How is information stored in cloud secure from hacks
CyberSecurity Insiders
MAY 14, 2023
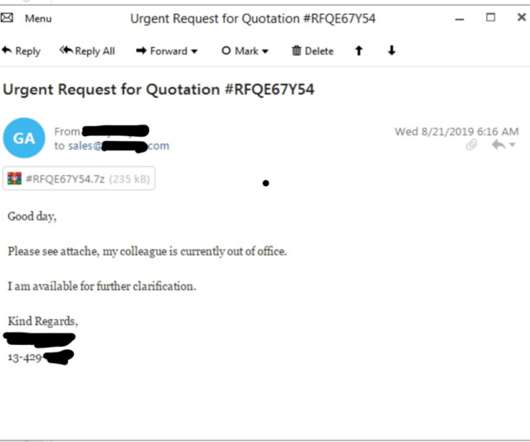
Cloud providers implement access controls through authentication and authorization. Authentication is the process of verifying a user’s identity, while authorization is the process of granting or denying access based on the user’s identity and privileges. Antivirus software scans files for known viruses and malware.

















































Let's personalize your content