3 reasons even Chromebook™ devices benefit from added security
Webroot
OCTOBER 25, 2021
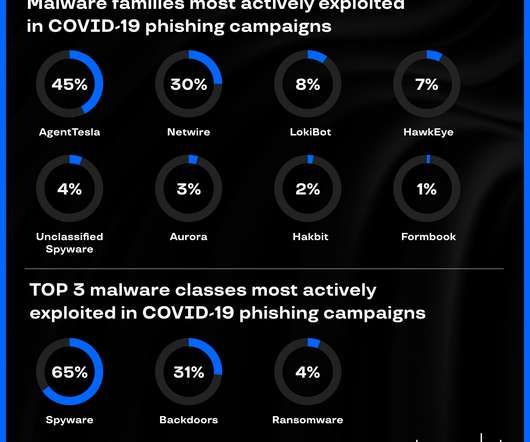
In 2020, phishing scams spiked by 510 percent between January and February alone. To combat phishing scams, it helps to have filters that can proactively alert users if there’s a high chance that a form field or website is likely to steal credentials. Web-borne malware remains widespread.




























Let's personalize your content