New S1deload Malware Hijacking Users' Social Media Accounts and Mining Cryptocurrency
The Hacker News
FEBRUARY 23, 2023
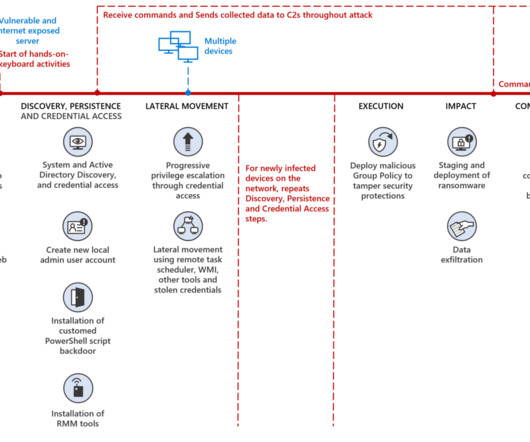
An active malware campaign has set its sights on Facebook and YouTube users by leveraging a new information stealer to hijack the accounts and abuse the systems' resources to mine cryptocurrency. Once infected, S1deload Stealer steals














































Let's personalize your content