GUEST ESSAY: In pursuit of smarter cybersecurity — to overcome complex risks and grow revenue
The Last Watchdog
JANUARY 8, 2023
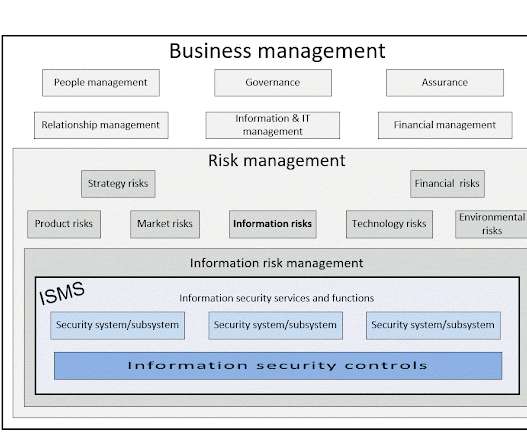
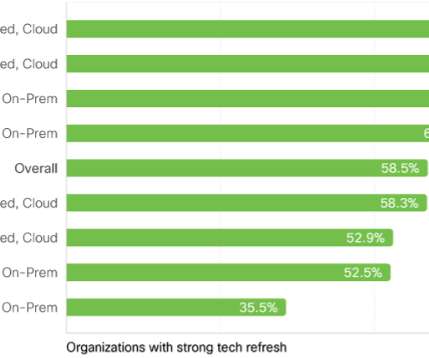
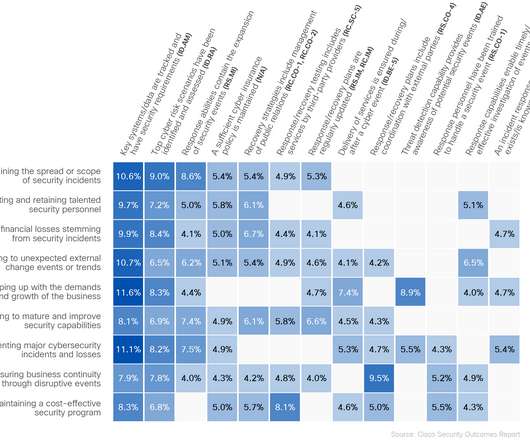
Smarter security to me broadly refers to relentlessly focusing on fundamentals while maturing the program, making sure your risk posture aligns with your business strategy. Business initiatives demand faster, more efficient outcomes and technology responds. Complexity challenge. Managed solutions can help.










































Let's personalize your content