Hermit spyware is deployed with the help of a victim’s ISP
Malwarebytes
JUNE 29, 2022
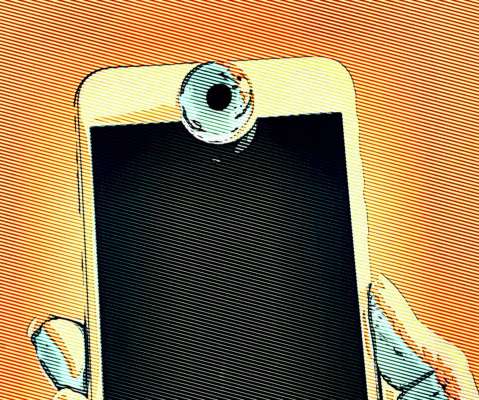
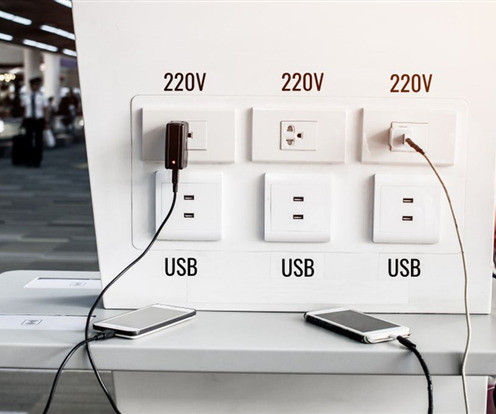
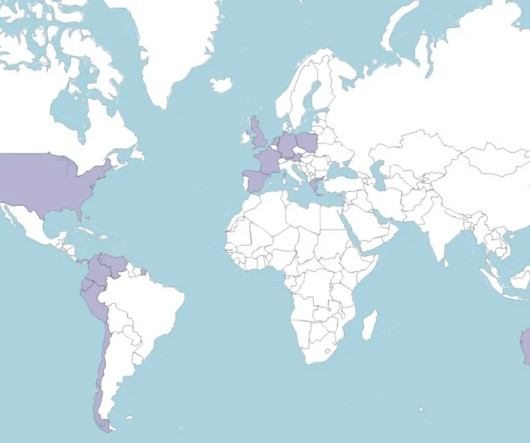
Google’s Threat Analysis Group (TAG) has revealed a sophisticated spyware activity involving ISPs (internet service providers) aiding in downloading powerful commercial spyware onto users’ mobile devices. The spyware, dubbed Hermit, is reported to have government clients much like Pegasus.



























Let's personalize your content