled $2.4 billion USD globally. URL spoofing and typosquatting techniques bypass casual inspection.

Centraleyes
DECEMBER 8, 2023
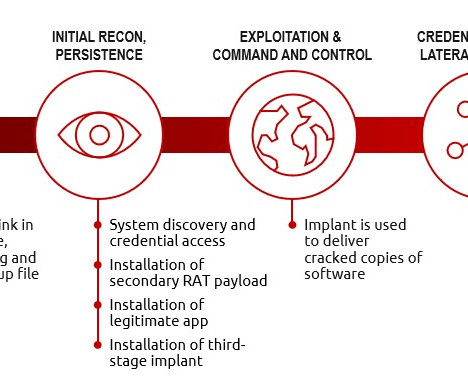
Passive, reactive cyber defenses have long struggled to keep up with the evolving cybercrime market. In addition to threat modeling, ATT&CK also provides frameworks for penetration testing, cybersecurity, and defense development. Lateral movement: The threat actor moves between compromised systems and accounts.

SecureWorld News
SEPTEMBER 15, 2023
Here are just some of the types of cybercrime that could jeopardize the safety of digital media assets: External attacks : Cybercriminals may attempt to breach company networks or systems to steal sensitive assets through phishing emails, brute force, or DDoS attacks.

Security Affairs
SEPTEMBER 5, 2018
For more than two years, there was not a single sign of Silence that would enable to identify them as an independent cybercrime group. He has experience in penetration testing, which means he can easily find his way around banking infrastructure. Like most cybercrime groups, Silence uses phishing emails.
Security Affairs
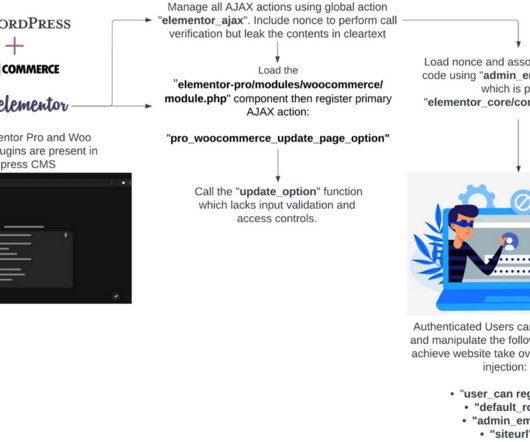
JUNE 14, 2023
The Elementor Pro and WooCommerce compromise path allows authenticated users to modify WordPress configurations to create administrator accounts or inject URL redirects into website pages or posts. Proceed at your own risk! com/wp-admin/?wc-ajax=1”. wc-ajax=1”. Remove all unnecessary or unused software.

CyberSecurity Insiders
SEPTEMBER 21, 2021
Establish a unique password for each account. Remember to use Multi-Factor Authentication (MFA) on accounts wherever it is available, especially on accounts that have financial information such as online banking, credit card, and retirement accounts. Consider using a password manager if you haven’t in the past.

Herjavec Group
AUGUST 26, 2021
We can learn a lot from the cybercrime of the past…the history of cybercrime is a glimpse into what we can expect in the future. In the past 18 months, we’ve experienced the beginning of an era that has seen cybersecurity and cybercrime at the center of it all. Dateline Cybercrime . Robert Herjavec.

SecureList
OCTOBER 26, 2021
The first accounts of its activity date back to March last year, in which archives carrying COVID-related decoy file names that contained a malicious executable were described in a tweet by MalwareHunterTeam. It is mainly known for being a proprietary commercial penetration testing toolkit officially designed for red team engagements.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content