Chinese Antivirus Firm Was Part of APT41 ‘Supply Chain’ Attack
Krebs on Security
SEPTEMBER 17, 2020
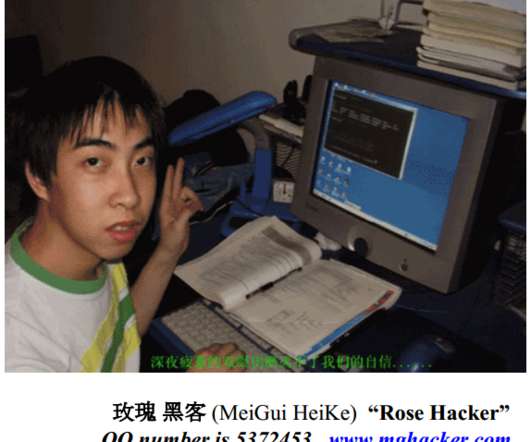
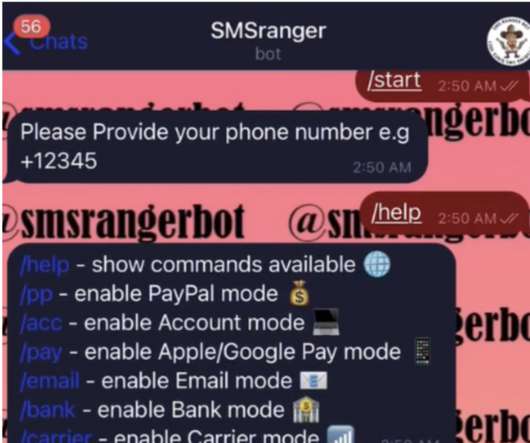
One of the alleged hackers was first profiled here in 2012 as the owner of a Chinese antivirus firm. ” The government alleges the group monetized its illicit access by deploying ransomware and “ cryptojacking ” tools (using compromised systems to mine cryptocurrencies like Bitcoin). Image: FBI.





































Let's personalize your content