Multiple Brocade SANnav SAN Management SW flaws allow device compromise
Security Affairs
APRIL 28, 2024
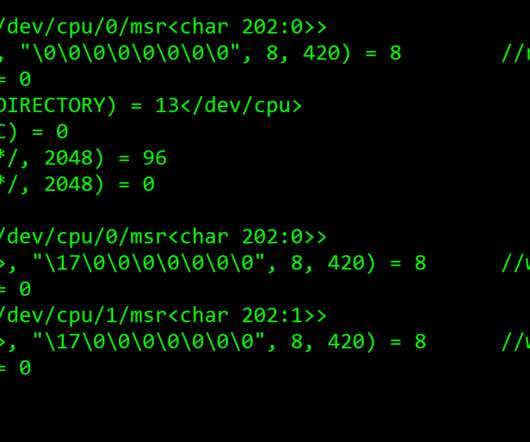
The following vulnerabilities, discovered by the security researcher Pierre Barre , impact all versions up to 2.3.0 The following vulnerabilities, discovered by the security researcher Pierre Barre , impact all versions up to 2.3.0































Let's personalize your content