Security Affairs newsletter Round 453 by Pierluigi Paganini – INTERNATIONAL EDITION
Security Affairs
JANUARY 7, 2024
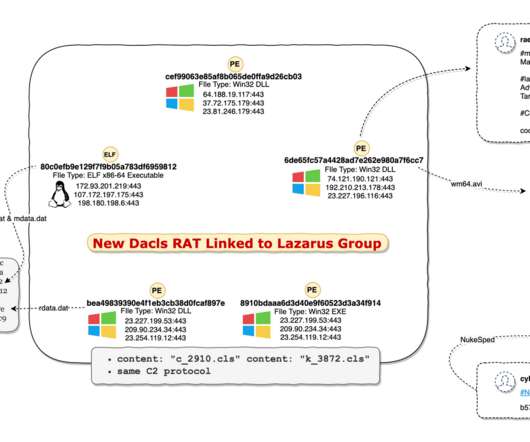
Experts spotted a new macOS Backdoor named SpectralBlur linked to North Korea Merck settles with insurers regarding a $1.4
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
Security Affairs
JANUARY 7, 2024
Experts spotted a new macOS Backdoor named SpectralBlur linked to North Korea Merck settles with insurers regarding a $1.4

Krebs on Security
OCTOBER 28, 2020
In August, Gunnebo said it had successfully thwarted a ransomware attack, but this week it emerged that the intruders stole and published online tens of thousands of sensitive documents — including schematics of client bank vaults and surveillance systems.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
SEPTEMBER 2, 2019
Login details of more than 36 million Poshmark accounts are available for sale in the cybercrime underground. Earlier in August, Poshmark , a social commerce marketplace where people in the United States can buy and sell new or used clothing, shoes, and accessories, disclosed a data breach that took place in May 2018.
Security Affairs
DECEMBER 18, 2019
Lab test provider LifeLabs has disclosed a data breach that exposed personal information for up to 15 million Canadians. LifeLabs notified its customers via letter, exposed data includes names, contact information, health card numbers, and for approximately 85,000 customers their lab test results. ” said Brown.

Approachable Cyber Threats
MAY 30, 2023
Category Awareness, Cybersecurity Fundamentals, Physical Security Risk Level You may have thought that hackers wore black suits and rappelled off the roof to hack a company, but that only exists in Hollywood. In real life, human error remains one of the leading causes of cybersecurity breaches.
Security Affairs
APRIL 16, 2023
hacking tools and electronics A new round of the weekly SecurityAffairs newsletter arrived! hacking tools and electronics A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box.
Security Affairs
MAY 14, 2023
ransom Dragon Breath APT uses double-dip DLL sideloading strategy International Press Cybercrime San Bernardino County pays $1.1-million ransom Dragon Breath APT uses double-dip DLL sideloading strategy International Press Cybercrime San Bernardino County pays $1.1-million
Security Affairs
MARCH 26, 2023
NCA infiltrates the cybercriminal underground with fake DDoS-for-hire sites Pwn2Own Vancouver 2023 awarded $1,035,000 and a Tesla for 27 0-days CISA announced the Pre-Ransomware Notifications initiative China-linked hackers target telecommunication providers in the Middle East City of Toronto is one of the victims hacked by Clop gang using GoAnywhere (..)
Security Affairs
MAY 6, 2023
Twitter confirmed that a security incident publicly exposed Circle tweets FBI seized other domains used by the shadow eBook library Z-Library WordPress Advanced Custom Fields plugin XSS exposes +2M sites to attacks Fortinet fixed two severe issues in FortiADC and FortiOS Pro-Russia group NoName took down multiple France sites, including the French (..)

Security Affairs
SEPTEMBER 3, 2022
Google rolled out emergency fixes to address actively exploited Chrome zero-day Samsung discloses a second data breach this year The Prynt Stealer malware contains a secret backdoor. users China-linked APT40 used ScanBox Framework in a long-running espionage campaign Russian streaming platform Start discloses a data breach impacting 7.5M
Security Affairs
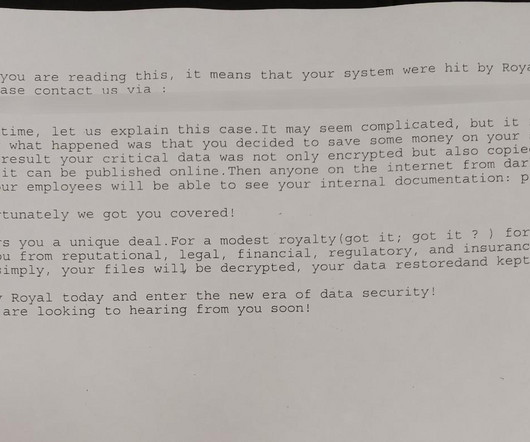
SEPTEMBER 23, 2023
The City of Dallas revealed that the Royal ransomware gang that hit the city system in May used a stolen account. The Royal group began reconnaissance activity in April 2023, and the analysis of system log data dates the beginning of the surveillance operations on April 7, 2023. ” reads the report.

Security Affairs
AUGUST 7, 2022
Greek intelligence service used surveillance malware to spy on a journalist, Reuters reports Slack resets passwords for about 0.5% of its users due to the exposure of salted password hashes Twitter confirms zero-day used to access data of 5.4 SecurityAffairs – hacking, newsletter). Pierluigi Paganini.
Security Affairs
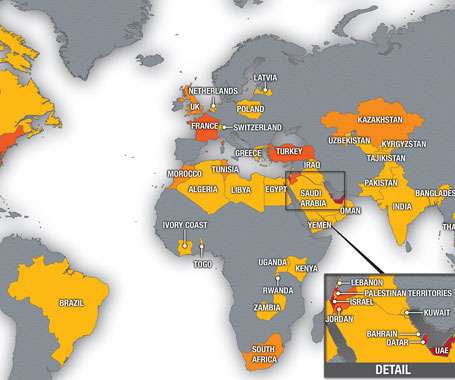
JULY 19, 2021
Pegasus Project investigation into the leak of 50,000 phone numbers of potential surveillance targets revealed the abuse of NSO Group’s spyware. Pegasus Project is the name of a large-scale investigation into the leak of 50,000 phone numbers of potential surveillance targets that revealed the abuse of NSO Group’s spyware.
Security Affairs
SEPTEMBER 24, 2023
0-days exploited by commercial surveillance vendor in Egypt PREDATOR IN THE WIRES OilRig’s Outer Space and Juicy Mix: Same ol’ rig, new drill pipes Cybersecurity Apple and Google Are Introducing New Ways to Defeat Cell Site Simulators, But Is it Enough?

Approachable Cyber Threats
MAY 30, 2023
Category Awareness, Cybersecurity Fundamentals, Physical Security Risk Level You may have thought that hackers wore black suits and rappelled off the roof to hack a company, but that only exists in Hollywood. In real life, human error remains one of the leading causes of cybersecurity breaches.

Security Affairs
FEBRUARY 13, 2022
to replace Chinese equipment Hackers breached a server of National Games of China days before the event Russian Gamaredon APT is targeting Ukraine since October Israeli surveillance firm QuaDream emerges from the dark Argo CD flaw could allow stealing sensitive data from Kubernetes Apps. SecurityAffairs – hacking, newsletter).

Security Affairs
SEPTEMBER 6, 2020
Is the Belarusian government behind the surveillance Android app banned by Google? The Twitter account of Indian Prime Minister Modi was hacked Evilnum APT used Python-based RAT PyVil in recent attacks SunCrypt Ransomware behind North Carolina school district data breach U.S. Pierluigi Paganini.

Webroot
FEBRUARY 19, 2021
For most small businesses, the chances of falling prey to a long-term covert surveillance operation by well-resourced, likely state-backed actors are slim. This shows that stealthily surveilling a network is not a tactic exclusive to highly sophisticated threat actors targeting enterprise businesses.

Security Affairs
AUGUST 4, 2019
Crooks used rare Steganography technique to hack fully patched websites in Latin America. Jessica Alba ‘s Twitter account hacked, it posted racist and homophobic messages. Over 23 million stolen payment card data traded on the Dark Web in H1 2019. LAPD data breach exposes personal info of thousands of officers.

Security Affairs
SEPTEMBER 1, 2019
Experts uncovered a hacking campaign targeting several WordPress Plugins. Hostinger disclosed a data breach that affects 14 Million customers. Imperva data Breach: WAF customers data exposed. White hat hacker demonstrated how to hack a million Instagram accounts. Remove it now from your phone!

Security Affairs
JULY 24, 2022
ransom and sued its insurance firm for refusing to cover this payment Crooks stole $375k from Premint NFT, it is one of the biggest NFT hacks ever Google is going to remove App Permissions List from the Play Store Security Affairs newsletter Round 374 by Pierluigi Paganini APT groups target journalists and media organizations since 2021.
Security Affairs
APRIL 23, 2023
Abandoned Eval PHP WordPress plugin abused to backdoor websites CISA adds MinIO, PaperCut, and Chrome bugs to its Known Exploited Vulnerabilities catalog At least 2 critical infrastructure orgs breached by North Korea-linked hackers behind 3CX attack American Bar Association (ABA) suffered a data breach,1.4

BH Consulting
DECEMBER 11, 2023
These practices can lead to account compromise, or enabling unauthorised users to access sensitive data and escalate privileges. The report recommends steps to prevent breaches, such as making MFA mandatory, turning on features that make storage buckets private, and discovering any publicly exposed workloads.

Adam Levin
APRIL 8, 2019
A week after it landed with a curious (and most likely spurious) thud, Zuckerberg’s announcement about a new tack on consumer privacy still has the feel of an unexpected message from some parallel universe where surveillance (commercial and/or spycraft) isn’t the new normal. This article originally appeared on Inc.com.

Security Affairs
OCTOBER 14, 2018
Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. . · GAO report reveals new Pentagon weapon systems vulnerable to hack. · Group-IB: $49.4 Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->. Copyright (C) 2014-2015 Media.net Advertising FZ-LLC All Rights Reserved -->.

Malwarebytes
NOVEMBER 2, 2023
When asked how they feel about the statement “I think monitoring apps and tools are an invasion of privacy,” fewer Gen Z respondents disagreed than non-Gen Z—18 percent compared to 24 percent—revealing, perhaps, that fewer members of this younger generation will ever stand up against this type of intimate surveillance.

Security Affairs
SEPTEMBER 30, 2018
Copyright (C) 2014 Media.net Advertising FZ-LLC All Rights Reserved -->. . · Firefox DoS issue crashes the browser and sometimes the Windows OS. · Akamai Report: Credential stuffing attacks are a growing threat. · Bitcoin Core Team fixes a critical DDoS flaw in wallet software. · SHEIN Data breach affected 6.42

Identity IQ
JANUARY 17, 2023
These are generally not considered privacy data, but when coupled with an element like your identity document, it becomes private. Other types of data that you should consider private include: Your bank account number and card details. Login information for online accounts you have. Why Is Data Privacy Important?

SC Magazine
MARCH 10, 2021
A hacking collective compromised roughly 150,000 internet-connected surveillance cameras from Verkada, Inc., Hacktivist Tillie Kottmann is reportedly among those asserting responsibility for the incident, telling Bloomberg that their act helped expose the security holes of modern-day surveillance platforms.

Security Affairs
NOVEMBER 19, 2019
Distributed Denial of Secrets didn’t hacked the systems at the Cayman National , the group only released information that were stolen by the popular hacktivist “ Phineas Fisher.” ” Phineas Fisher is the same hacker that breached the surveillance firms HackingTeam and Gamma Group.

Security Affairs
JULY 19, 2019
According to a court complaint , the stolen data include source codes developed by the NSA to its hacking campaigns against foreign governments. SecurityAffairs – NSA contractor, data breach). The post Former NSA contractor sentenced to 9 years for stealing classified data appeared first on Security Affairs.

Security Affairs
MARCH 10, 2019
The unprotected MongoDB install was discovered by security experts Ran Locar and Noam Rotem , the database contained cell phone numbers, App registration data (full name, email, Viber account, gender, etc.), The availability of GPS data for some users could allow attackers to track them. SecurityAffairs – Delil, hacking).
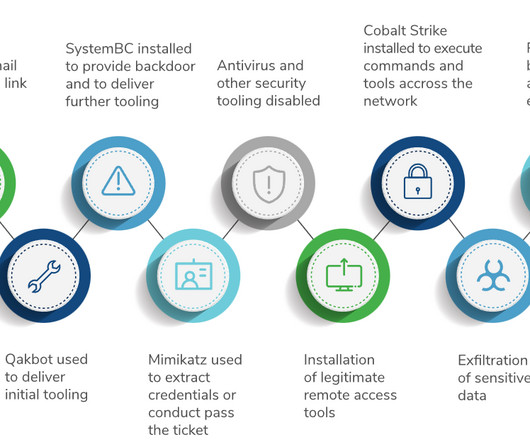
DoublePulsar
APRIL 20, 2023
Russian hackers exfiltrated data from from Capita over a week before outage Capita have finally admitted a data breach , but still do not think they need to disclose key details of the incident to customers, regulators, impacted parties and investors. Go in hard. If you see alerts for Cobalt Strike, isolate the PC. Go in hard.

Security Affairs
DECEMBER 29, 2019
According to Twelve Security , the exposed data includes: User name and email of those who purchased cameras and then connected them to their home 24% of the 2.4 Experts from Twelve Security claimed they found API tokens that would have allowed hackers to access Wyze user accounts from any iOS or Android device. ” continues Wyze.

SC Magazine
JULY 2, 2021
About 80 million company records were accessed in one of the largest health care data breaches. Accordingly, you can expect to continue to see providers give fairly vague breach notifications.” Other major settlements stemmed from covered entities that failed to provide adequate breach notification.

Spinone
JANUARY 5, 2021
This makes the likelihood of your cloud data getting damaged by a natural disaster like a fire or flood is extremely low. If something happens with one warehouse that con Also, unlike most on-site solutions, these places are guaranteed to 24/7 surveillance and armed security guards. Event logging and workload audit. Phishing emails.

SecureList
FEBRUARY 26, 2021
The Coalition Against Stalkerware warns that stalkerware “may facilitate intimate partner surveillance, harassment, abuse, stalking, and/or violence.” They still need physical access to the phone to jailbreak it, so iPhone users who fear surveillance should always keep an eye on their device.

Spinone
NOVEMBER 21, 2019
To train your employees and protect company data from human mistakes and, therefore, costly data breaches; 3. 3 Basic Cyber Security Training Courses For Everybody The best cyber security courses online listed below contain the information everybody must know to keep their data safe in the high-risk online environment.
Security Affairs
FEBRUARY 11, 2024
Gov imposes visa restrictions on individuals misusing Commercial Spyware HPE is investigating claims of a new security breach Experts warn of a surge of attacks targeting Ivanti SSRF flaw How to hack the Airbus NAVBLUE Flysmart+ Manager Crooks stole $25.5
Security Affairs
APRIL 2, 2023
Nominate here: [link] Follow me on Twitter: @securityaffairs and Facebook and Mastodon Pierluigi Paganini ( SecurityAffairs – hacking, newsletter) The post Security Affairs newsletter Round 413 by Pierluigi Paganini – International edition appeared first on Security Affairs.

SecureWorld News
NOVEMBER 30, 2023
Consequences of browser-focused cybercrime Hackers are able to utilize browser vulnerabilities to install malware and spyware on devices, steal login credentials for other services, extract sensitive user data, and maintain persistence inside systems. Follow SecureWorld News for more stories related to cybersecurity.
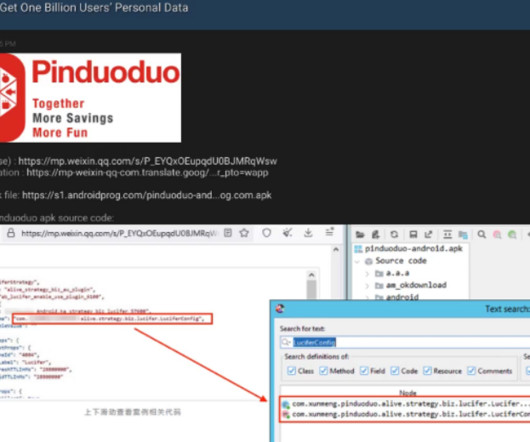
Krebs on Security
MARCH 22, 2023
Google said it believes the exploit chain for Samsung devices belonged to a “commercial surveillance vendor,” without elaborating further. The highly technical writeup also did not name the malicious app in question. That Weibo post has since been deleted.
Security Affairs
NOVEMBER 26, 2023
Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. million patients in the U.S. million patients in the U.S.

eSecurity Planet
OCTOBER 26, 2021
“This recent activity is another indicator that Russia is trying to gain long-term, systematic access to a variety of points in the technology supply chain and establish a mechanism for surveilling – now or in the future – targets of interest to the Russian government,” Burt wrote. Old Attack Techniques Resurface.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content