Penetration Testing vs. Vulnerability Testing
eSecurity Planet
FEBRUARY 25, 2022
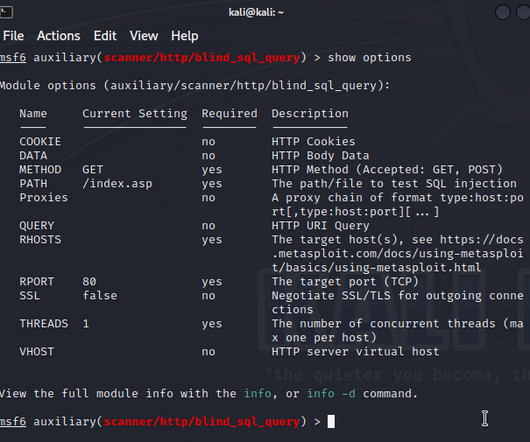
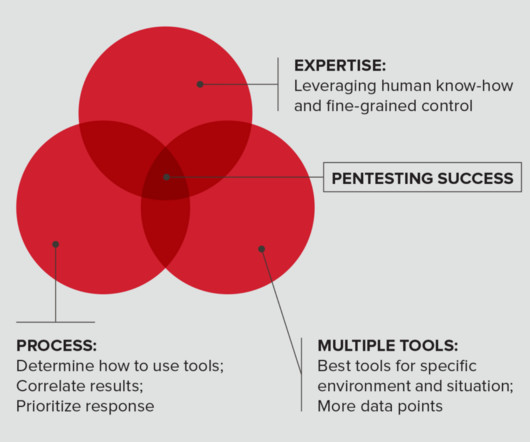
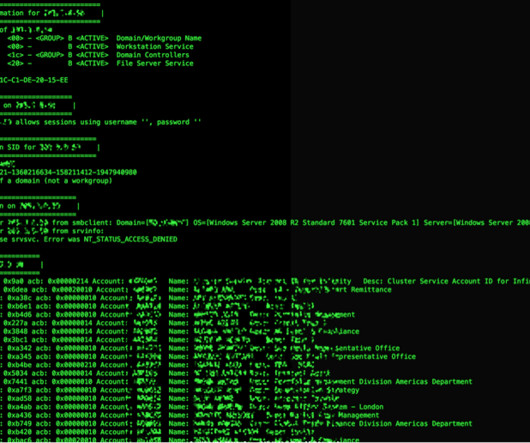
Many cybersecurity audits now ask whether penetration testing is conducted and how vulnerabilities are detected and tracked. These questions ask IT teams to consider how frequently security is tested from the outside via penetration testing and from the inside via vulnerability testing. File servers.






































Let's personalize your content