News Alert: i2Coalition launches ‘VPN Trust Initiative’ to promote VPN operators’ best practices
The Last Watchdog
SEPTEMBER 26, 2023
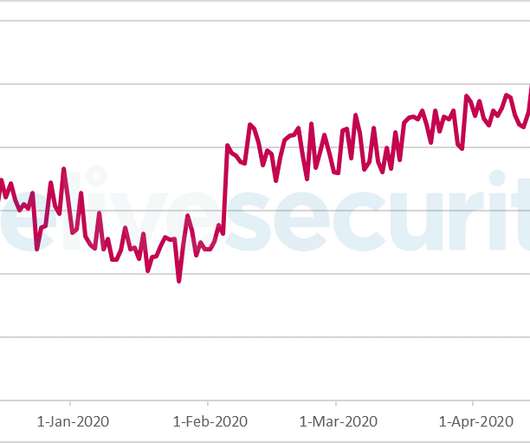
26, 2023 — The Internet Infrastructure Coalition (i2Coalition) launched the VPN Trust Initiative (VTI) in 2020 to establish a baseline for how virtual private network (VPN) providers should operate. Advertising Practices: Given the complexity and different use cases for VPNs, claims must not mislead.












































Let's personalize your content