Architecture Matters When it Comes to SSE
CyberSecurity Insiders
MAY 17, 2023
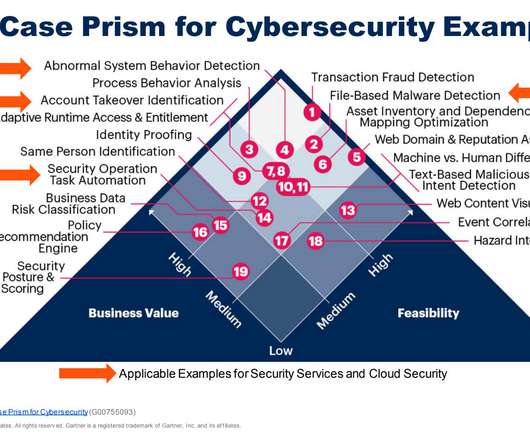
While the Gartner MQ provides a plethora of helpful information to the network and security leader, one area I found needing improvement was how these solutions are architected. ” Or said another way, “architecture matters”. By 2026, SaaS workloads will dominate the enterprise software market.













































Let's personalize your content