GUEST ESSAY: 7 tips for protecting investor data when it comes to alternative asset trading
The Last Watchdog
JULY 11, 2023
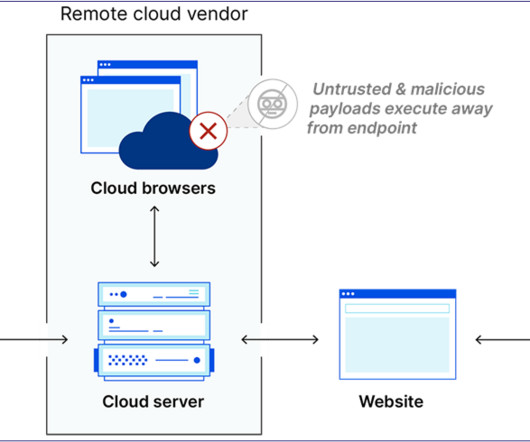
•Employ real-time antivirus scanning. By using real-time antivirus scanning to detect and neutralize security risks as they enter the trading system, threats can be quickly identified and eliminated. This includes scanning all materials, such as investor onboarding documents and communication. Implement strong data encryption.













































Let's personalize your content